Difference between revisions of "IKEA TRÅDFRI: Basic Setup"
Jump to navigation
Jump to search
(Added test results (AndroidEmulator & Wireshark)) |
m |
||
| Line 60: | Line 60: | ||
== Alternatives & Tests == | == Alternatives & Tests == | ||
As of today, there is no official alternative to a setup via mobile app, | As of today, there is no official alternative to a setup via mobile app, albeit ... | ||
* A simple nmap scan reveales a suspicious (unencrypted) open '''port 80''', which requires authentication ('''status code 470''', while no entity body is sent). | |||
* However listening into a live connection (Wireshark and an Android Emulator) reveals that actually a secure '''DTLS''' connection (port 5684) is used to set up the gateway. | |||
Basic scan results: | |||
[[File:Ikea tradfri gateway wiresharklog.png|right]] | [[File:Ikea tradfri gateway wiresharklog.png|right]] | ||
Latest revision as of 00:02, 16 September 2019
Summary
This documentation describes how to set up IKEA TRÅDFRI
Requirements
- A mobile device running either Android 4.1 or later, or iOS 9.0 or later
- Hardware: IKEA TRÅDFRI Typ E1526 (Gateway), WiFi router
Description
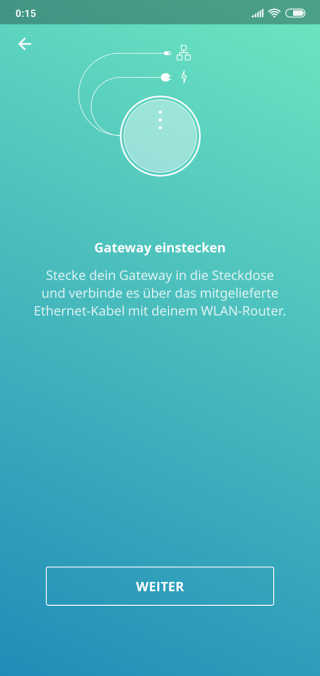
Step 1: Hardware Setup
- Connect the TRÅDFRI to your router, using a straight network cable
- Connect the micro usb power cable into the TRÅDFRI, and plug it in
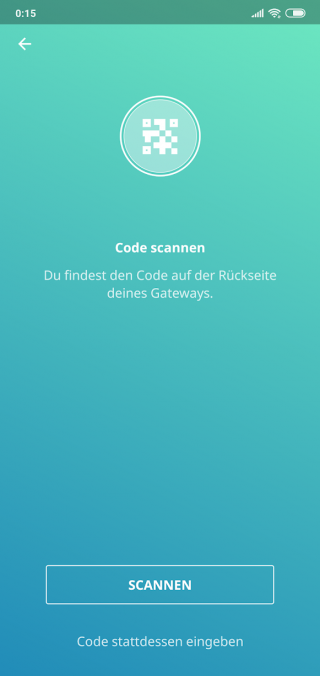
Step 2: Home Smart App
In order to set up your TRÅDFRI, you are required to install the IKEA Home Smart App either for Android or iOS:
Follow the instructions within the app, to finish the process.
Used Hardware
Mandadory:
Optional:
- Tradfri_dimmer
- Tradfri_smart_plug
- Tradfri_smart_plug_with_button
- Tradfri_signal_repeater
- Tradfri_remote_control
- Tradfri_motion_sensor
- Tradfri_Led_power_supply_with_wireless_receiver_10_W
- Tradfri_Led_power_supply_with_wireless_receiver_30_W
- Tradfri_LED_with_motion_sensor_1000_lm_12.5_W_E27
- Tradfri_LED_1000_lm_12.5_W_E27
- Tradfri_LED_1000_lm_12.5_W_E27_with_dimmer
- Tradfri_LED_1000_lm_12.5_W_E27_with_remote_control
- Tradfri_LED_400_lm_5.3_W_E14
- Tradfri_LED_400_lm_5.3_W_GU10
- Tradfri_LED_950_lm_12_W_E27
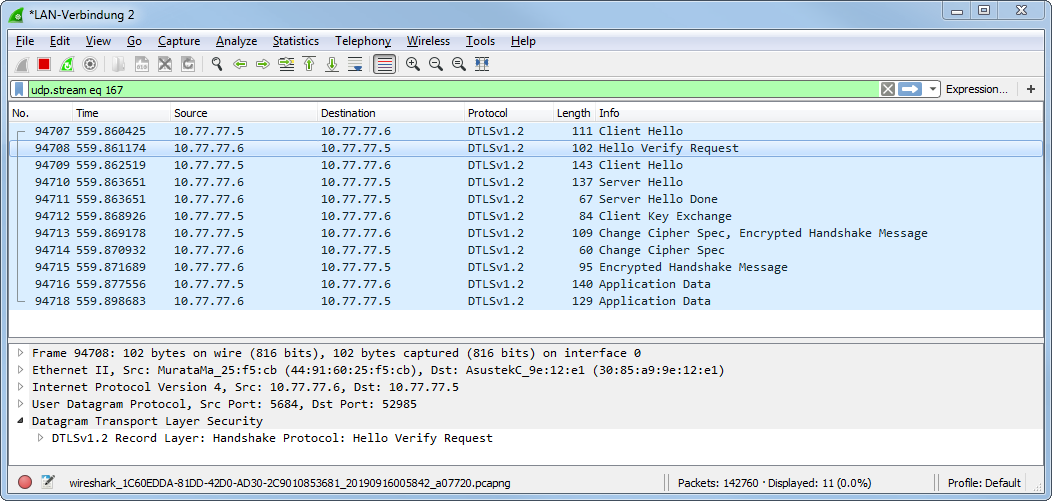
Alternatives & Tests
As of today, there is no official alternative to a setup via mobile app, albeit ...
- A simple nmap scan reveales a suspicious (unencrypted) open port 80, which requires authentication (status code 470, while no entity body is sent).
- However listening into a live connection (Wireshark and an Android Emulator) reveals that actually a secure DTLS connection (port 5684) is used to set up the gateway.
Basic scan results:
Starting Nmap 7.80 ( https://nmap.org ) at 2019-09-14 02:35 Mitteleuropäische Sommerzeit NSE: Loaded 151 scripts for scanning. NSE: Script Pre-scanning. ... Initiating ARP Ping Scan at 02:35 Scanning 10.77.77.6 [1 port] Completed ARP Ping Scan at 02:35, 0.19s elapsed (1 total hosts) Initiating Parallel DNS resolution of 1 host. at 02:35 Completed Parallel DNS resolution of 1 host. at 02:35, 11.04s elapsed Initiating SYN Stealth Scan at 02:35 Scanning 10.77.77.6 [1000 ports] Discovered open port 80/tcp on 10.77.77.6 Completed SYN Stealth Scan at 02:35, 0.81s elapsed (1000 total ports) Initiating Service scan at 02:35 Scanning 1 service on 10.77.77.6 Completed Service scan at 02:36, 38.22s elapsed (1 service on 1 host) ... Nmap scan report for 10.77.77.6 Host is up (0.00051s latency). Not shown: 999 closed ports PORT STATE SERVICE VERSION 80/tcp open http | fingerprint-strings: | DNSStatusRequestTCP, DNSVersionBindReqTCP, FourOhFourRequest, GenericLines, GetRequest, HTTPOptions, Help, Kerberos, LANDesk-RC, LDAPBindReq, LDAPSearchReq, LPDString, NCP, NotesRPC, RPCCheck, RTSPRequest, SIPOptions, SMBProgNeg, SSLSessionReq, TLSSessionReq, TerminalServer, TerminalServerCookie, X11Probe: |_ HTTP/1.1 470 Connection Authorization Required |_http-title: Site doesn't have a title. 1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service : SF-Port80-TCP:V=7.80%I=7%D=9/14%Time=5D7C35ED%P=i686-pc-windows-windows%r( SF:GetRequest,32,"HTTP/1\.1\x20470\x20Connection\x20Authorization\x20Requi SF:red\r\n\r\n")%r(HTTPOptions,32,"HTTP/1\.1\x20470\x20Connection\x20Autho SF:rization\x20Required\r\n\r\n")%r(RTSPRequest,32,"HTTP/1\.1\x20470\x20Co SF:nnection\x20Authorization\x20Required\r\n\r\n")%r(X11Probe,32,"HTTP/1\. SF:1\x20470\x20Connection\x20Authorization\x20Required\r\n\r\n")%r(FourOhF SF:ourRequest,32,"HTTP/1\.1\x20470\x20Connection\x20Authorization\x20Requi SF:red\r\n\r\n")%r(GenericLines,32,"HTTP/1\.1\x20470\x20Connection\x20Auth SF:orization\x20Required\r\n\r\n")%r(RPCCheck,32,"HTTP/1\.1\x20470\x20Conn SF:ection\x20Authorization\x20Required\r\n\r\n")%r(DNSVersionBindReqTCP,32 SF:,"HTTP/1\.1\x20470\x20Connection\x20Authorization\x20Required\r\n\r\n") SF:%r(DNSStatusRequestTCP,32,"HTTP/1\.1\x20470\x20Connection\x20Authorizat SF:ion\x20Required\r\n\r\n")%r(Help,32,"HTTP/1\.1\x20470\x20Connection\x20 SF:Authorization\x20Required\r\n\r\n")%r(SSLSessionReq,32,"HTTP/1\.1\x2047 SF:0\x20Connection\x20Authorization\x20Required\r\n\r\n")%r(TerminalServer SF:Cookie,32,"HTTP/1\.1\x20470\x20Connection\x20Authorization\x20Required\ SF:r\n\r\n")%r(TLSSessionReq,32,"HTTP/1\.1\x20470\x20Connection\x20Authori SF:zation\x20Required\r\n\r\n")%r(Kerberos,32,"HTTP/1\.1\x20470\x20Connect SF:ion\x20Authorization\x20Required\r\n\r\n")%r(SMBProgNeg,32,"HTTP/1\.1\x SF:20470\x20Connection\x20Authorization\x20Required\r\n\r\n")%r(LPDString, SF:32,"HTTP/1\.1\x20470\x20Connection\x20Authorization\x20Required\r\n\r\n SF:")%r(LDAPSearchReq,32,"HTTP/1\.1\x20470\x20Connection\x20Authorization\ SF:x20Required\r\n\r\n")%r(LDAPBindReq,32,"HTTP/1\.1\x20470\x20Connection\ SF:x20Authorization\x20Required\r\n\r\n")%r(SIPOptions,32,"HTTP/1\.1\x2047 SF:0\x20Connection\x20Authorization\x20Required\r\n\r\n")%r(LANDesk-RC,32, SF:"HTTP/1\.1\x20470\x20Connection\x20Authorization\x20Required\r\n\r\n")% SF:r(TerminalServer,32,"HTTP/1\.1\x20470\x20Connection\x20Authorization\x2 SF:0Required\r\n\r\n")%r(NCP,32,"HTTP/1\.1\x20470\x20Connection\x20Authori SF:zation\x20Required\r\n\r\n")%r(NotesRPC,32,"HTTP/1\.1\x20470\x20Connect SF:ion\x20Authorization\x20Required\r\n\r\n"); MAC Address: 44:91:60:25:F5:CB (Murata Manufacturing) No exact OS matches for host (If you know what OS is running on it, see https://nmap.org/submit/ ). TCP/IP fingerprint: OS:SCAN(V=7.80%E=4%D=9/14%OT=80%CT=1%CU=39904%PV=Y%DS=1%DC=D%G=Y%M=449160%T OS:M=5D7C362E%P=i686-pc-windows-windows)SEQ(CI=I%II=I%TS=U)ECN(R=N)T1(R=Y%D OS:F=N%T=80%S=O%A=S+%F=AS%RD=0%Q=)T1(R=N)T2(R=N)T3(R=N)T4(R=Y%DF=N%T=80%W=0 OS:%S=A%A=Z%F=R%O=%RD=0%Q=)T5(R=Y%DF=N%T=80%W=0%S=Z%A=S+%F=AR%O=%RD=0%Q=)T6 OS:(R=Y%DF=N%T=80%W=0%S=A%A=Z%F=R%O=%RD=0%Q=)T7(R=Y%DF=N%T=80%W=0%S=Z%A=S+% OS:F=AR%O=%RD=0%Q=)U1(R=Y%DF=N%T=FF%IPL=38%UN=0%RIPL=G%RID=G%RIPCK=G%RUCK=G OS:%RUD=G)IE(R=Y%DFI=N%T=80%CD=S) Network Distance: 1 hop TRACEROUTE HOP RTT ADDRESS 1 0.51 ms 10.77.77.6 NSE: Script Post-scanning. Initiating NSE at 02:37 Completed NSE at 02:37, 0.00s elapsed Initiating NSE at 02:37 Completed NSE at 02:37, 0.00s elapsed Initiating NSE at 02:37 Completed NSE at 02:37, 0.00s elapsed Read data files from: C:\Program Files (x86)\Nmap OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 89.06 seconds Raw packets sent: 1215 (58.910KB) | Rcvd: 1089 (45.266KB)