Bettercap
Summary
This documentation is about bettercap, more specifically the functionality related to Arp Spoofing and Bluetooth conncetions. The bettercap tool is described on it’s website as "the Swiss Army knife for WiFi, Bluetooth Low Energy, wireless HID hijacking and Ethernet networks reconnaissance and MITM attacks".[1] In this Wiki entry, bettercap installed on a Raspberry Pi Model 4 B.
Requirements
- Raspberry Pi Model 4 B
- Operating system: Raspbian Buster
- Packages: build-essential, libpcap-dev, libusb-1.0-0-dev, libnetfilter-queue-dev
- BLE device (MiPow Playbulb Candle)
Installation
Step 1 Install the prerequisites
sudo apt install golang git build-essential libpcap-dev libusb -1.0-0-dev libnetfilter-queue-dev
Step 2 Install bettercap
go get github.com/bettercap/bettercap cd go/src/github.com/bettercap/bettercap make build sudo make install
Step 3 Run bettercap
sudo bettercap
If there is are any problems or you want to install the newest Bettercap version follow this documentation.
Show the available commands and modules
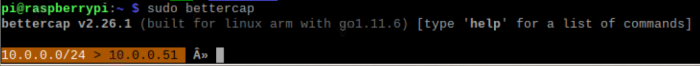
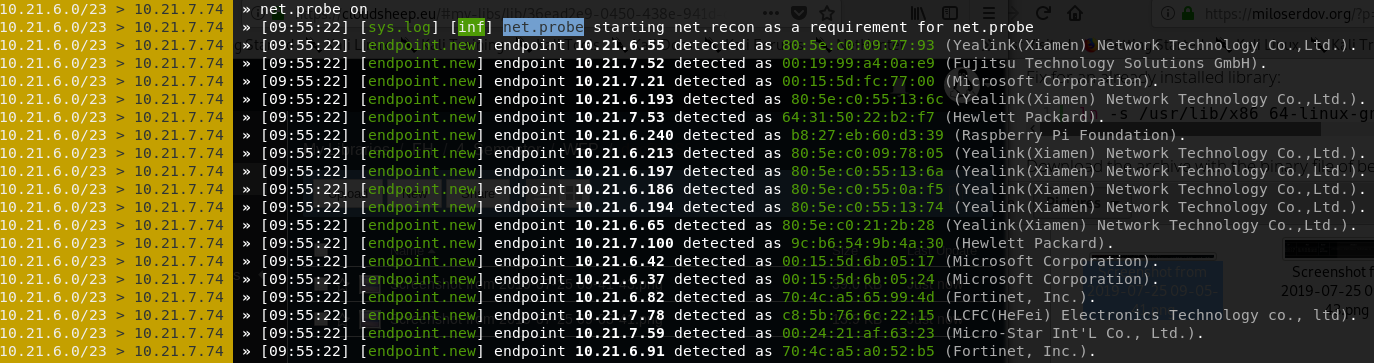
The following shows the output after starting bettercap. Note the subnet and the IP address of the Raspberry Pi are shown.
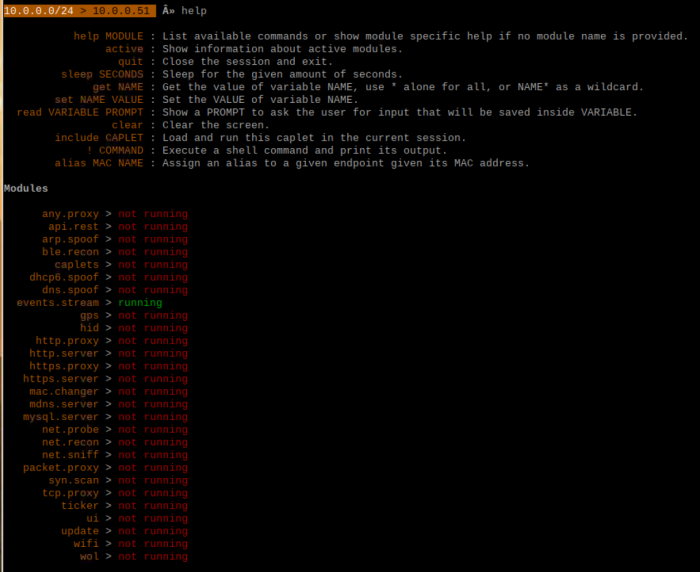
After bettercap is running, a list of available commands and modules can be displayed using the command
help
ARP Spoofing with Bettercap
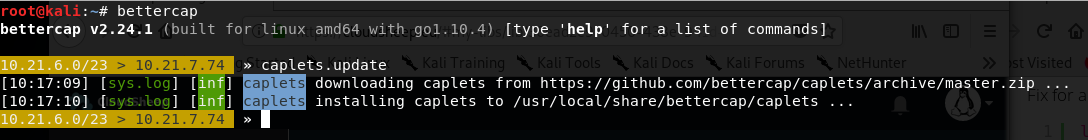
Step 1: Start bettercap & update caplets
bettercap caplets.update
Step 2: Scan local Network
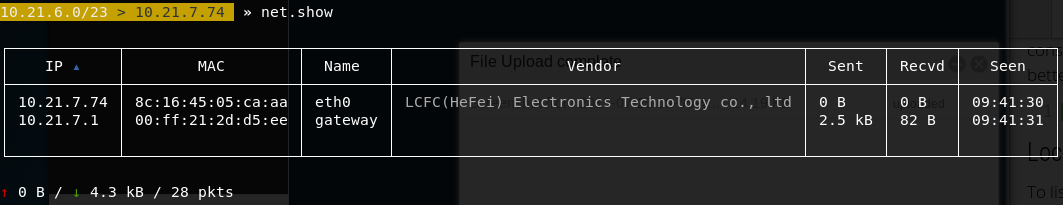
Passive: List already detected hosts on the network (own arp cache):
net.show
Active: Search active hosts on the network
net.probe on
Stop detection:
net.probe off net.recon off
List available hosts again:
net.show
Step 3: ARP Poisoning
By default, the arp poisoning attack is performed on the whole subnet which is pretty conspicuous. If you want to target single hosts on the network you can define a target variable like this:
set arp.spoof.targets 'IP'
Enable/Disable ARP poisoning:
arp.spoof on arp.spoof off
Sniff client actions:
net.sniff on
BLE with Bettercap
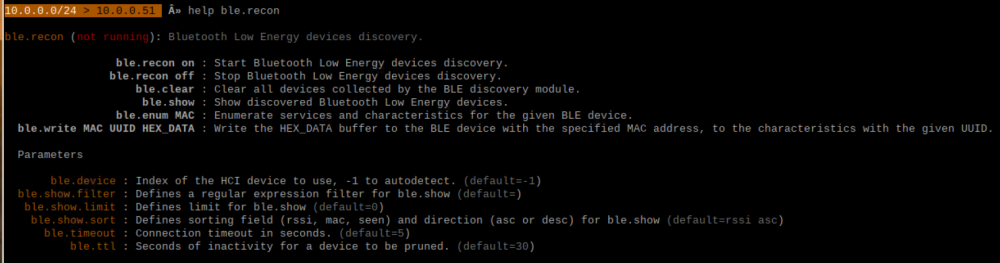
Enter the module name to gain further help
help ble.recon
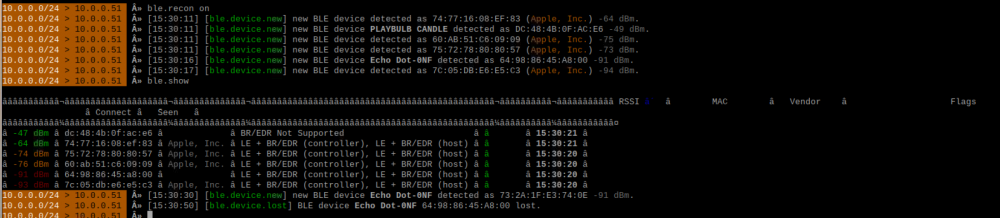
Turn on ble.recon and list the available BLE devices
ble.recon on ble.show
Various information is available from these commands such as the RSSI, the MAC address (BD_ADDR), the vendor, the flags that show which version of Bluetooth is supported, whether it is possible to connect to the device and time discovered. The Playbulb Candle has been discovered and from the output it possible to see that it only supports BLE as BR/EDR is not supported.
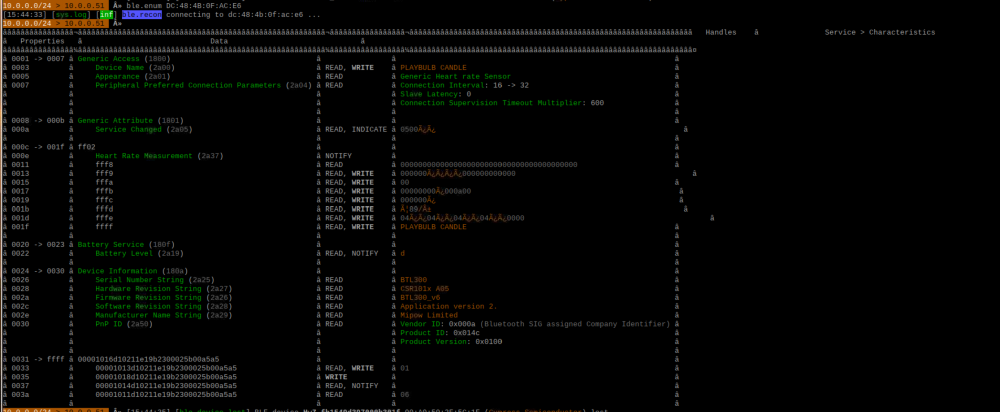
To list the services and characteristics of the a device use the command
ble.enum MAC
In this case for the Playbulb Candle
ble.enum DC:48:4B:0F:AC:E6
Attempts to change the values of characteristics can be made with
ble.write MAC UUID HEX_DATA
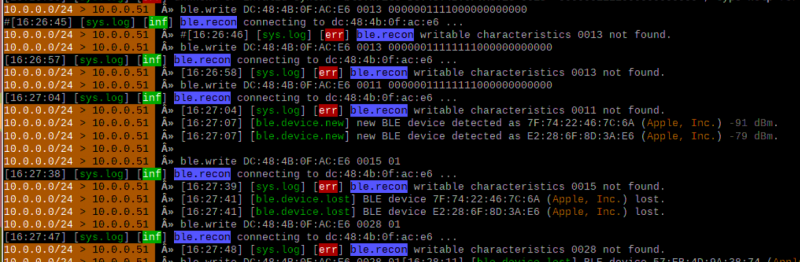
Results can be seen in the following screenshot.
To end BLE scanning using bettercap, use the command
ble.recon off
Used Hardware
- Raspberry Pi 3, Model B+, WLAN, BT
- Raspberry Pi 3 Model B+ V1.2
- Raspberry Pi® 3 Model B, 1GB LPDDR2 RAM
- MiPow Playbulb Candle
Courses
- Vertiefendes Wahlfachprojekt (2019, 2020)
- Bachelorarbeit 1 (2019, 2020)