HNAP0wn: The Home Network Administration Protocol Owner
██╗ ██╗███╗ ██╗ █████╗ ██████╗ ██████╗ ██╗ ██╗███╗ ██╗ ██║ ██║████╗ ██║██╔══██╗██╔══██╗██╔═████╗██║ ██║████╗ ██║ ███████║██╔██╗ ██║███████║██████╔╝██║██╔██║██║ █╗ ██║██╔██╗ ██║ ██╔══██║██║╚██╗██║██╔══██║██╔═══╝ ████╔╝██║██║███╗██║██║╚██╗██║ ██║ ██║██║ ╚████║██║ ██║██║ ╚██████╔╝╚███╔███╔╝██║ ╚████║ ╚═╝ ╚═╝╚═╝ ╚═══╝╚═╝ ╚═╝╚═╝ ╚═════╝ ╚══╝╚══╝ ╚═╝ ╚═══╝
Summary
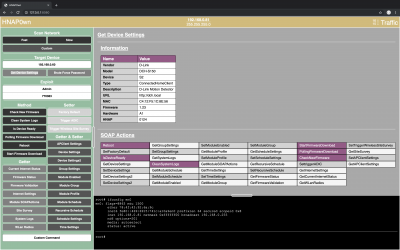
HNAP0wn is a graphical tool that allows us to find devices that use the Home Network Administration Protocol (HNAP) (File:HNAP Protocol.pdf), collect information about them, and inject commands. These instructions will get you a copy of the project up and running on your local machine for development and testing purposes. See deployment for notes on how to deploy the project on a live system.
Home Network Administration Protocol (HNAP)
HNAP is a network device management protocol that allows network devices to be silently managed and administered. HNAP is based on SOAP. HNAP was designed to be a simple, lightweight protocol that is easy to implement inside of small cost-constrained hardware such as the devices used in this examination. Cisco promised three high-level benefits to vendors for implementing HNAP in a network device [1]:
- Accurate topology discovery: A network device can accurately describe itself to applications that support HNAP and show detailed information about the device.
- Custom task extensibility: For example, when a device with HNAP support is selected in an application, tasks related to that device can be displayed.
- Programmable API: The fully programmable API suite allows devices’ network connections to be remotely managed and administered.
The participants in any HNAP interaction define the two roles – an HNAP server and an HNAP client. HNAP servers are typically implemented inside of networking devices to be managed. HNAP clients are usually software applications residing on PCs or other devices that can interact with an HNAP server in order to manage it, and ultimately, the device. [2] A typical client-server interaction begins when a client has discovered an HNAP server on a network. It issues an HNAP discovery command in order to determine the capabilities of the device. A client then proceeds to make one or more HNAP requests to the server, which performs the desired action and returns the response.
One can simply query all supported HNAP actions from a device by requesting the URL http://$DEVICE_IP/HNAP1/ from a web client. Since HNAP is encapsulated in HTTP, it is also the best way to determine if a device is HNAP-enabled since such devices need to reply to this request. In case of the DCH-S150 Motion Sensor the output of that link is listed below. There may be more or less SOAPactions available depending on the devices' configuration.
<?xml version="1.0" encoding="UTF-8"?> <soap:Envelope xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xmlns:xsd="http://www.w3.org/2001/XMLSchema" xmlns:soap="http://schemas.xmlsoap.org/soap/envelope/"> <soap:Body> <GetDeviceSettingsResponse xmlns="http://purenetworks.com/HNAP1/"> <GetDeviceSettingsResult>OK</GetDeviceSettingsResult> <Type>ConnectedHomeClient</Type> <DeviceName>MotionSensorDLink</DeviceName> <VendorName>D-Link</VendorName> <ModelDescription>D-Link Motion Detector</ModelDescription> <ModelName>DCH-S150</ModelName> <DeviceMacId>C4:12:F5:1C:8E:4C</DeviceMacId> <FirmwareVersion>1.23</FirmwareVersion> <FirmwareRegion>Default</FirmwareRegion> <LatestFirmwareVersion/> <HardwareVersion>A1</HardwareVersion> <HNAPVersion>0124</HNAPVersion> <PresentationURL>http://dch.local</PresentationURL> <CAPTCHA>false</CAPTCHA> <ModuleTypes> <string>Motion Sensor</string> </ModuleTypes> <SOAPActions> <string>http://purenetworks.com/HNAP1/Reboot</string> <string>http://purenetworks.com/HNAP1/SetFactoryDefault</string> <string>http://purenetworks.com/HNAP1/IsDeviceReady</string> <string>http://purenetworks.com/HNAP1/GetDeviceSettings</string> <string>http://purenetworks.com/HNAP1/SetDeviceSettings</string> <string>http://purenetworks.com/HNAP1/GetDeviceSettings2</string> <string>http://purenetworks.com/HNAP1/SetDeviceSettings2</string> <string>http://purenetworks.com/HNAP1/GetGroupSettings</string> <string>http://purenetworks.com/HNAP1/SetGroupSettings</string> <string>http://purenetworks.com/HNAP1/GetSystemLogs</string> <string>http://purenetworks.com/HNAP1/CleanSystemLogs</string> <string>http://purenetworks.com/HNAP1/GetModuleSchedule</string> <string>http://purenetworks.com/HNAP1/SetModuleSchedule</string> <string>http://purenetworks.com/HNAP1/GetModuleEnabled</string> <string>http://purenetworks.com/HNAP1/SetModuleEnabled</string> <string>http://purenetworks.com/HNAP1/GetModuleProfile</string> <string>http://purenetworks.com/HNAP1/SetModuleProfile</string> <string>http://purenetworks.com/HNAP1/GetModuleSOAPActions</string> <string>http://purenetworks.com/HNAP1/GetTimeSettings</string> <string>http://purenetworks.com/HNAP1/SetTimeSettings</string> <string>http://purenetworks.com/HNAP1/GetModuleGroup</string> <string>http://purenetworks.com/HNAP1/SetModuleGroup</string> <string>http://purenetworks.com/HNAP1/GetScheduleSettings</string> <string>http://purenetworks.com/HNAP1/SetScheduleSettings</string> <string>http://purenetworks.com/HNAP1/GetRecursiveSchedule</string> <string>http://purenetworks.com/HNAP1/SetRecursiveSchedule</string> <string>http://purenetworks.com/HNAP1/GetFirmwareStatus</string> <string>http://purenetworks.com/HNAP1/GetFirmwareValidation</string> <string>http://purenetworks.com/HNAP1/StartFirmwareDownload</string> <string>http://purenetworks.com/HNAP1/PollingFirmwareDownload</string> <string>http://purenetworks.com/HNAP1/CheckNewFirmware</string> <string>http://purenetworks.com/HNAP1/SettriggerADIC</string> <string>http://purenetworks.com/HNAP1/GetInternetSettings</string> <string>http://purenetworks.com/HNAP1/GetCurrentInternetStatus</string> <string>http://purenetworks.com/HNAP1/GetWLanRadios</string> <string>http://purenetworks.com/HNAP1/SetTriggerWirelessSiteSurvey</string> <string>http://purenetworks.com/HNAP1/GetSiteSurvey</string> <string>http://purenetworks.com/HNAP1/SetAPClientSettings</string> <string>http://purenetworks.com/HNAP1/GetAPClientSettings</string> </SOAPActions> <SubDeviceURLs/> </GetDeviceSettingsResponse> </soap:Body> </soap:Envelope>
Requirements
- PHP 5 Server or newer
- ECMAScript 6 Compatible Browser
- Optional: Nmap
Deployment
Get your copy from GitLab. Start the local PHP server using the run.sh script and open this link in browser: http://127.0.0.1:8080
sudo bash HNAP0wn/run.sh
Usage
Scan Network
Executes an underlying Nmap scan and displays HNAP enabled hosts together with additional information.
- Located in the Sidebar. (Green)
- Provides different Scan modes. (
Fast,Slow,Custom)
Custom scan mode gives the possibility to define Nmap parameters.Target Device
Gather information about a HNAP enabled device.
- Located in the Sidebar. (Green)
- Provides an input field for the target IP address
- Provides two modes. (
Get Device Settings,Brute Force Password)
Target IP address needs to be set! No Password nor Username needed at this point.Get Device Settings
Displays device information gathered via http://$IP/HNAP1/ and extends the sidebar by all supported HNAP actions available executables for the target device.
Brute Force Password
Tries all numeric combinations from 000000 to 999999 until a HNAP login was succesfull.
Admin and Password 000000 is used to initialize if none was set manually.^[0-9]{6}$ is adapted for use with mydlink™ home devices.Exploit
Area to define Username and Password. These credentials are used to inject HNAP Actions discovered via Get Device Settings.
- Located in the Sidebar. (Green)
- Provides an input field for the
UsernameandPassword.
Brute Force Password was previously run with success, then Username and Password are already set.HNAP Actions
Loaded after successfully executing Get Device Settings. Grouped into different groups. (Method, Getter, Setter, Getter & Setter)
- Loaded at the bottom of the Sidebar. (Green)
- Provides a button for every available action.
Custom mode. Information about the correct syntax may be found here: File:HNAP Protocol.pdfSimple
Simple actions executed once clicked on the according button in the sidebar. Results are displayed in the main container. (Grey)
Simple actions span over the following the groups: Method, Getter, Setter
Reboot and SetFactoryDefaults require confirmation.Getter / Setter
When executing this kind of action, the Getter action is executed on click, while the resulting table gives the possibility to change its values and send the update via the matching Setter action.
Getter is considered as a template to use it with its Setter.Custom
More complex HNAP actions can be executed here. Set HNAP action and parameters manually.
Terminal
Terminal emulation. Commands are executed by the local PHP server as sudoer and results are returned.
- Located at the bottom. (Black)
- Locally catched commands:
history,clear,!^[0-9]$ - Arrow up and down to navigate through the history.
Additional Information
GitLab
Demo
License
This project is licensed under the MIT License.
Compatible Browsers
- Chrome: ≥58
- Edge: ≥14
- Firefox: ≥54
- Safari: ≥10
- Opera: ≥55
Development Environment
Localhost
- MacOS Mojave 10.14.4 (18E226)
- Darwin Kernel 18.5.0 x86_64
- Chrome 75.0.3770.142 (Official Build) (64-bit)
- PHP 7.1.23 Development Server
- Nmap 7.70