Elliptic Curve Cryptography
Summary
This documentary gives a brief introduction into elliptic curve cryptography
Elliptic Curve Cryptography
Elliptic curve cryptography is a part of asymmetric cryptography, it is based on the mathematical hard problem to find a solution for the elliptic curve discrete logarithm. The calculations are performed on the algebraic structure of elliptic curves over finite fields, which means we compute points on a elliptic curve over finite field by applying the group operations double and add.
The scalar multiplication of a point on an elliptic curve over a finite field is equivalent to the exponentation of a number in a prime field, therefore the inversion is also called discrete logarithm.
First proposed application of elliptic curves in cryptography was random number generations, now ECC is widely used for key establishment and digital signature schemes.
Simple Weierstrass Elliptic Curve Presentation
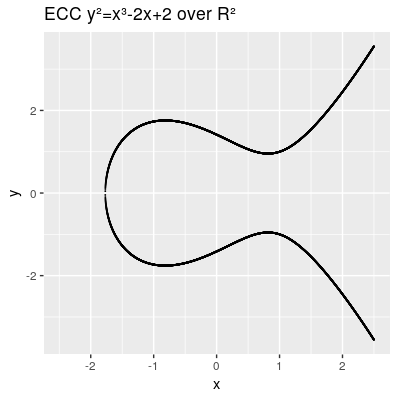
- Simple Weierstrass form curve equation:
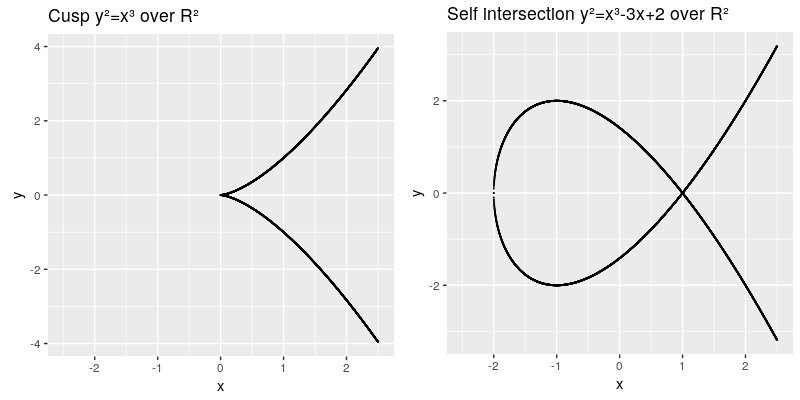
The elliptic curve are all points in the x,y coordinates which fulfill the cubic curve equation, whereas a and b are called the characteristic of the curve. The curve needs to be smooth, which means that it will not contain any singularities such as a cusp or a self intersection,
This can be also described by the term:
Another characteristic we need to introduce is the point at infinity denoted by 0 (also known as ideal point), which can be thought as identity element infinitly raised on the y axis. Therefore our points on the elliptic curve over R² all fulfill this equation and can be presented by:
A point consists of 2 values P(x,y).
Group operations on elliptic curves
According to the group law all points support following operations:
- Point addition:
- Point doubling:
TODO:Need to install link target extension: https://www.mediawiki.org/wiki/Extension:LinkTarget Test: https://cdn.rawgit.com/andreacorbellini/ecc/920b29a/interactive/reals-add.html
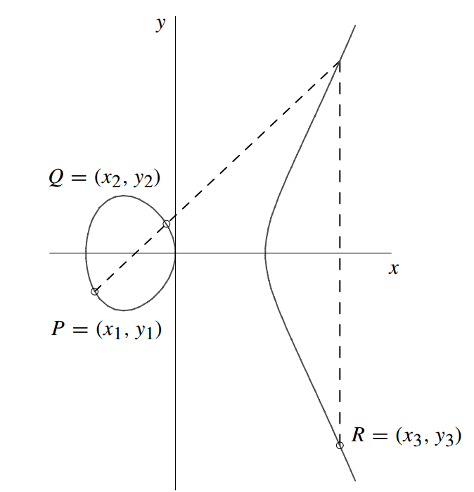
Given the elliptic curve and the points and , we can caculate the coordinates of the point as follows. 1. Calculation of
- We know the equation from the line
- Therfore
and we can find the intersection with the y-axis and achieve d .
- we can find by insertion in the line equation:
2. Calculation of
- Now we insert the values of the line equation into the elliptic curve equation:
- The cross points can be searched by
- Now we can conclude from the second term
- and achieve a solution for by:
Algebraic group of points
The points further comply associative and commutative algebraic group laws and the handling of the neutral element:
- closure: b
- associative:
- identity element and inverse that:
- cummutative:
The inverse point of a point P(x,y) is therfore P(x,-y).
Scalar Multiplication
Double and Add algorithm
Calculation in projective coordinates
Side Channel Attacks
Montgomery ladder
Standardization of elliptic curves
Curve25519
Curve25519 is a highly optimized curve proposed by Daniel J. Bernstein (djb) in 2005. The curve equation is over a prime field
Edward curves
Applications Example Elliptic curve Diffie Hellman key exchange
References
- ↑ Hankerson, D., A. Menezes and S. Vanstome: Guide to Elliptic Curve Cryptographie. Springer Verlag New York, Inc., 1. Auflage, 2004.