Meterpreter
Summary
Meterpreter, which is short for Meta-Interpreter, is an attack payload included in the Metasploit Framework. It was developed by Matt Miller under the hacker moniker of Skape. It is used in the post-exploitation phase after an exploit was already used to gain access to a system. It provides a more powerful interactive command line interface (CLI) than a regular shell and also avoids the risk of being exposed since starting a regular shell process could alert the system to intrusion. Meterpreter does not need a separate process to execute since it is injected into a process already running on the target system. This also means it is executed from memory only, which makes it even harder to detect for Anti-Virus software. Meterpreter has a wide variety of commands, additional modules and scripts available for further exploiting a system. Since it is integrated into the Metasploit Framework it can use its post-exploitation modules as well.
Meterpreter Basics
How does Meterpreter work?
- Target system is compromised using an exploit.
- Compromised system executes the initial Meterpreter payload also called stager (bind_tcp, reverse_tcp, ...)
- The stager loads the needed DLLs, the Meterpreter core initializes and established a TLS connection to the attacking system.
- Meterpreter sends a GET request which Metasploit receives and configures the client.
- Meterpreter loads the default extensions (stdapi and priv) over the TLS connection by using the TLV (Type-Length-Value) protocol.
Meterpreter Design Goals
Meterpreter is supposed to give the attacker access to a command interpreter on the target machine that offers powerful post-exploitation tools and is also hard to detect with forensic tools. To achieve this goal three requirements had to be met.
Stealthy
The payload had to be stealthy and hard to detect.
- Meterpreter is designed to operate in working memory and never write to the physical disk.
- Meterpreter operates inside running processes and can be migrated to other processes.
- Meterpreter uses encrypted communication.
Powerful
The user rights on the target system can be elevated using privilege escalation.
- Meterpreter utilizes a channelized communication system.
- The TLV (Type-Length-Value) protocol has few limitations.
Extensible
Meterpreter had to be extensible to adapt to different requirements.
- Meterpreter can be augmented at runtime. Extensions, modules and scripts can be loaded over the network connection.
- The Meterpreter session does not have to be rebuilt every time new features are added.
Meterpreter Features
The Meterpreter CLI offers standard commands that are also used in shells like sh and zsh. Additional commands are loaded by default and can be added by loading extensions.
Basic Commands
Commonly used Meterpreter commands can be found in the table below.
| Command | Description |
|---|---|
| background | Moves the current Meterpreter session to the background letting the user use the Metasploit command line. |
| sessions -i ID | Reactivates the specified session. Using the command without a switch shows all active sessions. |
| clearev | Deletes all Application, System and Security logs on the victim machine. Only works for Windows systems. |
| execute | Executes a command on the remote machine specified by the -f switch. The executed command can be supplied with arguments by using -a |
| getsystem | This attempts to elevate the current Meterpreter session to system administrator level of authorization. |
| getuid | Displays the user identification of the user the current Meterpreter session is running as. |
| hashdump | Prints all available usernames and their password hashes, making them available for further manipulation like password cracking using additional software or rainbow tables. |
| help | Shows the Meterpreter help menu consisting of a comprehensive list of commands. This menu expands if more extensions are loaded. |
| ipconfig | Prints the network configuration of the target machine in Windows display style. |
| migrate | Migrates the Meterpreter session to the process given as a parameter. This allows further exploitation of the system from within the new process. This should be done to avoid getting thrown out by the user closing the process that served as entry point. |
| ps | Prints a non-interactive list of the currently running processes on the target machine including process IDs, usernames of the process owners and the path to the executables. |
| search | Searches the system for a file specified by the -f switch. The provided filename may contain wildcards. |
Extensions
Meterpreter extensions are loaded by using the load-command. Some Extensions are loaded by default like the priv-extension which is used for privilege escalation and the stdapi-extension which supplies basic Meterpreter commands like getuid. Frequently used extensions include:
- kiwi (formerly mimikatz): This extension is used to obtain user credentials and authentication tokens. These are retrieved directly from target systems memory. Passwords can even be displayed directly in cleartext.
- python : This extensions allows the execution of python scripts on the target machine.
- powershell : This extensions allows the execution of powershell scripts on the target machine.
Scripts & Modules
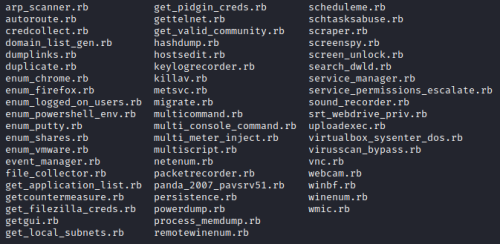
Meterpreter includes pre-made scripts that can be used for various purposes and are run by using the run-command. It includes scripts that can persist Meterpreter sessions, unlock the targets screen or disable Anti-Virus software. Some of the script seen in the figure below are considered deprecated. Some of those, like the persistence script were integrated directly into the Metasploit Framework. A Meterpreter session can be put into the background to run these post-exploitation modules supplied by Metasploit.
Sources
- D. Kennedy, J. O’Gorman, D. Kearns, and M. Aharoni. Metasploit: The Penetration Tester’s Guide. No Starch Press Series. No Starch Press, 2011.
- M. Miller. Meterpreter specifications. http://www.hick.org/code/skape/papers/meterpreter.pdf, 2004. Accessed: 2022-09-14.
- Metasploit Unleashed free ethical hacking course. https://www.offensive-security.com/metasploit-unleashed/. Accessed: 2022-11-05.
- Michael Messner. Hacking mit Metasploit. dpunkt.verlag, 3rd edition, 2017.