Difference between revisions of "Unsecure Webservices: bWAPP vs. JuiceShop"
| Line 122: | Line 122: | ||
[[File:Bild23PWErgebnis.png|500px]] | [[File:Bild23PWErgebnis.png|500px]] | ||
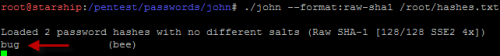
STEP 18: To crack the hashed password, the next step is to use a password cracker software such as John the Ripper | STEP 18: To crack the hashed password, the next step is to use a password cracker software such as John the Ripper. John the Ripper is a popular open source password cracking software. A number of password crackers are combined in one package. Password hash types are detected automatically, the password's output in clear text. | ||
[[File:Challenge1.9bWAPP.png|500px]] | [[File:Challenge1.9bWAPP.png|500px]] | ||
Revision as of 18:59, 28 January 2020
Introduction
The number of users of online services has increased significantly in the last years. Nowadays web applications represent a fundamental part in information technologies. Therefore the danger of attacks on the internet are growing and make so-called penetration tests necessary. A penetration test comprises a series of activities with which security gaps are recorded and identified. In the following seminar paper, two intentionally insecure web services are compared with each other. The focus of the practical part includes the testing of the world's most frequently used SQL-injection Attack. In this case attackers take advantage of specific weaknesses in order to gain access to confidential information. A variation of this SQL injection attack is described.
Author
Melanie Kaimer
Web Security Test-Application
Penetrating Testing
Penetrating testing is a targeted, permitted attempt to penetrate an IT system. The main objective is to detect and eliminate vulnerabilities in order to improve IT security. Vulnerabilities should be identified before they arise. Methods such as SQL injection, XML external entities (XEE) and cross-Site scripting (XSS) are very popular by hackers. For web applications, the Open Web Application Security Project (OWASP) offers materials for pentests.
SQL Injection Vulnerability
With the growing popularity of the World Wide Web, there was an increasing use for advanced technology and dynamic websites.
SQL injection vulnerability is one of the greatest dangers to confidentiality and integrity in Web applications and thus has been included in the OWASP Top 10 list as one of the most common vulnerabilities since its introduction. For example, attackers can insert malware into an SQL statement through an SQL injection vulnerability. The practical part of this thesis deals with the SQL injection attack. Attackers gain the ability to perform a series of actions if an SQL injection is applied to a vulnerable page. By exploiting this vulnerability, database contents can be added, edited, deleted or read.
bWAPP
The term bWAPP stands for buggy Web Applications. bWAPP belongs to the ITSEC-Games-Project and describes a deliberately extremely faulty web application. It was designed with the goal of ensuring IT security. Furthermore, it has a gaming character and should serve as a fun factor in addition to training.
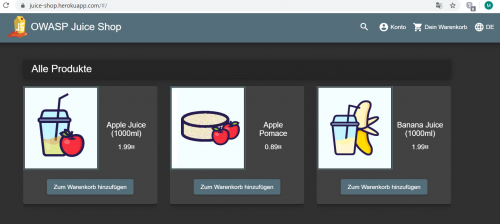
OWASP Juice Shop
At first glance, the OWASP Juice Shop looks like an inconspicuous online shop for fruit juices. The Juice Shop was designed in 2014 and is a so-called 'online juice shop' for safety training. Two years after its foundation, Juice Shop was submitted and accepted as an OWASP tool project. This step made the Juice Shop accessible to a large community of users within a very short time.
Practical demonstration Step-by-Step guideline
For the practical demonstrations SQL injection is chosen. This hacking method will be tested on both insecure web applications to get a clear comparison. SQL-Injection is one of the most common methods on the top 10 list of OWASP and therefore it is considered as a very serious threat.
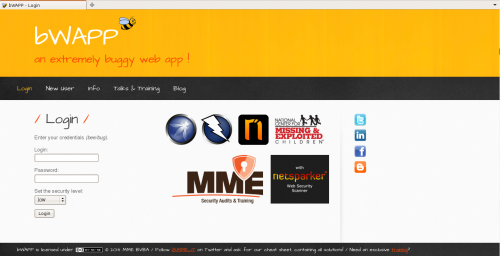
bWAPP Challenge
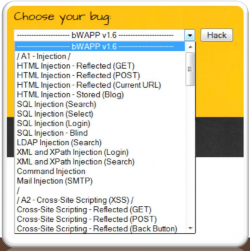
STEP 1: The challenge is selected first. Afterwards, the user is redirected to the next web page to be able to execute the challenge.
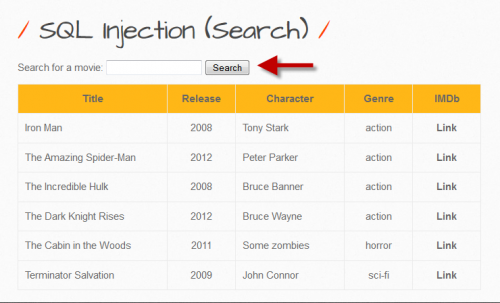
STEP 2: In order to be able to select a challenge, there is a registration requirement. However, users have the possibility to register with any data they wish. Afterwards, an SQL injection task can be selected from various 'bugs'. For the selected (GET/SEARCH) SQL-Injection, information about available movies is displayed in a table when entering a movie title. Here you can search for one or more movies. As a result of the search, the movie details are displayed. If the input button is clicked without entering a search term, all movies are displayed. The set goal is to get a user password.
STEP 3: If you enter a search term such as 'iron', for example, all data will be displayed as follows.
STEP 4: A wrong input like 1' leads to an syntax error. As a result, you can see that the URL parameter 1' is definitely vulnerable to an SQL injection:
File:Bild2SQLSyntaxFehler.png |500px STEP 5: After recognizing the syntax error the URL is edited. action=search is deleted and replaced by order by 1 -- -.
STEP 6: From the output you can see that the URL parameters are definitely vulnerable to an SQL injection.
STEP 7: Try the numbers until a so-called out of table message is displayed. After a short time of trying - by increasing the number by 1 again and again until an error message is displayed - it is recognized that there are 7 columns. In the example case shown, it is an easy game, because there are 7 columns and not 600 for example.
STEP 8: The attempt to display confidential information begins with an SQL Union statement. This statement allows you to merge database tables. First you must ensure that the same number of columns is used as in the original SQL statement.
STEP 9: The result shows that column 5 corresponds to one character.
STEP 10: Again, the URL is changed to access the desired password.
STEP 11: The result ejects the character bWAPP.
STEP 12: From this point on it is possible to visualize the current database version:
STEP 13: Table names should be printed:
STEP 14: Certain characters of the table should now be printed.
STEP 15: Linking table names from the database.
STEP 16: In the following step the contents of the columns-output is 'User'.
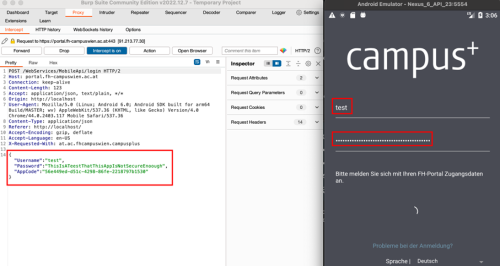
STEP 17: The goal is to get the password, therefore the URL is changed so that at best the login and password of the user are displayed. The result gives some interesting values. The database is exploited by retrieving confidential data. The value of the password is stored in a hash state and cannot yet be retrieved.
STEP 18: To crack the hashed password, the next step is to use a password cracker software such as John the Ripper. John the Ripper is a popular open source password cracking software. A number of password crackers are combined in one package. Password hash types are detected automatically, the password's output in clear text.
Juice Shop Challenge
Conclusion
Tools like bWAPP and OWASP Juice Shop are very helpful and interesting to try out hacking tasks in different levels of difficulty in a playful manner. With the unstoppable development of technology and today's abundance of information it becomes more important to be well informed about the dangers that came with the World Wide Web.
Further information to this article can be found in my paper: seminar paper