Difference between revisions of "Proxmark3: Useful commands"
Jostrowski (talk | contribs) (Add hf section) |
Jostrowski (talk | contribs) (Add final) |
||
| Line 47: | Line 47: | ||
==== command: hw ==== | ==== command: hw ==== | ||
hw stands for hardware and lists a bunch of commands to get basic hardware information of the Proxmark3. | "hw" stands for hardware and lists a bunch of commands to get basic hardware information of the Proxmark3. | ||
detectreader ['l'|'h'] -- Detect external reader field (option 'l' or 'h' to limit to LF or HF) | detectreader ['l'|'h'] -- Detect external reader field (option 'l' or 'h' to limit to LF or HF) | ||
| Line 71: | Line 71: | ||
fpga_hf.bit built for 2s30vq100 on 2019/03/20 at 08:08:07 | fpga_hf.bit built for 2s30vq100 on 2019/03/20 at 08:08:07 | ||
We can now check the antenna strength of the attached antennas. If you have borrowed the proxmark3 of the Elvis IoT Lab you will get following output | We can now check the antenna strength of the attached antennas. If you have borrowed the proxmark3 of the Elvis IoT Lab you will get following output: | ||
(If no smart card is in proximity): | (If no smart card is in proximity): | ||
| Line 94: | Line 94: | ||
==== command: hf ==== | ==== command: hf ==== | ||
hf stands for high frequency, which are specified at a carrier frequency of about 13.56 MHz. | "hf" stands for high frequency, which are specified at a carrier frequency of about 13.56 MHz. | ||
Possible commands that can be issued: | Possible commands that can be issued are listed below: | ||
proxmark3> hf | proxmark3> hf | ||
| Line 117: | Line 117: | ||
Must of these group together different smart card manufactures. On the other hand 14a is a NFC card standard that describes low level communication of smart cards. Not all follow the same standard and some implement proprietary protocols. The Mifare cards are built upon the 14a standard and has additional commands which can be found in their specific directory. | Must of these group together different smart card manufactures. On the other hand 14a is a NFC card standard that describes low level communication of smart cards. Not all follow the same standard and some implement proprietary protocols. The Mifare cards are built upon the 14a standard and has additional commands which can be found in their specific directory. | ||
You usually start with the '''hf search''' command. It sends the card some data and analyses the return messages of the | You usually start with the '''hf search''' command. It sends the card some data and analyses the return messages of the card. With this information it can make assumptions on what kind of card it may be. | ||
proxmark3> hf search | proxmark3> hf search | ||
| Line 135: | Line 135: | ||
[[File:Waveform.PNG|frameless]] | [[File:Waveform.PNG|frameless]] | ||
Thankfully people wrote programs that will parse this data a dedicated protocol ('''hf list'''). In this case we want to parse it as a Mifare classic communication with '''hf list mf'''. | Thankfully people wrote programs that will parse this data to a dedicated protocol ('''hf list'''). In this case we want to parse it as a Mifare classic communication with '''hf list mf'''. | ||
proxmark3> hf list mf | proxmark3> hf list mf | ||
| Line 158: | Line 158: | ||
54196 | 58932 | Tag | 01 20 01 45 | | AUTH: nt | 54196 | 58932 | Tag | 01 20 01 45 | | AUTH: nt | ||
More on what is happening here can be found in the documentation [[Proxmark3: FH-Campus Card NFC Security Valuation]] | |||
There are many more commands. For example, '''hf data''' to manipulate the raw data, or '''hf mf''' to interact with Mifare Classic cards. Since this is only a short introduction to commands of the Proxmark3 we won't go deeper. If one is interested and wants to find out more about the Proxmark you we highly recommend the documentation [[Proxmark3: FH-Campus Card NFC Security Valuation]] - where not only the essentials are covered, but also an in depth explanation about the technology used, the Proxmark itself, the Mifare Classic Standard and a validation of the FH-Campus card system. | |||
It is definitely worth checking out the paper, since it also shows which vulnerabilities where found in the school card system. | |||
== Used Hardware == | == Used Hardware == | ||
| Line 181: | Line 171: | ||
* [[Proxmark3: Installation]] | * [[Proxmark3: Installation]] | ||
* [[Proxmark3: FH-Campus Card NFC Security Valuation]] | |||
== References == | == References == | ||
Revision as of 12:18, 22 July 2019
Authors
- Ostrowski, John
- Arseven, Can
Summary
"NFC Hacking with Proxmark3" has been conducted during a school project, in which we analyzed the implementation of our NFC System. Which includes our on-campus cards, the printing system, snacks and drinks machines and the classroom doors. The additional output of this project was a (tested) guide on how to install the Proxmark3. For further details with regards to our project, concrete tests and more advanced commands please see our documentation Proxmark3: FH-Campus Card NFC Security Valuation.
In this thread we show a short overview of the different commands the proxmark3 environment has to offer.
Requirements
Please see the Proxmark3: Installation guide for a full overview of requirements. However, the Operating systems on which we tested the installation on are:
- Ubuntu 16.04/18.03
- Windows 10
- MacOS 10.x
In order to complete the "Introduction" described below, you have to complete the Proxmark3: Installation guide first.
These overview is based on the proxmark3 client, published on Github on the 29. May 2019
Introduction
This introduction should only give you a glimpse of the available commands and possibilities of the Proxmark3. The official Proxmark3-Repository as well as the more advanced Ice-Man-Fork Repository (both linked in the reference section) provide lots of functions, though most of them are still in their alpha stage and therefore still need a bit of tinkering in order to work well. For further commands and our security analysis of our university feel free to have a look at our documentation!
The Commands
After you have successfully completed the Install Proxmark3 guide, you should see a screen similar to this when connecting to your proxmark3:
proxmark3>
You can always (in whichever menu you are) type 'help' in order to have a full list of available commands in that menu. If you enter help in the start menu, you will get following output:
help This help. Use '<command> help' for details of a particular command.
data { Plot window / data buffer manipulation... }
hf { High Frequency commands... }
hw { Hardware commands... }
lf { Low Frequency commands... }
emv { EMV iso14443 and iso7816... }
sc { Smartcard commands... }
script { Scripting commands }
quit Exit program
exit Exit program
command: hw
"hw" stands for hardware and lists a bunch of commands to get basic hardware information of the Proxmark3.
detectreader ['l'|'h'] -- Detect external reader field (option 'l' or 'h' to limit to LF or HF) fpgaoff Set FPGA off lcd <HEX command> <count> -- Send command/data to LCD lcdreset Hardware reset LCD readmem [address] -- Read memory at decimal address from flash reset Reset the Proxmark3 setlfdivisor <19 - 255> -- Drive LF antenna at 12Mhz/(divisor+1) setmux <loraw|hiraw|lopkd|hipkd> -- Set the ADC mux to a specific value tune ['l'|'h'] -- Measure antenna tuning (option 'l' or 'h' to limit to LF or HF) version Show version information about the connected Proxmark status Show runtime status information about the connected Proxmark ping Test if the pm3 is responsive
We can check the version of the different builds of the Proxmark3 currently running on it:
proxmark3> hw version Prox/RFID mark3 RFID instrument bootrom: master/v3.1.0-94-gd38bb3a-dirty-suspect 2019-06-01 14:36:05 os: master/v3.1.0-94-gd38bb3a-dirty-suspect 2019-06-01 14:36:22 fpga_lf.bit built for 2s30vq100 on 2015/03/06 at 07:38:04 fpga_hf.bit built for 2s30vq100 on 2019/03/20 at 08:08:07
We can now check the antenna strength of the attached antennas. If you have borrowed the proxmark3 of the Elvis IoT Lab you will get following output:
(If no smart card is in proximity):
proxmark3> hw tune Measuring antenna characteristics, please wait......... # LF antenna: 43.86 V @ 125.00 kHz # LF antenna: 21.04 V @ 134.00 kHz # LF optimal: 44.14 V @ 123.71 kHz # HF antenna: 30.41 V @ 13.56 MHz
If we now lay a NFC card on the antennas the voltages changes:
proxmark3> hw tune Measuring antenna characteristics, please wait......... # LF antenna: 44.27 V @ 125.00 kHz # LF antenna: 21.04 V @ 134.00 kHz # LF optimal: 44.27 V @ 123.71 kHz # HF antenna: *19.39 V* @ 13.56 MHz
We can see, that the voltage of the HF antenna dropped from 30 volts to about 19 volts. We can assume that the placed NFC card is a high frequency card.
command: hf
"hf" stands for high frequency, which are specified at a carrier frequency of about 13.56 MHz. Possible commands that can be issued are listed below:
proxmark3> hf
14a { ISO14443A RFIDs... }
14b { ISO14443B RFIDs... }
15 { ISO15693 RFIDs... }
epa { German Identification Card... }
legic { LEGIC RFIDs... }
iclass { ICLASS RFIDs... }
mf { MIFARE RFIDs... }
mfu { MIFARE Ultralight RFIDs... }
mfp { MIFARE Plus RFIDs... }
topaz { TOPAZ (NFC Type 1) RFIDs... }
fido { FIDO and FIDO2 authenticators... }
tune Continuously measure HF antenna tuning
list List protocol data in trace buffer
plot Plot signal
search Search for known HF tags [preliminary]
snoop <samples to skip (10000)> <triggers to skip (1)> Generic HF Snoop
Must of these group together different smart card manufactures. On the other hand 14a is a NFC card standard that describes low level communication of smart cards. Not all follow the same standard and some implement proprietary protocols. The Mifare cards are built upon the 14a standard and has additional commands which can be found in their specific directory.
You usually start with the hf search command. It sends the card some data and analyses the return messages of the card. With this information it can make assumptions on what kind of card it may be.
proxmark3> hf search UID : 01 02 03 04 ATQA : 00 04 SAK : 08 [2] TYPE : NXP MIFARE CLASSIC 1k | Plus 2k SL1 proprietary non iso14443-4 card found, RATS not supported Chinese magic backdoor commands (GEN 1a) detected Prng detection: WEAK Valid ISO14443A Tag Found - Quiting Search
Here we see that this card is classified as a Mifare Classic 1k. In particularly it also answers back to the Chinese magic backdoor command which tells us that this card is a clone card which allows us to change the UID block of the card. More on this can be found in the Documentation Proxmark3: FH-Campus Card NFC Security Valuation
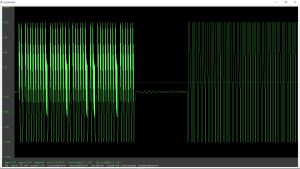
We can now issue the hf plot command which will display a waveform with the just sent and received data.
Thankfully people wrote programs that will parse this data to a dedicated protocol (hf list). In this case we want to parse it as a Mifare classic communication with hf list mf.
proxmark3> hf list mf
Recorded Activity (TraceLen = 156 bytes)
Start = Start of Start Bit, End = End of last modulation. Src = Source of Transfer
iso14443a - All times are in carrier periods (1/13.56Mhz)
iClass - Timings are not as accurate
Start | End | Src | Data (! denotes parity error, ' denotes short bytes) | CRC | Annotation |
-----------|------------|-----|-----------------------------------------------------------------|-----|--------------------|
0 | 992 | Rdr | 40' | | MAGIC WUPC1
2484 | 3060 | Tag | 0a' | |
7040 | 8352 | Rdr | 43 | | MAGIC WUPC2
9524 | 10100 | Tag | 0a' | |
14080 | 18848 | Rdr | 50 00 57 cd | ok | HALT
0 | 992 | Rdr | 52' | | WUPA
2228 | 4596 | Tag | 04 00 | |
7040 | 9504 | Rdr | 93 20 | | ANTICOLL
10676 | 16564 | Tag | 01 02 03 04 04 | |
19328 | 29856 | Rdr | 93 70 01 02 03 04 04 8e 25 | ok | SELECT_UID
31028 | 34548 | Tag | 08 b6 dd | |
47488 | 52192 | Rdr | 60 00 f5 7b | ok | AUTH-A(0)
54196 | 58932 | Tag | 01 20 01 45 | | AUTH: nt
More on what is happening here can be found in the documentation Proxmark3: FH-Campus Card NFC Security Valuation
There are many more commands. For example, hf data to manipulate the raw data, or hf mf to interact with Mifare Classic cards. Since this is only a short introduction to commands of the Proxmark3 we won't go deeper. If one is interested and wants to find out more about the Proxmark you we highly recommend the documentation Proxmark3: FH-Campus Card NFC Security Valuation - where not only the essentials are covered, but also an in depth explanation about the technology used, the Proxmark itself, the Mifare Classic Standard and a validation of the FH-Campus card system.
It is definitely worth checking out the paper, since it also shows which vulnerabilities where found in the school card system.