WiFI Pineapple Mark VII: Cracking WPA/WPA2-PSK with a dictionary/brut force attack
Jump to navigation
Jump to search
Summary
This Documentation will give you a guide how to retrieve a WPA2-PSK password with the Wi-Fi Pineapple Mark VII combined with the Linux Tool aircrack-ng. The Wi-Fi Pineapple Mark VII will be used to deauthenticate the clients of the victim's Wi-Fi. Simultaneously, the Wi-Fi Pineapple Mark VII will capture the 4-way handshake between client and access point and saves it as a PCAP or Hashcat file. This guide will use Linux to demonstrate how to use aircrack-ng.
Requirements
Mandatory
GNU/Linux
- Install aircrack-ng suite:
sudo apt install aircrack-ng
To complete these steps, you must have followed WiFI Pineapple Mark VII: Initial Setup before.
Optional
Hashcat
- Clone GIT repository:
git clone https://github.com/hashcat/hashcat.git - Build:
cd ./hashcat && make && make install - Link:
sudo ln -s ./hashcat /usr/local/bin/hashcat
Description
Step 1
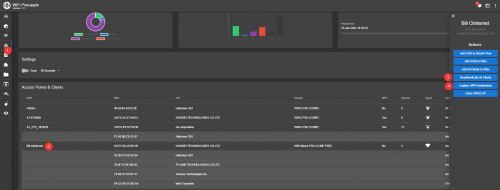
Log in to Wi-Fi Pineapple Web GUI and open the tab Reacon
echo foo echo bar
Step 2
Make sure to read
- War and Peace
- Lord of the Rings
- The Baroque Cycle
Used Hardware
Courses
- Campus Cyber Security Team WiFi Hacking 28.01.2022