Bandit - Static Code Analyss for Python Code
Summary
This documentation shows how to install and use Bandit, a static analysis tool for C/C++ source code. This Tool can be used to identify possible Security risks categorized in three different Severity Levels (Low, Medium, High).
Requirements
- Python Version 3.7 or higher
- Python Package: bandit
Installation and Usage
Bandit can be easily installed via the pip install command. Furthermore it can be found on PyPi for manual installation. If you want to install it manually please follow the attached References.
pip install bandit
For executing the analysis just enter die File or Folder you want to be analyzed in a Python Terminal
bandit <File/Folder>
Example
This example is using the Bandit example files from their github (https://github.com/PyCQA/bandit). For this case we are using the imports.py Example with the following Source Code:
import sqlalchemy
# bad
query = "SELECT * FROM foo WHERE id = '%s'" % identifier
query = "INSERT INTO foo VALUES ('a', 'b', '%s')" % value
query = "DELETE FROM foo WHERE id = '%s'" % identifier
query = "UPDATE foo SET value = 'b' WHERE id = '%s'" % identifier
query = """WITH cte AS (SELECT x FROM foo)
SELECT x FROM cte WHERE x = '%s'""" % identifier
# bad alternate forms
query = "SELECT * FROM foo WHERE id = '" + identifier + "'"
query = "SELECT * FROM foo WHERE id = '{}'".format(identifier)
# bad
cur.execute("SELECT * FROM foo WHERE id = '%s'" % identifier)
cur.execute("INSERT INTO foo VALUES ('a', 'b', '%s')" % value)
cur.execute("DELETE FROM foo WHERE id = '%s'" % identifier)
cur.execute("UPDATE foo SET value = 'b' WHERE id = '%s'" % identifier)
# bad alternate forms
cur.execute("SELECT * FROM foo WHERE id = '" + identifier + "'")
cur.execute("SELECT * FROM foo WHERE id = '{}'".format(identifier))
# good
cur.execute("SELECT * FROM foo WHERE id = '%s'", identifier)
cur.execute("INSERT INTO foo VALUES ('a', 'b', '%s')", value)
cur.execute("DELETE FROM foo WHERE id = '%s'", identifier)
cur.execute("UPDATE foo SET value = 'b' WHERE id = '%s'", identifier)
# bug: https://bugs.launchpad.net/bandit/+bug/1479625
def a():
def b():
pass
return b
a()("SELECT %s FROM foo" % val)
# real world false positives
choices=[('server_list', _("Select from active instances"))]
print("delete from the cache as the first argument")
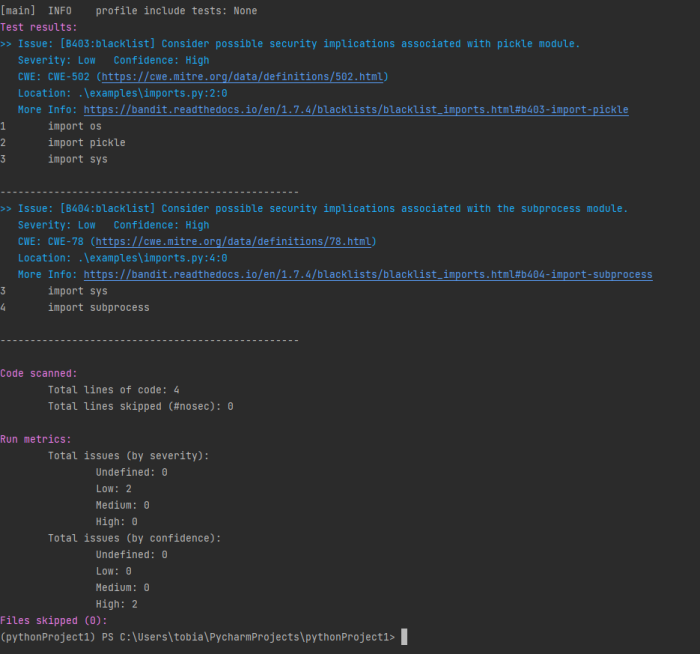
After executing bandit on the File you get the following output
Bandit has found two Low Severity Issues regarding Problems with the imported Packages. A detailed information is given for every Issue found. It also shows the CWE Number associated with it.