Difference between revisions of "Information Gathering Tools"
| Line 168: | Line 168: | ||
<b>Category: Information Gathering - OSINT</b><br> | <b>Category: Information Gathering - OSINT</b><br> | ||
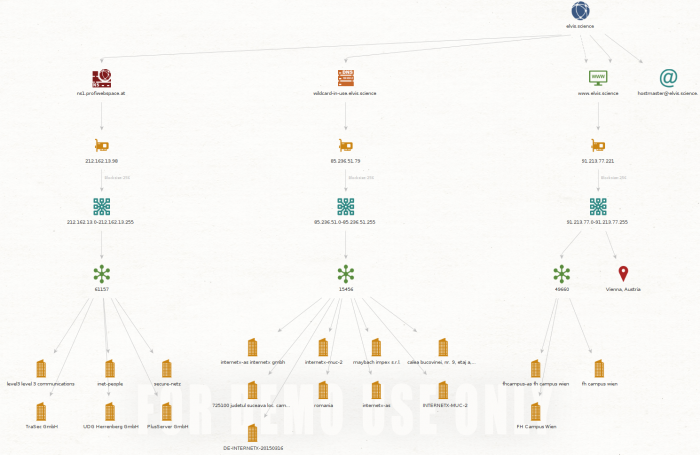
Maltego is a graphical footprinting tool with quite some extensions available. With the preinstalled extensions you can allready footprint any domain and view it as a tree. where this tree is formatted according to the amount discovered and may change to a mesh view, if it would get too crowded. | Maltego is a graphical footprinting tool with quite some extensions available. With the preinstalled extensions you can allready footprint any domain and view it as a tree. where this tree is formatted according to the amount discovered and may change to a mesh view, if it would get too crowded. | ||
[[File:Elvis.science.png|thumb|none|700px|Example footprinting of elvis.science]] | [[File:Elvis.science.png|thumb|none|700px|Example footprinting of elvis.science]] | ||
There is allready a page in this wiki for Maltego about how to create networks yourself without the use of extensions: [[https://wiki.elvis.science/index.php?title=Maltego|Documetation/Maltego]] | |||
=== Netdiscover === | === Netdiscover === | ||
Revision as of 08:21, 24 June 2021
Summary
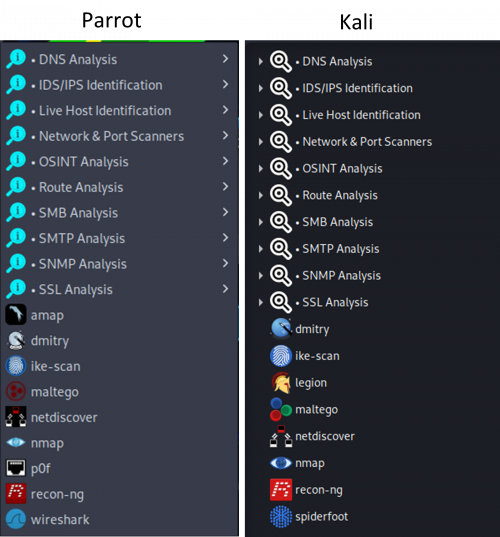
This is a draft. Comparing various available pre-installed information gathering tools in Kali and comparing differences to ParrotOS. This document is NOT a documentation of the tools, it is merely a comparison and practical evaluation of the tools for an average security specialist or a security newbie wanting to start using the tools.
Requirements
- Operating system: Kali Linux 2021.1 amd64, Parrot Security 4.10 amd64
Disclaimer: all possible examples and tests done have been done in VMWare in a Kali Linux 2021.1 and the commands are up-to-date as of 21st June 2021.
Tools
Nmap
Category: Information Gathering - Network & Port Scanners
Nmap is known to be a very powerful tool for information gathering and vulnerability scanning. It offers loads of options, offering for example for host discovery, scans (TCP, UDP, IP...), service/version detection, OS detection, firewalls/IDS evasion and spoofing, script scanning etc. Since this is not meant to be a full documentation of the tools, but rather an evaluation overview, compared to the other tools in this category, Nmap is the one main tool that most of the other secondary tools are using and it is very powerful. See the following tools for some comparison and Nmap examples.
For more information please refer to the full tool documentation.
Spiderfoot
Category: Information Gathering - OSINT
This is a reconnaissance framework that uses many modules for information gathering, working on the OSINT principle. You can access a GUI by starting the framework on a port on localhost and accessing that address via web browser once it starts:
$ spiderfoot -l 127.0.0.1:5001
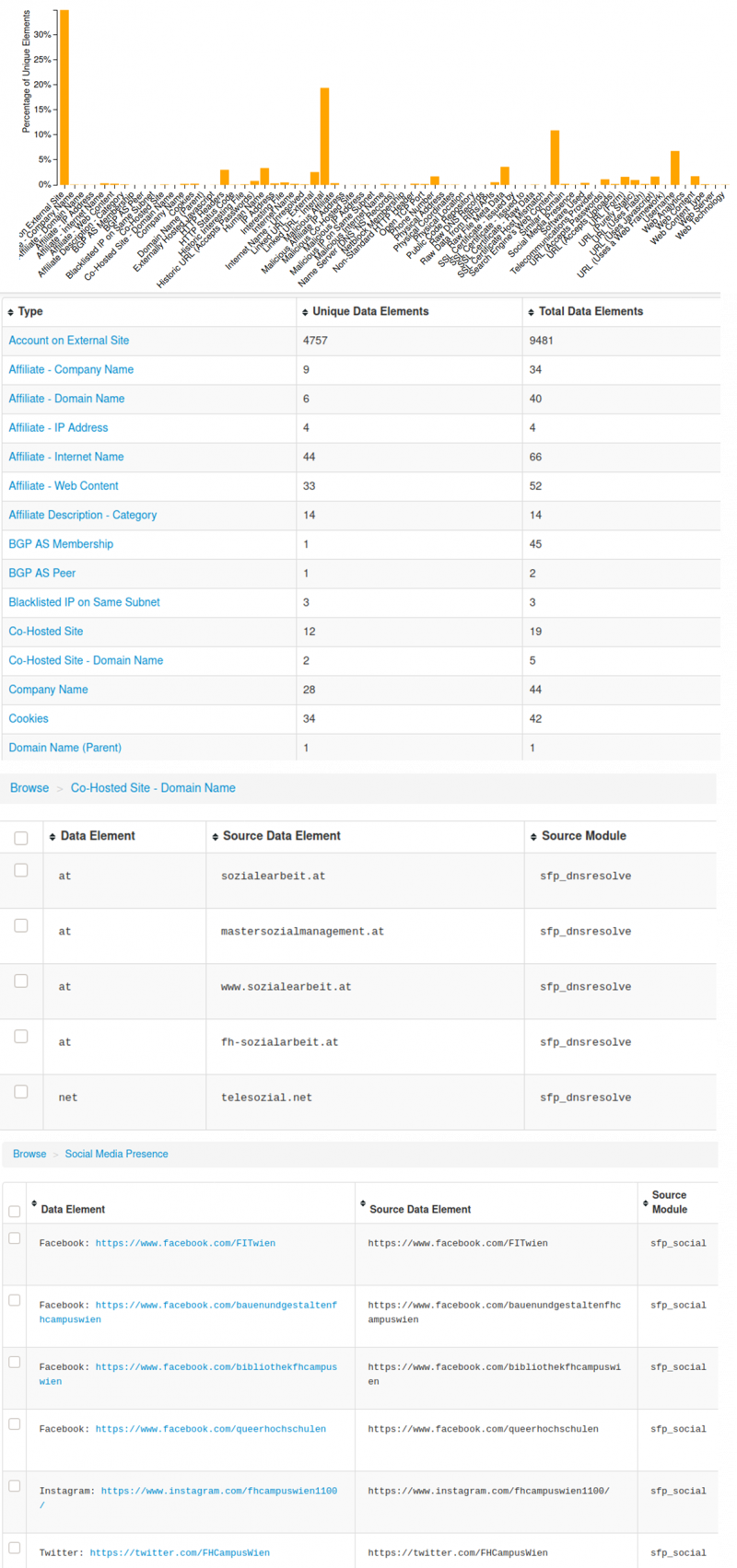
You can then set up a new scan, where you would give the program a target: this can be a domain/sub-domain name, IPv4 or IPv6 address, hostname, subnet, ASN, e-mail address, phone number, a person's actual name or username. This gives a really wide spectrum on options. The full scan is demonstrated below.
scan www.fh-campuswien.ac.at for a full scan, where you "get anything and everything about the target":
Execution takes many days, depending on the size of the target and the information available on the internet to that target. This specific inquiry took several days to complete and collect all information. Some parts of the information is displayed below, however the results were much more extensive:
For more information please refer to the full tool documentation.
Legion
Category: Information Gathering - general
Legion is a GUI tool, a network penetration testing framework, that offers many options. It automatically detects CVEs and provides nmap, Vulners, whataweb, webslayer, sslyzer, SMBenum, dirbuster, nikto, Hydra and other additional scripts. Its execution takes up to a couple of minutes. A demonstration:
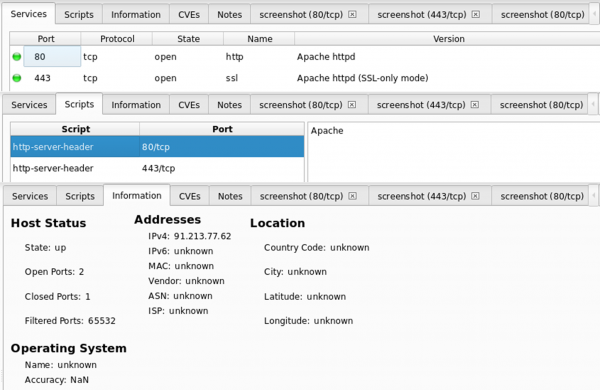
scan www.fh-campuswien.ac.at
No CVEs have been found.
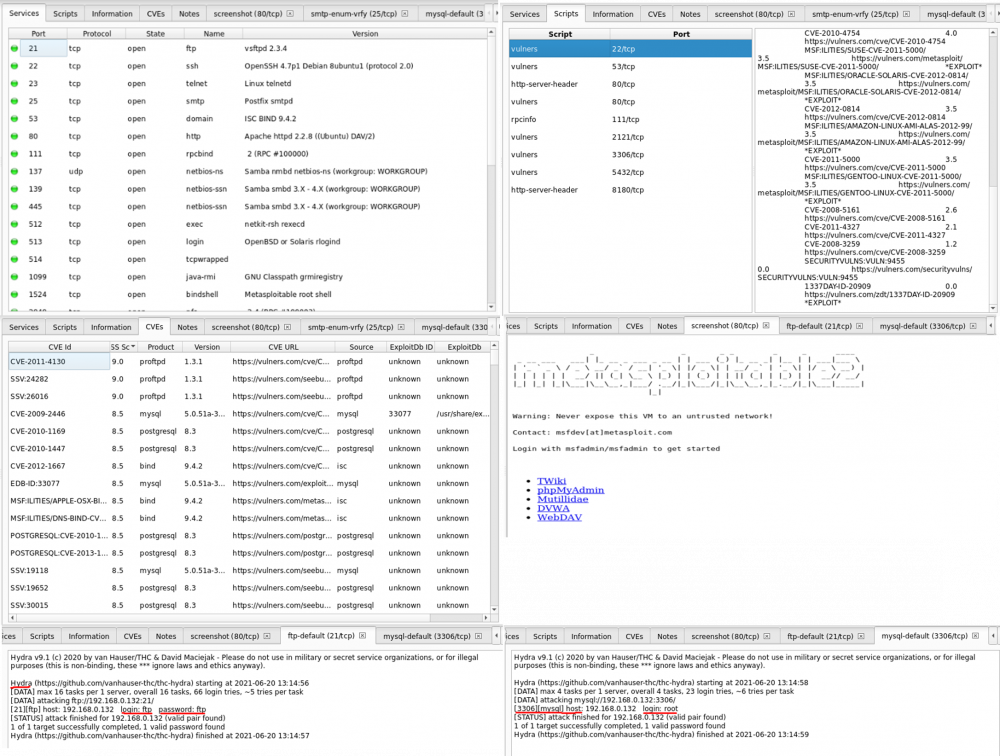
Below is a comparison with the Metasploitable2 machine that can be found in the same subnet, so that it is clear how the vulnerabilities are shown in an actual weak system:
It is safe to say that it is a very powerful and useful tool, also very user friendly and quite fast. Maybe not the best for domains in the internet because it won't offer much more information than nmap and whois lookup, but when you look at the metasploitable output, so a scan of a server, you can see how much information is shown. The implementation of Hydra also gets you the cracked passwords in the vulnerabilities which is very useful.
For more information please refer to the full official Legion Framework website.
DMitry
Category: Information Gathering - general
DMitry is a CLI tool to gather information about a host - possible subdomains, uptime information, tcp port scan, email addresses, whois lookups etc. It is mostly used to reveal information that exists through search engines about the owner or host of a web page, i.e. for social engineering attacks.
When using the portscan option, the results show less open ports than doing that same TCP scan with nmap.
DMitry:
HostIP:192.168.0.130 HostName: Gathered TCP Port information for 192.168.0.130 Port State 23/tcp open Portscan Finished: Scanned 150 ports, 148 ports were in state closed
Nmap:
Nmap scan report for 192.168.0.130 Host is up (0.20s latency). Not shown: 996 closed ports PORT STATE SERVICE 23/tcp open telnet 554/tcp open rtsp 843/tcp open unknown 5001/tcp open commplex-link MAC Address: 7C:DD:90:AF:4E:7D (Shenzhen Ogemray Technology) Nmap done: 1 IP address (1 host up) scanned in 2.33 seconds
To find out information about a domain, you need either the IP or the domain same.
Whois lookup on the other hand gets you some nice useful results. Below is an example of using dmitry -w www.fh-campuswien.ac.at on the college website of FH Campus Wien www.fh-campuswien.ac.at, and it just goes to show that it is exactly the same output as if you were to type whois fh-campuswien.ac.at
HostIP:91.213.77.62 HostName:www.fh-campuswien.ac.at Gathered Inic-whois information for fh-campuswien.ac.at --------------------------------- domain: fh-campuswien.ac.at registrar: registrant: FCW1942152-NICAT admin-c: tech-c: NLTU11579014-NICAT nserver: ns.nextlayer.at remarks: 81.16.150.30 nserver: ns2.nextlayer.at remarks: 81.16.151.30 changed: 20171003 19:16:08 source: AT-DOM personname: organization: fh campus wien street address: Favoritenstrasse 226 postal code: A-1100 city: Vienna country: Austria phone: +43160668771000 fax-no: +43160668771009 e-mail: office@fh-campuswien.ac.at nic-hdl: FCW1942152-NICAT changed: 20100323 17:12:46 source: AT-DOM personname: Hostmaster Hostmaster organization: next layer Telekommunikationsdienstleistungs- und BeratungsGmbH street address: Mariahilfer Guertel 37- 7 postal code: 1150 city: Vienna country: Austria phone: +43517649 e-mail: hostmaster@nextlayer.at nic-hdl: NLTU11579014-NICAT changed: 20170929 13:17:54 source: AT-DOM
For more information please refer to the full tool documentation.
Recon-ng
Category: Information Gathering - general
On the first glance, it looks very similar to Metasploit. You can start it via the command line and enter an environment in the shell. It is a python web reconnaissance framework designed specifically for web-based information gathering, and is, unlike Metasploit, not an exploitation framework.
To navigate it, always utilize the help flag to view possible options. At first, you won't have any modules enables/installed, which is kind of confusing and one really has to look into the documentation first before using it because the shell environment isn't that intuitive.
To view available modules, use show modules. When you want to start now, create a workspace first where your retrieved data will be saved:
[recon-ng][default] > workspaces create test
Now install the module you would like to use, we will use hackertarget to get subdomains. You can use marketplace search hackertarget to view the module and install it by:
[recon-ng][test] > marketplace install hackertarget [*] Module installed: recon/domains-hosts/hackertarget [*] Reloading modules...
Now we will load the module and set the source of input, which we want to retrieve data from. With the command info or input you can view the current source. Execute the module with run:
[recon-ng][test] > modules load hackertarget [recon-ng][test][hackertarget] > options set SOURCE tesla.com [recon-ng][test][hackertarget] > run
This will get you 27 found hosts, after the show hosts command you can review them in an arranged list:
+---------------------------------------------------------------------------------------------------------------------+ | rowid | host | ip_address | region | country | latitude | longitude | notes | module | +---------------------------------------------------------------------------------------------------------------------+ | 1 | tesla.com | 199.66.11.62 | | | | | | hackertarget | | 2 | o7.ptr6980.tesla.com | 149.72.144.42 | | | | | | hackertarget | | 3 | vpn1.tesla.com | 8.45.124.215 | | | | | | hackertarget | | 4 | model3.tesla.com | 205.234.27.221 | | | | | | hackertarget | | 5 | o3.ptr1444.tesla.com | 149.72.152.236 | | | | | | hackertarget | | 6 | o2.ptr556.tesla.com | 149.72.134.64 | | | | | | hackertarget | | 7 | o5.ptr8466.tesla.com | 149.72.172.170 | | | | | | hackertarget | | 8 | o6.ptr9437.tesla.com | 168.245.123.10 | | | | | | hackertarget | | 9 | o4.ptr1867.tesla.com | 149.72.163.58 | | | | | | hackertarget | | 10 | mobile.tesla.com | 209.133.79.82 | | | | | | hackertarget | | 11 | marketing.tesla.com | 13.111.47.196 | | | | | | hackertarget | | 12 | o1.ptr2410.link.tesla.com | 149.72.247.52 | | | | | | hackertarget | | 13 | referral.tesla.com | 72.10.32.90 | | | | | | hackertarget | | 14 | mta2.email.tesla.com | 13.111.4.231 | | | | | | hackertarget | | 15 | mta.email.tesla.com | 13.111.14.190 | | | | | | hackertarget | | 16 | xmail.tesla.com | 204.74.99.100 | | | | | | hackertarget | | 17 | comparison.tesla.com | 64.125.183.133 | | | | | | hackertarget | | 18 | emails.tesla.com | 13.111.18.27 | | | | | | hackertarget | | 19 | mta2.emails.tesla.com | 13.111.88.1 | | | | | | hackertarget | | 20 | mta3.emails.tesla.com | 13.111.88.2 | | | | | | hackertarget | | 21 | mta4.emails.tesla.com | 13.111.88.52 | | | | | | hackertarget | | 22 | mta5.emails.tesla.com | 13.111.88.53 | | | | | | hackertarget | | 23 | mta.emails.tesla.com | 13.111.62.118 | | | | | | hackertarget | | 24 | click.emails.tesla.com | 13.111.48.179 | | | | | | hackertarget | | 25 | view.emails.tesla.com | 13.111.49.179 | | | | | | hackertarget | | 26 | events.tesla.com | 13.111.47.195 | | | | | | hackertarget | | 27 | shop.eu.tesla.com | 205.234.27.221 | | | | | | hackertarget | +---------------------------------------------------------------------------------------------------------------------+
Disclaimer: the used Recon-ng version here is recon-ng v5.1.1, which is important to note, because countless tutorials on the internet refer to older commands which no longer work, so you kind of really have to play around with it to see which modules work (because some don't) and what commands are available by always utilizing the help flag along the way.
For more information please refer to the official documentation or Github, however the documentation in this case is quite lacking.
Maltego
Category: Information Gathering - OSINT
Maltego is a graphical footprinting tool with quite some extensions available. With the preinstalled extensions you can allready footprint any domain and view it as a tree. where this tree is formatted according to the amount discovered and may change to a mesh view, if it would get too crowded.
There is allready a page in this wiki for Maltego about how to create networks yourself without the use of extensions: [[1]]
Netdiscover
Category: Information Gathering - Route Analysis
This is another reconnaissance tool that can be used for host discovery on wireless and switched networks. You can scan your subnet at home or at work, wherever your device is connected. It works through ARP requests and can detect hosts either by actively sending requests, or if you set it to passive mode, only by sniffing.
If Nmap is too much for a given moment and you just want to see quickly who is in your network, this is the way to go. Below is a comparison of Netdiscover used on a local subnet, a very well-arranged output, and nmap, which in some situations offers too much:
$ netdiscover -r 192.168.0.0/24 20 Captured ARP Req/Rep packets, from 16 hosts. Total size: 1200 _____________________________________________________________________________ IP At MAC Address Count Len MAC Vendor / Hostname ----------------------------------------------------------------------------- 192.168.0.1 00:xx:xx:xx:xx:c2 2 120 Cisco Systems, Inc 192.168.0.9 00:xx:xx:xx:xx:a9 1 60 Weinzierl Engineering GmbH 192.168.0.10 50:xx:xx:xx:xx:c7 1 60 Loxone Electronics GmbH 192.168.0.80 54:xx:xx:xx:xx:a0 1 60 Hangzhou Hikvision Digital Technology Co.,Ltd. 192.168.0.81 18:xx:xx:xx:xx:50 1 60 Hangzhou Hikvision Digital Technology Co.,Ltd. 192.168.0.82 54:xx:xx:xx:xx:ff 1 60 Hangzhou Hikvision Digital Technology Co.,Ltd. 192.168.0.83 28:xx:xx:xx:xx:27 1 60 Hangzhou Hikvision Digital Technology Co.,Ltd. 192.168.0.84 18:xx:xx:xx:xx:d7 1 60 Hangzhou Hikvision Digital Technology Co.,Ltd. 192.168.0.101 48:xx:xx:xx:xx:2e 1 60 ZENNIO AVANCE Y TECNOLOGIA, S.L. 192.168.0.102 00:xx:xx:xx:xx:bb 1 60 VMware, Inc. 192.168.0.109 fc:xx:xx:xx:xx:f9 4 240 Ubiquiti Networks Inc. 192.168.0.112 04:xx:xx:xx:xx:a5 1 60 ASUSTek COMPUTER INC. 192.168.0.132 00:xx:xx:xx:xx:d4 1 60 VMware, Inc. 192.168.0.149 c4:xx:xx:xx:xx:48 1 60 Hewlett Packard 192.168.0.172 8c:xx:xx:xx:xx:eb 1 60 Apple, Inc. 192.168.0.195 f2:xx:xx:xx:xx:3a 1 60 Unknown vendor
If you were to do this same information in Nmap, you would need to perform a host discovery scan first:
$ nmap -sP 192.168.0.0/24 Starting Nmap 7.91 ( https://nmap.org ) at 2021-06-20 16:34 CEST Nmap scan report for 192.168.0.1 Host is up (0.0051s latency). Nmap scan report for 192.168.0.10 Host is up (0.00058s latency). Nmap scan report for 192.168.0.80 Host is up (0.00034s latency). Nmap scan report for 192.168.0.81 Host is up (0.0018s latency). Nmap scan report for 192.168.0.82 Host is up (0.0017s latency). Nmap scan report for 192.168.0.83 Host is up (0.0037s latency). Nmap scan report for 192.168.0.84 Host is up (0.0019s latency). Nmap scan report for 192.168.0.101 Host is up (0.00045s latency). Nmap scan report for 192.168.0.102 Host is up (0.00018s latency). Nmap scan report for 192.168.0.107 Host is up (0.00021s latency). Nmap scan report for 192.168.0.109 Host is up (0.00049s latency). Nmap scan report for 192.168.0.132 Host is up (0.00033s latency). Nmap scan report for 192.168.0.172 Host is up (0.089s latency). Nmap done: 256 IP addresses (13 hosts up) scanned in 2.42 seconds
Only then you can scan each alive host separately for their Hostname/OS/MAC address with sudo nmap -O <IP address>. That is unless you want to wait several hours by scanning the whole subnet for their OS which I would not recommend since it takes so long. If you need a quick swipe, Nmap is possibly the inferior option here and could be used once you want to find out more about each host, their ports etc.
For more information please refer to the full tool documentation.
Ike-scan
Category: Information Gathering - general
Ike-scan is useful for VPN endpoints. To explain this a little, first we should know what IKE is. It is Internet Key Exchange protocol, which is used by IPsec. The majority of IPsec VPNs use IKE for key exchange. The Ike-scan tool is for discovering, testing and fingerprinting IPsec VPN systems. It sends IKE phase 1 packets to the target and displays the received responses. To be able to test this, we now need a target that we are certain uses IKE for key exchange. To achieve this, we will demonstrate this on an IP address found through www.shodan.io, where you need to search for the keyword "IKE" to find targets that satisfy this condition. For demonstration, we chose the IP 110.142.206.85, which should be a VPN in Melbourne, Australia.
$ ike-scan 110.142.206.85 Starting ike-scan 1.9.4 with 1 hosts (http://www.nta-monitor.com/tools/ike-scan/) 110.142.206.85 Main Mode Handshake returned HDR=(CKY-R=49cc50cbfcf85509) SA=(Enc=3DES Hash=SHA1 Group=2:modp1024 Auth=PSK LifeType=Seconds LifeDuration=28800) VID=dbfb81eb5760b0788562067da102d755 VID=09002689dfd6b712 (XAUTH) VID=afcad71368a1f1c96b8696fc77570100 (Dead Peer Detection v1.0) VID=12f5f28c457168a9702d9fe274cc0100 (Cisco Unity) Ending ike-scan 1.9.4: 1 hosts scanned in 0.356 seconds (2.81 hosts/sec). 1 returned handshake; 0 returned notify
This returns the main mode handshake and shows information like security associations (hash, encoding, authentication) and also vendor ID etc.
The following scan tries to fingerprint the firewall in use and additionally to the previous output it shows the following:
$ ike-scan --showbackoff -v -v 110.142.206.85 DEBUG: pkt len=336 bytes, bandwidth=56000 bps, int=52000 us Starting ike-scan 1.9.4 with 1 hosts (http://www.nta-monitor.com/tools/ike-scan/) --- Sending packet #1 to host entry 1 (110.142.206.85) tmo 500000 us --- Received packet #1 from 110.142.206.85 --- Removing host entry 1 (110.142.206.85) - Received 152 bytes IKE Backoff Patterns: IP Address No. Recv time Delta Time 110.142.206.85 1 1624204029.790995 0.000000 110.142.206.85 Implementation guess: Linksys Etherfast Ending ike-scan 1.9.4: 1 hosts scanned in 60.426 seconds (0.02 hosts/sec). 1 returned handshake; 0 returned notify
There is a possibility to use the so called aggressive mode (default is Main Mode) which uses a 3-way-handshake where the VPN sends an unencrypted message to the client containing the hashed PSK. If you manage to capture the plaintext hash, you could use psk-crack to perform a brute force attack and try to recover the PSK (Pre-shared key).
For more information please refer to the full tool documentation.
Dnsenum
Category: Information Gathering - DNS Analysis
This is an efficient and well-performing tool for locating all DNS servers and DNS entries for a given organization. A basic demonstration on the example of google.com is shown below (some entries have been replaced with ... to keep it as short as possible):
$ dnsenum google.com 255 ⨯
dnsenum VERSION:1.2.6
----- google.com -----
Host's addresses:
__________________
google.com. 300 IN A 216.58.201.78
Name Servers:
______________
ns2.google.com. 345600 IN A 216.239.34.10
ns4.google.com. 345600 IN A 216.239.38.10
ns1.google.com. 345600 IN A 216.239.32.10
ns3.google.com. 345600 IN A 216.239.36.10
Mail (MX) Servers:
___________________
aspmx.l.google.com. 293 IN A 173.194.69.27
alt1.aspmx.l.google.com. 293 IN A 142.250.150.27
alt2.aspmx.l.google.com. 293 IN A 74.125.200.27
alt3.aspmx.l.google.com. 293 IN A 142.250.157.27
alt4.aspmx.l.google.com. 293 IN A 173.194.202.26
Trying Zone Transfers and getting Bind Versions:
_________________________________________________
Trying Zone Transfer for google.com on ns1.google.com ...
AXFR record query failed: corrupt packet
...
Trying Zone Transfer for google.com on ns4.google.com ...
AXFR record query failed: corrupt packet
Brute forcing with /usr/share/dnsenum/dns.txt:
_______________________________________________
about.google.com. 0 IN CNAME www3.l.google.com.
www3.l.google.com. 300 IN A 172.217.23.238
accounts.google.com. 300 IN A 172.217.23.205
admin.google.com. 300 IN A 172.217.23.206
ads.google.com. 300 IN A 216.58.201.78
america.google.com. 0 IN CNAME www3.l.google.com.
...
www.google.com. 300 IN A 172.217.23.196
google.com class C netranges:
______________________________
8.8.4.0/24
8.8.8.0/24
...
216.239.36.0/24
216.239.38.0/24
Performing reverse lookup on 4096 ip addresses:
________________________________________________
68.224.9.64.in-addr.arpa. 86400 IN PTR vpn.google.com.
69.224.9.64.in-addr.arpa. 86400 IN PTR vpn.google.com.
70.224.9.64.in-addr.arpa. 86400 IN PTR vpn.google.com.
10.32.239.216.in-addr.arpa. 86400 IN PTR ns1.google.com.
11.32.239.216.in-addr.arpa. 86400 IN PTR ns.google.com.
15.32.239.216.in-addr.arpa. 86400 IN PTR time1.google.com.
116.32.239.216.in-addr.arpa. 86400 IN PTR e2a.google.com.
10.34.239.216.in-addr.arpa. 86400 IN PTR ns2.google.com.
10.36.239.216.in-addr.arpa. 86400 IN PTR ns3.google.com.
11.36.239.216.in-addr.arpa. 86400 IN PTR hedns1.google.com.
10.38.239.216.in-addr.arpa. 86400 IN PTR ns4.google.com.
11 results out of 4096 IP addresses.
google.com ip blocks:
______________________
64.9.224.68/31
64.9.224.70/32
216.239.32.10/31
216.239.32.15/32
216.239.32.116/32
216.239.34.10/32
216.239.36.10/31
216.239.38.10/32
done.
You can also use the --enum flag to gather whois information and to dig up subdomains.
For more information please refer to the full tool documentation.
Swaks
Category: Information Gathering - SMTP Scan
This tool is for sending e-mails of all kinds. Now, compared to a regular e-mail client, here you can change the header, attachments, which server to talk to and more. It handles TLS, authentication, and pipelining.
Since I don't have my own SMTP server available, for demonstration purposes we will use the Gmail's SMTP server:
$ swaks -t example.receiver@gmail.com -s smtp.gmail.com:587 -tls -a LOGIN
You will then be prompted to enter Gmail credentials of an actual existing account. However, from security reasons, Gmail will probably block this login attempt, that's why using your own SMTP server would be ideal. To have a look at some more examples of changing headers and using different servers, please refer here.
For more information please refer to the full tool documentation.
SSLdump
Category: Information Gathering - SSL Analysis
SSLdump is a TLS/SSL network protocol analyzer that identifies TCP streams/connections from a specified port and interface and attempts to interpret them. Once it identifies SSL/TLS traffic, it decodes and displays the content in a readable form as text. If you provide a necessary key as well, it can decrypt the connection fully and display the exchanged application data traffic (ssldump -Ad -k ~/privatekey.pem -p password -i eth0 host user123). Below is a demonstration of a basic command that listens to traffic on port 443 of interface eth0:
$ sudo ssldump -i eth0 port 443
New TCP connection #2: 192.168.0.102(53984) <-> edge-star-mini-shv-01-vie1.facebook.com(443)
2 1 0.0096 (0.0096) C>S Handshake
ClientHello
Version 3.3
resume [32]=
37 64 3d 51 d2 3d 5a 44 38 c6 72 d6 7f 34 16 ed
cc f0 32 fe ed 95 94 67 c8 dc ec 2e f5 ba 04 cf
cipher suites
TLS_AES_128_GCM_SHA256
TLS_CHACHA20_POLY1305_SHA256
TLS_AES_256_GCM_SHA384
TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256
TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256
TLS_ECDHE_ECDSA_WITH_CHACHA20_POLY1305_SHA256
TLS_ECDHE_RSA_WITH_CHACHA20_POLY1305_SHA256
TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384
TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384
TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA
TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA
TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA
TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA
TLS_RSA_WITH_AES_128_GCM_SHA256
TLS_RSA_WITH_AES_256_GCM_SHA384
TLS_RSA_WITH_AES_128_CBC_SHA
TLS_RSA_WITH_AES_256_CBC_SHA
TLS_RSA_WITH_3DES_EDE_CBC_SHA
compression methods
NULL
extensions
server_name
host_name: www.facebook.com
extended_master_secret
renegotiation_info
supported_groups
ec_point_formats
session_ticket
application_layer_protocol_negotiation
status_request
key_share
supported_versions
signature_algorithms
psk_key_exchange_modes
record_size_limit
padding
ja3 string:
771,4865-4867-4866-49195-49199-52393-52392-49196-49200-49162-49161-49171-49172-156-157-47-53-10,0-23-65281-10-11-35-16-5-51-43-13-45-28-21,29-23-24-25-256-257,0
ja3 fingerprint: aa7744226c695c0b2e440419848cf700
2 2 0.0146 (0.0049) S>C Handshake
ServerHello
Version 3.3
session_id[32]=
37 64 3d 51 d2 3d 5a 44 38 c6 72 d6 7f 34 16 ed
cc f0 32 fe ed 95 94 67 c8 dc ec 2e f5 ba 04 cf
cipherSuite TLS_AES_128_GCM_SHA256
compressionMethod NULL
extensions
supported_versions
key_share
ja3s string: 771,4865,43-51
ja3s fingerprint: f4febc55ea12b31ae17cfb7e614afda8
2 3 0.0146 (0.0000) S>C ChangeCipherSpec
2 4 0.0146 (0.0000) S>C application_data
For more information please refer to the full tool documentation.
What's different in ParrotOS?
As we know, you can install any tools from Kali also on ParrotOS, and the other way around, that's why in this context, the preinstalled tools are meant. Overall you can say, that the "main" tools are the same on both operating systems.
On the first glance the tools look very similar, however when you click on the the various sub-categories, you can see that Parrot offers a greater range of tools. Refer to the table below for a detailed overview:
| Tool Category | >>>>>Kali<<<<< | >>>>>Parrot<<<<< |
|---|---|---|
| DNS Analysis |
dnsenum
|
dnsdict6
|
| IDS/IPS Identification |
lbd
|
lbd
|
| Live Host Identification |
arping
|
arping
|
| Network & port scanners |
masscan
|
amap
|
| OSINT Analysis |
maltego
|
casefile
|
| Route Analysis |
netdiscover
|
0trace
|
| SMB Analysis |
enum4linux
|
enum4linux
|
| SMTP Analysis | swaks |
smtp-user-enum
|
| SNMP Analysis |
onesixtyone
|
braa
|
| SSL Analysis |
ssldump
|
ssldump
|