Difference between revisions of "Sniffing&Spoofing"
(Created page with "== Summary == Sniffing and Spoofing are common methods, to capture the traffic, manipulate data and execute a variate of attacks. In most cases the attacker wants to gain in...") |
(→Tools) |
||
| Line 26: | Line 26: | ||
== Tools == | == Tools == | ||
* Macchanger | * Macchanger [https://www.kali.org/tools/macchanger/] | ||
* Netsniff-ng | * Netsniff-ng [http://netsniff-ng.org/] | ||
* Ettercap | * Ettercap [https://www.ettercap-project.org/] | ||
* Mitmproxy | * Mitmproxy [https://mitmproxy.org/] | ||
* Responder | * Responder [https://www.kali.org/tools/responder/] | ||
== Requirements == | == Requirements == | ||
Latest revision as of 15:47, 4 January 2022
Summary
Sniffing and Spoofing are common methods, to capture the traffic, manipulate data and execute a variate of attacks. In most cases the attacker wants to gain information from the victim(Username and password, credit card information, etc.).
Introduction
Sniffing:
A sniffer is a program or device that eavesdrops on network traffic by intercepting information transmitted over a network. Sniffers are basically a "data interception" technology. They work because Ethernet was built on the principle of sharing. Most networks use broadcast technology, in which messages for one computer can be read by another computer on that network. In practice, all other computers except the one for which the message is intended will ignore that message. However, computers can be made to accept messages even if they are not intended for them.
Spoofing:
Spoofing involves disguising a message from an unknown source as coming from a known, trusted source. It can be used to gain access to a target's personal information, spread malware via infected links or attachments, bypass network access controls, or redirect traffic to perform a denial-of-service attack. Through spoofing, a malicious actor often gains access to conduct a larger cyberattack, such as an advanced persistent threat or man-in-the-middle attack.
Spoofing Methods:
- IP Spoofing
- ARP Spoofing
- DNS Server Spoofing
- Email Spoofing
- Caller ID Spoofing
- Website Spoofing
- GPS Spoofing
- Extension Spoofing
Tools
Requirements
- Operating system: Ubuntu 18.04 bionic amd64
- VMware
Example
Description
This example will demonstrate the tools netsniff-ng and ettercap. The Attacker will perform a "Man in the middle attack" to capture all the traffic that is adressed to the Victim.
Setup
2 Virtuell Machines with a connection to the Internet.
Step 1
Update both machines with:
sudo apt-get update sudo apt install net-tools
Step 2
Install Ettercap and Netsniff-ng on the Attacker machine:
sudo apt install netsniff-ng sudo apt-get install ettercap-graphical
Step 3
Starting the Man in the middle Attack:
Start Ettercap: ettercap -G
When starting ettercap u have to make sure to choose the right interface and then start the application.
In this step u have to set the Gateway IP on the left side and the target IP on the right side.
Now u have to click on arp poisoning and the "Man in the middle attack" is done. All traffic that is going from or to the victim are redirected to the attacker. So the attacker can capture the victims traffic.
Step 4
Starting Netsniff-ng
netsniff-ng --in ens33 --out infooutput.pcap Make sure to choose the right interface again and to select a target file where the ouput should be saved.
Step 5
Result:
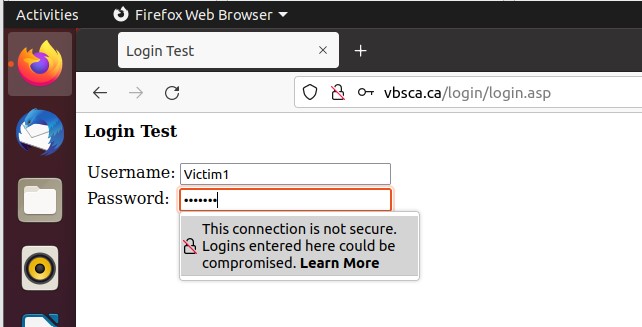
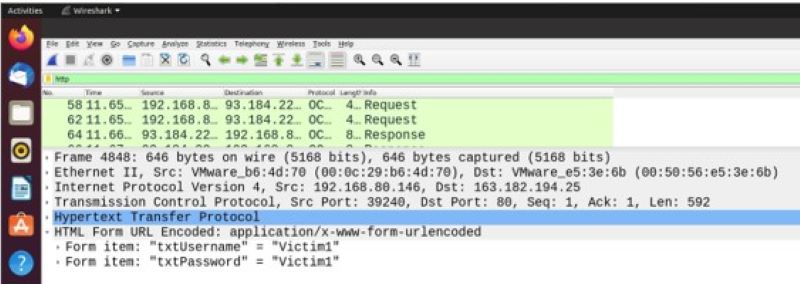
Now u have to generate on the victims side some traffic which will be captured on the attackers side.
In the last step u open your file where u have saved the captured traffic and look for the information u want. In this case there is shown a http login where u can see the username and password.
Used Hardware