Difference between revisions of "JTAGulator: Introduction"
Jostrowski (talk | contribs) |
Jostrowski (talk | contribs) (Add link) |
||
| Line 104: | Line 104: | ||
: Set the RX, TX and the baudrate you found before. | : Set the RX, TX and the baudrate you found before. | ||
'''For an example visit: [[ | '''For an example visit: [[Editing JTAGulator: Find IoT-Device's UART interface]]''' | ||
Revision as of 11:26, 2 December 2019
JTAG explained
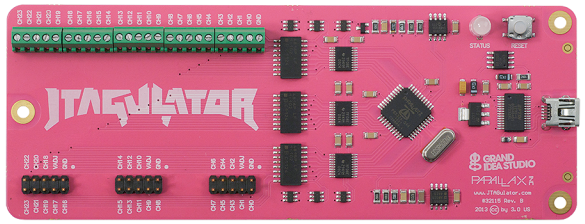
The JTAGulator is tool to assist identifying JTAG and USART pins.
JTAG (named after the Joint Test Action Group) is an industry standard for verifying designs and testing printed circuit boards after manufacture.
- JTAG allows for many applications
-
- Boundary Scan (read and set values of pin)
- Debugging of hardware / software
- Program / Modify memory
- Chips can be daisy chained, so you can access multiple chips through one interface
- JTAG consist of 4 essential signals
-
- TCK ... Test Clock
- TMS ... Test Mode Select (Steuerung)
- TDI ... Test Data In
- TDO ... Test Data Out
- additional signals
-
- Vcc ... 3.3V
- GND ... ground
- TRST .. test reset (low active)
- RST ... system reset (low active)
Good video about the JTAG interface: EEVblog #499 - What is JTAG and Boundary Scan?
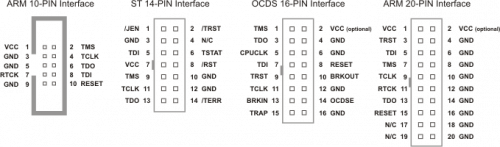
Manufactures have different Pin Layout, for Cortex Connectors it looks like this:
JTAGulator Overview
Since JTAG pins are not always labelled, they can be hard to find. This is when the JTAGulator comes into play.
You connect the channels of the JTAGulator to different test pins on the hardware you want to analyze.
The JTAGulator test each individual pins and tries to find JTAG connections. If found it will output the correct JTAG pins.
Setup
- Make sure you have the latest firmware
- JTAGulator: Update firmware
- Connect the JTAGulator via serial to the computer
- 115200 bps, 8 data bits, no parity, 1 stop bit
- Linux: you can use minicom
- Windows: you can use Putty
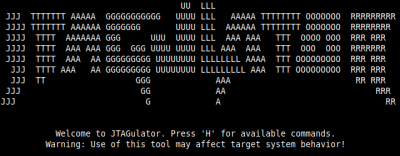
- You should see following output:
- Connect the JTAGulator to the test-device
- Connect the JTAGulator Ground (GND) to the GND of the hardware you want to analyze.
- Connect CHx from the JTAGulator to some pins (make sure via multimeter that the pins do not have a voltage levels over 3.3V) on the hardware which may be JTAG pins (start from CH0). Do not use the VADJ pin on the JTAGualtor (VADJ is the output from the PWM/op amp hardware on the JTAGulator that's used to create the target system voltage and drive the on-board level translators.)
JTAGulator commands
This tutorial is based on the firmware version 1.6
- Display all commands:
H - Display firmware version:
I
- First you need to set the voltage level
- Press
Vand set the voltage level accordingly (check via multimeter or hardware specification, usually 3.3)
Finding JTAG
- Type
Jto get to the JTAG commands - Then type
Hfor useful help-information
- IDCODE scan
I - This is a quick scan, which checks the output of every possible combination and presents possible combination + device IDs
- You can filter out incorrect JTAG identification by looking at the ID (device IDs are eye-catching, they are very non-uniform eg. (0x0D780237) and not like (0xFFFFFF7F) or (0x55555555) )
- BYPASS scan
B - After you used the IDcode scan, you want to determine the TDI line
- Enter x for the unknown TDI line and the numbers of the possible JTAG combination
- Test BYPASS
T - After the TDI pin was found, test the communication using the echo command of the JTAG interface. Here a random string gets sent to the TDI line of the JTAG interface and the JTAG controller should now send the same string back on the TDO line.
- With this you can make sure, that is really is a JTAG interface
- Go into the Test BYPASS menu, enter the number of the pins and see if the string matches
- If it does match it is very likely to be a JTAG interface, if not you will have to try out other pins.
For a real world example look into the post: JTAGulator: Find a Smartphone's JTAG interface
Finding UART
The JTAGulator can also find UART pins by bruteforcing the pinout configuration as well as the baudrate
- Find UART pins
- To enter the UART commands enter:
U
- (You can get help via
H)
- Set the voltage level with
V - Enter the bruteforce mode:
U - Set parameters (make sure you do not ignore non-printable characters)
- Analyze output
- If the the JTAGulator received a message it will output it to the screen
- The JTAGulator will display the TX and RX pin, the baudrate it was using and the message it received
- In the default configuration the JTAGualtor will send <CR> (0x0D) commands to the device
- Usually UART interfaces answer on <CR> commands with a response and append a <LF> (0x0A) or <CR> ( 0x0D) to it. THIS is a good indicator that is choose the right baudrate.
- Connect to UART
- The JTAGualtor allows for passthrough of UART commands
- Enter
Pfor UART passthrough
- Set the RX, TX and the baudrate you found before.
For an example visit: Editing JTAGulator: Find IoT-Device's UART interface