Awox CamLight Pentest
Summary
DRAFT - This is a report on pentest - the information gathering and vulnerability scans - performed on Awox CamLight.
Requirements
- Operating system: Kali Linux 2021.1 amd64, Parrot Security 4.10 amd64
- AWOX CamLight Hardware
- AWOX CamLight Smartphone application (IOS or Android)
Disclaimer: all possible examples and tests done have been done in VMWare in a Kali Linux and ParrotOS VM.
Description
In an effort to evaluate the Awox CamLight and perform a pentest, there are certain steps to be followed. A penetration test in general consists of several stages:
- Planning and reconnaissance
This is where the attacker/tester gets familiar with the target and gathers as much information as possible. Finding out what the network topology is (in case of networks), what the IP addresses, domain details or possible mail servers are etc.
- Scanning
This is the phase where you interact with the target, in our case the target host CamLight. Probes are sent to the target and responses are recorded. This includes scanning the target with various scanning tools, identification of open ports, services that are running and much more. The goal is to identify vulnerable ports, functions or services.
- Gaining Access
In this step the vulnerabilities are exploited to gain access to the target. However, not all vulnerabilities will lead to this stage, only those exploitable enough to grant access to the target host.
- Maintaining access
For example to make sure that access is maintained after reboot or modifications of the target. This would be the case for attackers whose goal is to stay in a system and collect information over longer periods of time to catch the perfect moment to exploit.
- Exploitation
This would be the stage where an attacker/tester does the "actual damage". The goal is to get their hands on data, compromise a system, launch various attacks etc. During authorized penetration testing, this will take place in a very controlled environment.
- Evidence collection and reporting
This is the stage where the results of the penetration test are collected, evaluated and handed in to whoever ordered the security evaluation.
In this pentest, the focus lies on information gathering and vulnerability scans of the target host, with possible attempts to exploit the vulnerabilities found.
Planning and reconnaissance
To list the known information about the camera, first step would be to find out, how it works and what are the specifications from the vendor. It should be noted that the camera can no longer be found in the AwoX official store, which would indicate that it is no longer sold, and therefore there isn't much information on the vendor's page, only the resellers. A brief documentation of the camera can also be found here. The camera connects over WiFi. You set it up in your home/office with your smartphone app and let it connect to the same WiFi that your phone is using. Disclaimer: The IOS AwoX CamLightapp does NOT work. If you own an IOS smartphone, you could still try the app, but if it doesn't work for you, the way to go would be to install an android emulator on your PC and then download the android there and perform the connection setup through there, since the app seems to no longer work properly for IOS - the reason for this could possibly be that the Camera is no longer sold, thus the application is no longer kept up to date.
To gather information about the camera itself, we need it to be connected to power and to WiFi and have your scanning tools (in our case the Kali Linux VM) available to access devices in that subnet. The IP address of the camera in this demonstration will be 192.168.0.130, which was concluded from excluding all the other known devices on the network and also turning the camera on and off to see which IP address is new.
Scanning
Starting with nmap, the following results have been gathered:
$ sudo nmap -O 192.168.0.130
Nmap scan report for 192.168.0.130 Host is up (0.043s latency). Not shown: 996 closed ports PORT STATE SERVICE 23/tcp open telnet 554/tcp open rtsp 843/tcp open unknown 5001/tcp open commplex-link MAC Address: 7C:DD:90:AF:4E:7D (Shenzhen Ogemray Technology) Device type: general purpose Running: Linux 2.6.X|3.X OS CPE: cpe:/o:linux:linux_kernel:2.6 cpe:/o:linux:linux_kernel:3 OS details: Linux 2.6.32 - 3.5 Network Distance: 1 hop
$ sudo nmap -sA 192.168.0.130
Nmap scan report for 192.168.0.130 Host is up (1.1s latency). All 1000 scanned ports on 192.168.0.130 are unfiltered MAC Address: 7C:DD:90:AF:4E:7D (Shenzhen Ogemray Technology) Nmap done: 1 IP address (1 host up) scanned in 5.67 seconds
$ nmap -Pn -sV --script vuln 192.168.0.130
Host discovery disabled (-Pn). All addresses will be marked 'up' and scan times will be slower. Starting Nmap 7.91 ( https://nmap.org ) at 2021-06-21 23:45 CEST Pre-scan script results: | broadcast-avahi-dos: | Discovered hosts: | 224.0.0.251 | After NULL UDP avahi packet DoS (CVE-2011-1002). |_ Hosts are all up (not vulnerable). Nmap scan report for 192.168.0.130 Host is up (0.060s latency). Not shown: 967 closed ports, 29 filtered ports PORT STATE SERVICE VERSION 23/tcp open telnet security DVR telnetd (many brands) 554/tcp open rtsp | fingerprint-strings: | HTTPOptions, RTSPRequest: | RTSP/1.0 200 OK | CSeq: 0 | Server: CameraRtspServer | Public: OPTIONS, DESCRIBE, SETUP, PLAY, TEARDOWN, GET_PARAMETER, SET_PARAMETER | SIPOptions: | RTSP/1.0 200 OK | CSeq: 42 | Server: CameraRtspServer |_ Public: OPTIONS, DESCRIBE, SETUP, PLAY, TEARDOWN, GET_PARAMETER, SET_PARAMETER 843/tcp open unknown 5001/tcp open commplex-link? 1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service : SF-Port554-TCP:V=7.91%I=7%D=6/21%Time=60D108A6%P=x86_64-pc-linux-gnu%r(RTS SF:PRequest,86,"RTSP/1\.0\x20200\x20OK\r\nCSeq:\x200\r\nServer:\x20CameraR SF:tspServer\r\nPublic:\x20OPTIONS,\x20DESCRIBE,\x20SETUP,\x20PLAY,\x20TEA SF:RDOWN,\x20GET_PARAMETER,\x20SET_PARAMETER\r\n\r\n")%r(HTTPOptions,86,"R SF:TSP/1\.0\x20200\x20OK\r\nCSeq:\x200\r\nServer:\x20CameraRtspServer\r\nP SF:ublic:\x20OPTIONS,\x20DESCRIBE,\x20SETUP,\x20PLAY,\x20TEARDOWN,\x20GET_ SF:PARAMETER,\x20SET_PARAMETER\r\n\r\n")%r(SIPOptions,87,"RTSP/1\.0\x20200 SF:\x20OK\r\nCSeq:\x2042\r\nServer:\x20CameraRtspServer\r\nPublic:\x20OPTI SF:ONS,\x20DESCRIBE,\x20SETUP,\x20PLAY,\x20TEARDOWN,\x20GET_PARAMETER,\x20 SF:SET_PARAMETER\r\n\r\n"); Nmap done: 1 IP address (1 host up) scanned in 152.36 seconds
After performing nmap and trying some other Kali tools but not discovering any more useful information, openVAS was used, which is a vulnerability scanner that can be installed additionally on Kali. To install openVAS the following commands are needed:
apt update apt dist-upgrade apt upgrade apt install openvas gvm-setup gvm-start
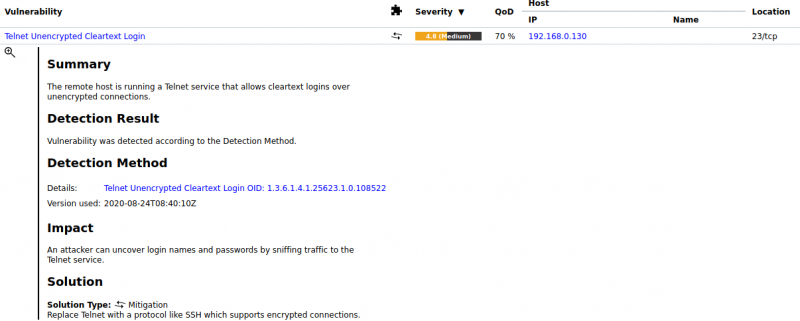
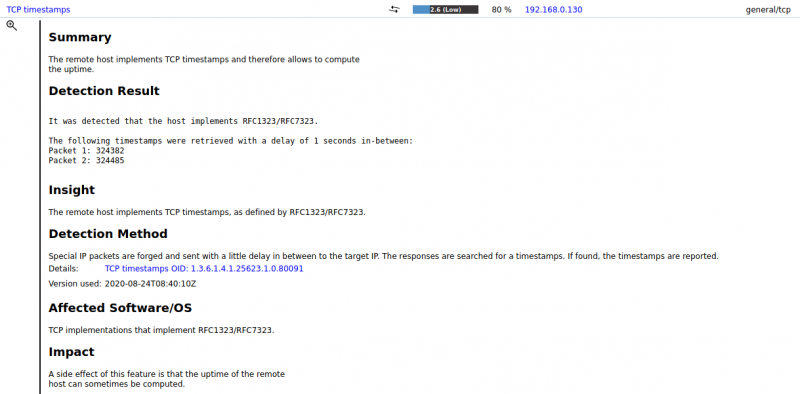
Afterwards just launch it on localhost in browser on 127.0.0.1:9392, add a target (our camera) and set up tasks to perform scans. The results of a full scan are shown below, however it mostly showed what we already knew, which is the Telnet port:
After openVAS we also tried the Nessus vulnerability scanner, which can be downloaded here. This did not offer any new information and the setup was quite lengthy, but it offers a nice GUI for possible newbie users.
Gaining access
When trying to telnet to the camera, you are prompted with a username and password, which we don't know. Guessing several admin-password combinations was also not met with success. The vulnerability here would thus be: being able to listen on the plaintext telnet connection (which was successfully done with Wireshark) if the admin would access the camera. The SSH port is not open for access (telnet connection failed, plus no scans show the port), which would solve this vulnerability from the admin's perspective.
- Attempt at Metasploit Telnet Login brute force exploit:
$ msfconsole msf6 > use auxiliary/scanner/telnet/telnet_login msf6 auxiliary(scanner/telnet/telnet_login) > set BLANK_PASSWORDS false msf6 auxiliary(scanner/telnet/telnet_login) > set PASS_FILE /usr/share/wordlists/metasploit/unix_passwords.txt msf6 auxiliary(scanner/telnet/telnet_login) > set RHOSTS 192.168.0.130 msf6 auxiliary(scanner/telnet/telnet_login) > set THREADS 254 msf6 auxiliary(scanner/telnet/telnet_login) > set USER_FILE /usr/share/wordlists/metasploit/unix_users.txt msf6 auxiliary(scanner/telnet/telnet_login) > set VERBOSE true msf6 auxiliary(scanner/telnet/telnet_login) > run
Results: no match found
This result was of course expected, bots need days and months to brute force telnet passwords of IoT devices, the important factor here is how much time one is willing to invest. Telnet brute force attacks on IoT devices are very popular and common nowadays, that's why the importance of a good username and password is so prevalent.
- Attempt at Hydra Telnet Login brute force exploit:
$ hydra -L /usr/share/wordlists/metasploit/unix_users.txt -P /usr/share/wordlists/metasploit/unix_passwords.txt 192.168.0.130 telnet $ hydra -L /usr/share/wordlists/metasploit/unix_users.txt -P /usr/share/wordlists/rockyou.txt 192.168.0.130 telnet
Elapsed time: several days
Results: not successful
Used Hardware