Steghide
Summary
Steghide is a stenography program which can hide data in different kinds of image- and audio files. This can be useful if you want to send messages hidden to a second party. For this, it is important that both parties know the passphrase with which the message is encrypted. The result does not show any obvious changes in the file because the color- respectivly sample-frequencies are not changed.[1]
Requirements
- install steghide
- embed file
- cover file
- passphrase
Features
- compression of embedded data
- encryption of embedded data
- embedding of a checksum to verify the integrity of the extraced data
- support for JPEG, BMP, WAV and AU files
Description
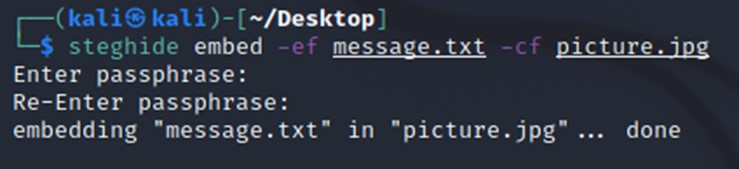
Embed
To hide a message in an JPEG: in this example the message to hide is the embed file (-ef) and the cover file (-cf) is picture.jpg
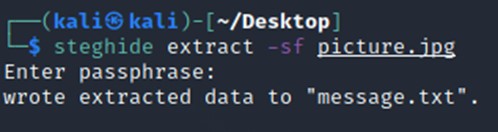
Extract
To extract the message.txt type following:
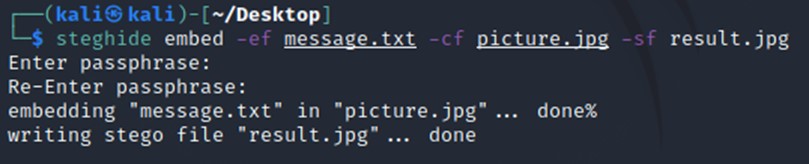
other details
There is the possibility to define a stegofile (-sf) for the output, so you do not override the coverfile.
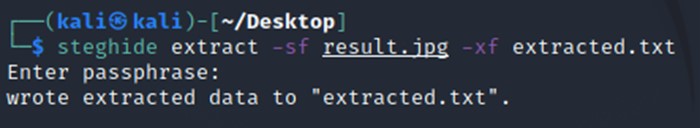
To extract into a specific file, you can also enter an extract file (-xf)
Detection
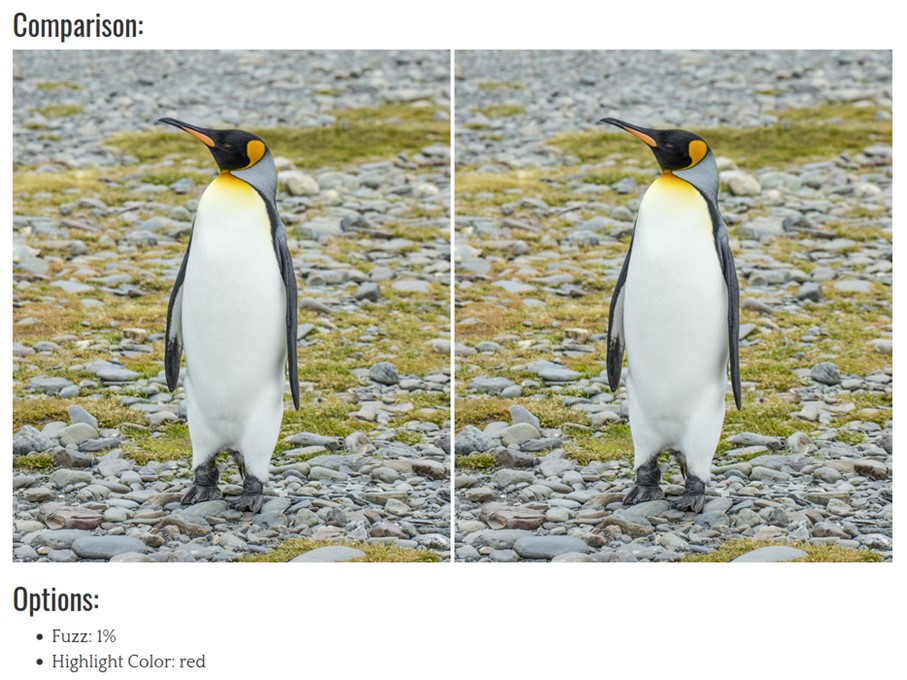
If you have the original .jpeg and the manipulated .jpeg you can compare those two with an online image comparison ([1]) Here you can upload both images and you can see where the information is embedded.
On the left side you see the original picture.jpg and on the right side the result.jpg
The hidden information is placed in the details of the image to prevent that it is visible in the result.jpg here highlighted in red.
Commands
steghide version 0.5.1 [1]
the first argument must be one of the following:
embed, --embed embed data extract, --extract extract data info, --info display information about a cover- or stego-file info <filename> display information about <filename> encinfo, --encinfo display a list of supported encryption algorithms version, --version display version information license, --license display steghide's license help, --help display this usage information
embedding options:
-ef, --embedfile select file to be embedded -ef <filename> embed the file <filename> -cf, --coverfile select cover-file -cf <filename> embed into the file <filename> -p, --passphrase specify passphrase -p <passphrase> use <passphrase> to embed data -sf, --stegofile select stego file -sf <filename> write result to <filename> instead of cover-file -e, --encryption select encryption parameters -e <a>[<m>]|<m>[<a>] specify an encryption algorithm and/or mode -e none do not encrypt data before embedding -z, --compress compress data before embedding (default) -z <l> using level <l> (1 best speed...9 best compression) -Z, --dontcompress do not compress data before embedding -K, --nochecksum do not embed crc32 checksum of embedded data -N, --dontembedname do not embed the name of the original file -f, --force overwrite existing files -q, --quiet suppress information messages -v, --verbose display detailed information
extracting options:
-sf, --stegofile select stego file -sf <filename> extract data from <filename> -p, --passphrase specify passphrase -p <passphrase> use <passphrase> to extract data -xf, --extractfile select file name for extracted data -xf <filename> write the extracted data to <filename> -f, --force overwrite existing files -q, --quiet suppress information messages -v, --verbose display detailed information
options for the info command:
-p, --passphrase specify passphrase -p <passphrase> use <passphrase> to get info about embedded data