Difference between revisions of "OpenHAB - Man in the middle attack"
| Line 28: | Line 28: | ||
[[File:Traffic_before_attack.png]] | [[File:Traffic_before_attack.png]] | ||
== | == Using Cain & Able == | ||
The first thing to do when using Cain and Able is to use the sniffing function the determine which hosts in the network are available for sniffing and MitM attacks. | |||
To start the process, we click on the second button from the right in the top left corner. | |||
Make sure to read | Make sure to read | ||
Revision as of 17:57, 16 July 2019
Summary
The results of our Man in the middle attack on OpenHAB.
Goal
To perform a Man in the Middle attack via arp spoofing between a Hue bridge and a computer and capture the traffic send between OpenHab and the bridge to control a wireless light.
Used Software
- Cain & Able https://www.chip.de/downloads/Cain-Abel_17043501.html
- OpenHAB https://www.openhab.org/
You can find our documentation about installing OpenHAB here Install OpenHAB.
- Wireshark https://www.wireshark.org/
Used Hardware
Philips Hue White and Color Ambiance Single LED-Bulb E27 10W
Philips Hue Bridge 2.0, Frequencies 2400-2483.5 MHz
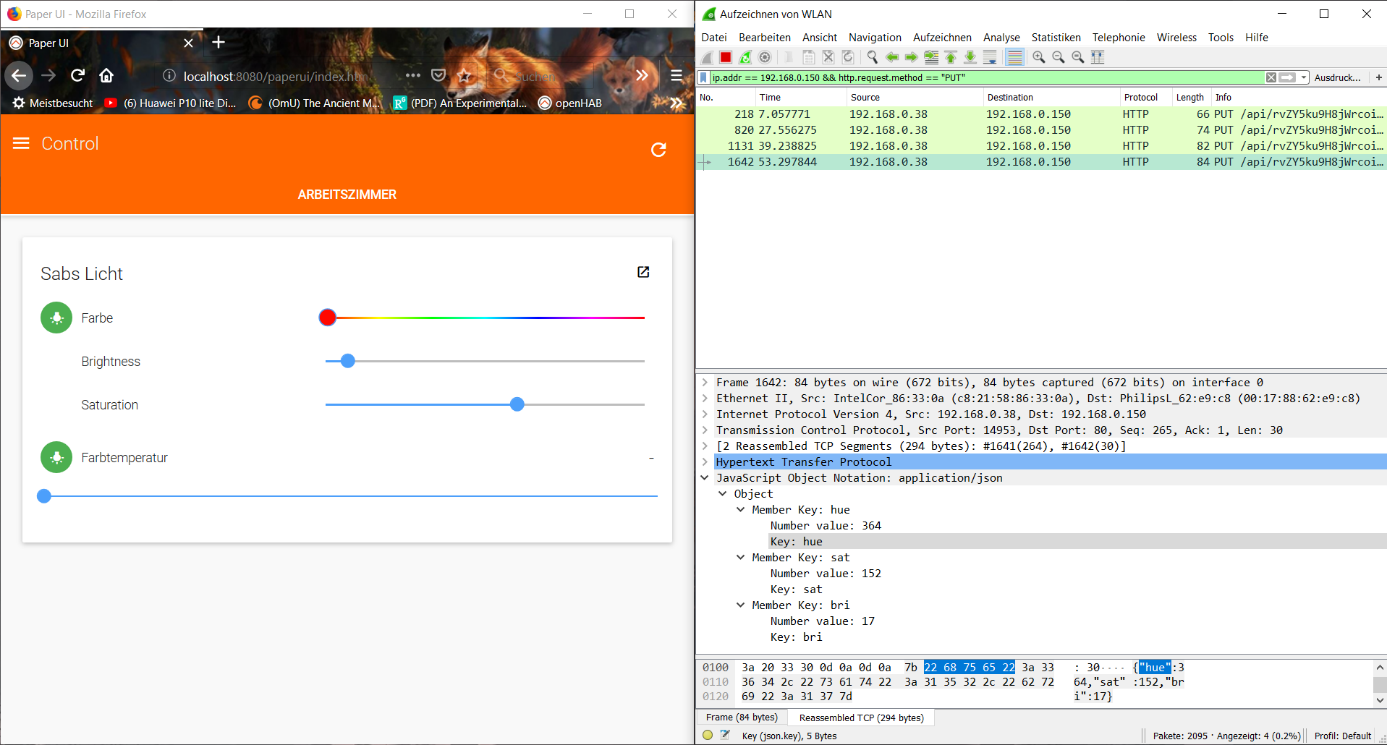
Capturing traffic before the Attack
Before we performed the Man in the Middle attack, we performed a wireshark capturing directly on the host camputer which was using OpenHab.
As one can see, we can see in plain text the numbers for color, saturation and brightness. And we see every PUT message send whenever we change something.
Using Cain & Able
The first thing to do when using Cain and Able is to use the sniffing function the determine which hosts in the network are available for sniffing and MitM attacks.
To start the process, we click on the second button from the right in the top left corner.
Make sure to read
- War and Peace
- Lord of the Rings
- The Baroque Cycle