ConBee ZigBee USB Gateway: Usage
Summary
This is a description of how to set up and use a ConBee ZigBee USB Gateway USB stick to sniff out keys of ZigBee end point devices in smart home networks.
Requirements
Operating system:
- Ubuntu 18.04
Applications:
- Wireshark
- ZShark (Interface between sniffer and Wireshark, available [here]
- Smart Home Management App, e.g. Philips Hue for Android, available in the [Google Play Store]
Network traffic generating devices, e.g.
- Philips Hue Bridge
- Philips Hue White LED
Sniffing tool
- ConBee ZigBee USB Gateway
In order to complete these steps, it is recommended to be familiar with Wireshark.
Description
Step 0: ZigBee Smart Home Provision
Be sure to have permission to hack into the ZigBee network you want to analyse. Even better, set up your own network to generate some traffic. Minimal requirements: 1 bridge and 1 connected smart home device, such as an LED lamp, preferably with an additional app e.g. for your phone, to control/manage the smart home devices.
Step 1: ConBee Setup
Plug ConBee into a USB Port.
Install firmware using ZShark
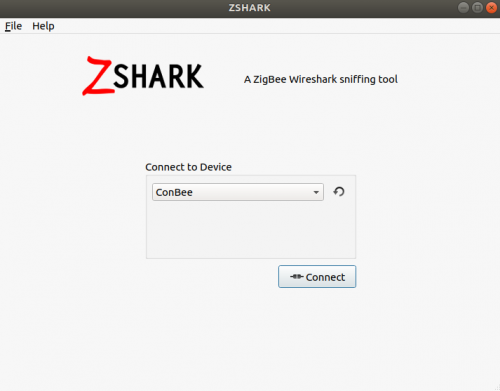
Open ZShark. You will see this window:
Select "ConBee" and click "Connect".
If the dialog tells you there is "No or wrong firmware found", and pressing the "Install Firmware" button doesn't prompt you to the next dialog, make sure no other USB devices are connected to your computer and try again.
If it still doesn't change, you can also install the firmware manually. For this open a terminal and change into the ZShark-folder (that is where you have installed the application) and run this command (as root):
GCFFlasher_internal -d /dev/ttyUSB0 -f /usr/share/zshark/fw/sniffer_v1_0.bin
where
- /dev/ttyUSB0 is the path to your device
- /usr/share/zshark/fw/sniffer_v1_0.bin is the path to the firmware you want to install
Both paths are the absolute paths, and they may certainly differ from this solution. Make sure you look up the correct paths on your own system and use them accordingly.
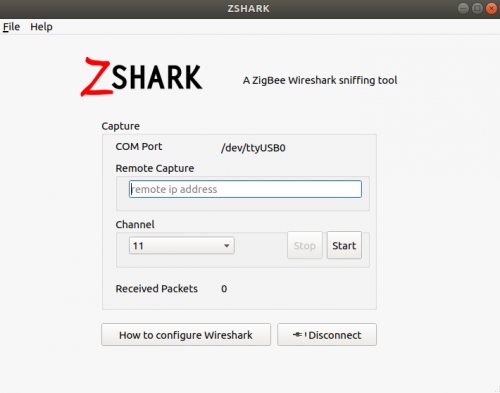
If everything worked fine, you should see a dialogue like this
where the path in the COM port identifier shows you the sniffer was detected correctly.
The remote capture IP is to use if you decide to send the captured data to Wireshark on another machine. In my case this was not necessary, as I used Wireshark on the same device.
Choose ZigBee channel
Channel 11 is the default ZigBee channel, so there you find your traffic unless you configured your network otherwise (in that case you obviously change it to the applicable channel).
Start capturing packets with "Start".
You should see the number identified by "Received Packets" in the dialogue to increase immediately.
Step 2: Wireshark Configuration
Open Wireshark.
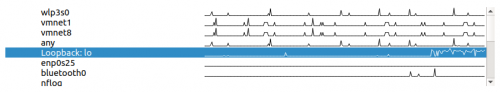
Select interface
Choose the loopback interface. This is where ZShark sends packets by default.
Leave the input field for capture filter empty.
Apply display filter
udp.port==17754 && !icmp
- UDP because our ZigBee devices rely on this protocol
- Port 17754 is designated for ZigBee packets
- And we don't need the ICMP output for our analysis
It won't do no harm if you forget to apply the filter, though you will get packets displayed you won't be interested in. You can also apply it afterwards or add additional filters to easier find specific packets.
Add symmetric key of bridge
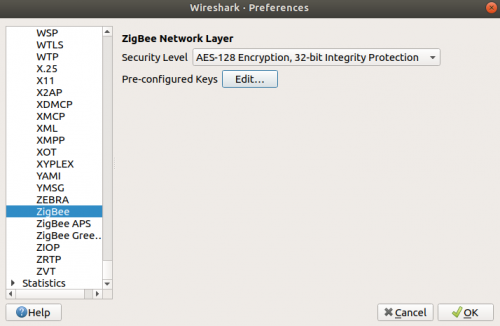
Go to:
Edit > Preferences > Protocols > ZigBee
Leave the Security Level in its default value (AES-128 Encryption, 32-bit Integrity Protection). Choose Edit at "Pre-configured keys" and add the key of your bridge, which in most cases is
5A:69:67:42:65:65:41:6C:6C:69:61:6E:63:65:30:39
or, in this case using the Philips Hue Bridge, is
81:42:86:86:5D:C1:C8:B2:C8:CB:C5:2E:5D:65:D1:B8
as these are mostly universal default keys so that communication in ZigBee networks can be established with lots of different devices from different vendors without further ado.
Another possible key, if the other two do not work as intendend would be
9F:55:95:F1:02:57:C8:A4:69:CB:F4:2B:C9:3F:EE:31
In both cases, choose the Byte Order "Normal".
Without the brigde key, you are still able to capture traffic, though you will not get access to additional information, or important insight into the payload respectively. For example, you would not be able to display the end-point device keys, which will be explained in the next step.
Start capturing the packets in Wireshark as well.
Step 3: Wireshark Network Traffic Analysis
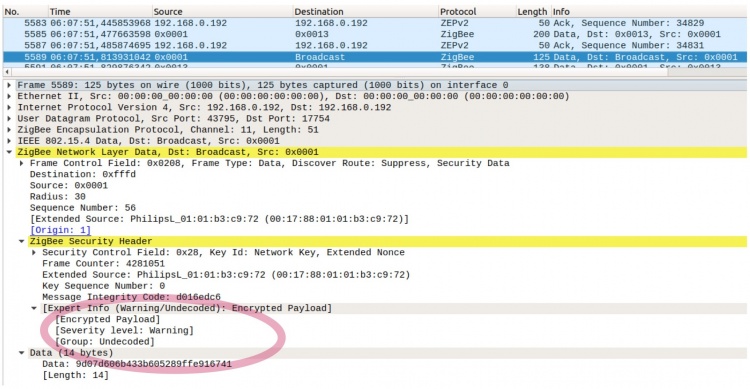
Now you will see traffic similar to this:
It shows there was data broadcasted, unfortunately without any further details. The circled output shows contained data is encrypted.
Locate Packet with Symmetric Key
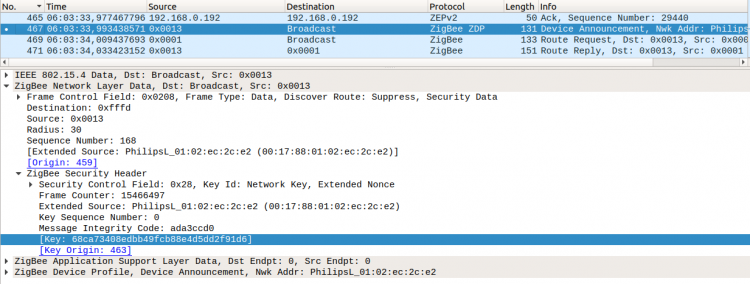
To get hold of an end-point device key in a ZigBee network, look out for specific packets. A device newly entering a network sends its key decrypted until it is established and ingested into the network by the bridge. If you have configured the bridge key correctly, you should see a new device advertising its symmetric key in packets which are tagged as "Device Announcement" in the information column of Wireshark (although there are other packets as well with visible key, this is the first one where this happens).
To simulate a device entering into a network, you have to reset it. With the light bulb, I simply disconnected it from its socket and re-attached it. Switching the light on and off won't help, it has to be taken off the electricity completely.
In newer versions of ZigBee it could happen, that the "Device Announcement"does not get send as usual when reconnecting after a power loss (socket disconnection). In this case try to remove the light bulb manually from the App and reconnect it.
Add end-point device key in Wireshark
Go to:
Edit > Preferences > Protocols > ZigBee
and add the key with Byte Order "Normal".
From this point on, you are able to see all information, as you can adequatly decrypt it.
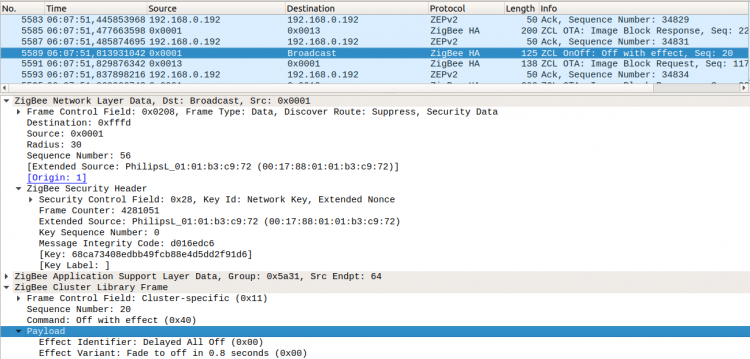
This is the same packet as the first one in this section, only with added key. As you can see, the payload is now clearly visible, and it shows detailed information about the transported commands.
Used Hardware
Philips Hue Bridge 2.0, Gateway
Philips Hue White LED E27 9.5W/827, white
Courses
- (nothing here yet)