Attify Badge IoT Hacking Device:MAERehim
Summary
This documentation describes basic information about the Attify Badge. General functionalities / hardfacts about the Badge and a set up example, where the Badge is used to exploit an IoT Device.
Introduction
Attify Badge is a dedicated hardware security assessment utility developed by Attify that enables communication between a PC and an embedded device over various hardware communication protocols. The Attify Badge uses an FTDI chip that supports a variety of communication protocols and standards including UART, SPI, I2C, 1-Wire and JTAG. This allows an interaction with any IoT/embedded device that has one or more hardware communication ports. It supports both 3.3V and 5V, making it suitable for a wide range of target devices.
Requirements
Devices: Attify Badge, IoT Device
Operating system: Ubuntu OS
Software: Attify Badge Tool
Supported Exploitation Interfaces
Universal Asynchronous Receiver Transmitter (UART)
Serial Peripheral Interface (SPI)
Joint Test Action Group (JTAG)
Inter-Integrated Circuit (I²C)
General Purpose Input/Output (GPIO)
Exploit by UART
Register the external USB device connected to the system and add it to the combo box at the top left of the user interface.
Select the USB port to which the device is connected and the baud rate to be used.
Once you have selected the desired baud rate, press Enter to connect to the device. the data received from the UART device will be displayed in a black console window. You can use the input fields below it to interact with the device. In the combo box at the bottom right, you can select the line termination for each line you want to send to the device.
Exploit by SPI
Allows users to detect, read, write and erase SPI based memory of the target device connected to the Attify Badge.
Select the desired operation from the drop-down menu.
For read/write commands, enter the path of the file where the data will be saved or read. An example of a path is ~/files/firmware.bin.
Exploit by JTAG
Select the appropriate configuration file for the target device. (Custom configuration files can be placed directly in the cfg/ directory.)
Click "Start OpenOCD Server". Then you will see the message "Initializing OpenOCD Server in the background".
Click on the "Connect to OpenOCD Server" button to connect to the OpenOCD Server. This will launch a new terminal window with a Telnet session connected to the OpenOCD Server.
For further analysis (for example, to find and exploit firmware vulnerabilities). Enter the path of the sprite file in the path edit box and click "Run GDB" (you will need the appropriate elf file). This will start a gdb session for the tool to analyze.
Exploit by I²C
The I2C module can be used to find I2C devices and to read, write and erase the contents of I2C EEPROMs connected to the badge.
To do so, simply select the action you want from the drop-down menu, enter the file path if necessary, and click the "Run" button.
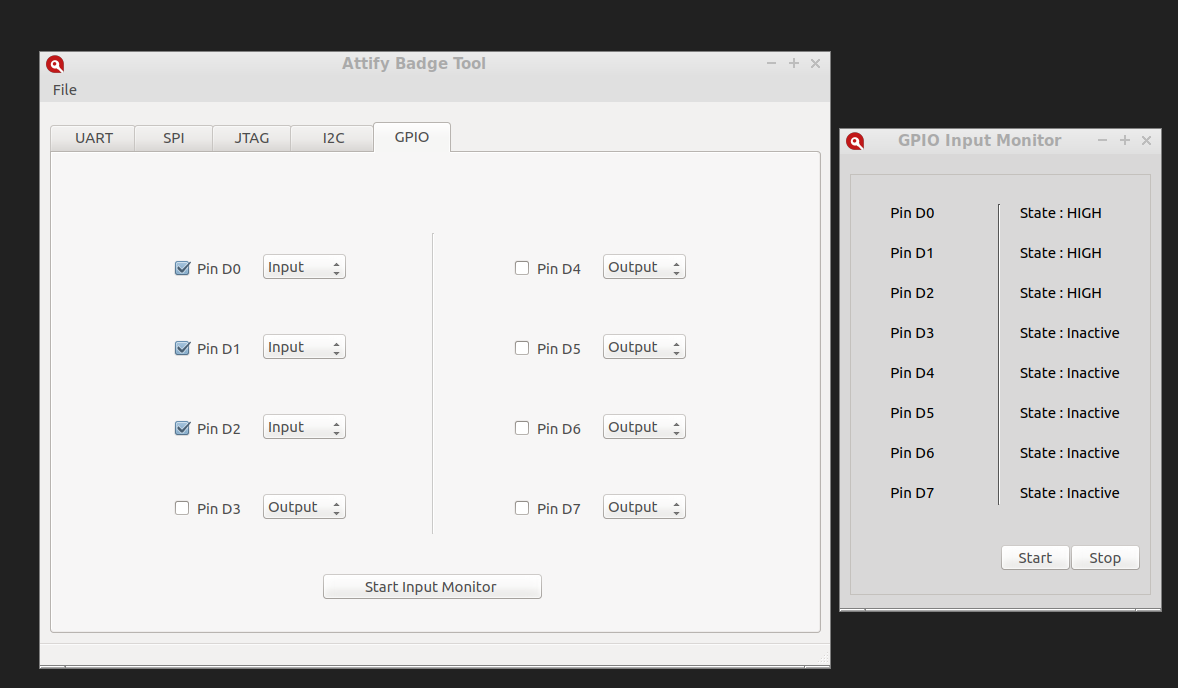
Exploit by GPIO
Output Mode: Selecting the check box next to each terminal will change the status of that terminal to "High", and unchecking the box will change the status of that terminal to "Low".
Input Mode If you want to use the pin in input mode, change the mode of the desired pin to input mode and check the box to enable the pin.
Click on the "Start input monitoring" button to start the input monitoring control.
Click the "Start" button in the "Input monitoring" widget to start monitoring the input of the selected pin.
References
https://blog.attify.com/hack-iot-devices-embedded-exploitation/