Bitcoin Wallets
Introduction
The need to get rid of centralized financial systems and bureaucracy and reduce fraud and forgery in commercial transactions and others was the reason behind the appearance of the basic idea of Blockchain technology. Blockchain has been around since the 1990s. In 1991, Blockchain was originally described by a group of researchers. The application of this technology was originally intended to timestamp digital documents so that it is not possible to backdate them or to tamper with them, like a digital notary [1]. In 2008 a study was published under the title Bitcoin: A Peer-to-Peer Electronic Cash System, under the pseudonym Satoshi Nakamoto, in which Blockchain‘s technology was applied to electronic currency, and then in 2009 the Bitcoin cryptocurrency blockchain network was created [2]. Bitcoin supersedes fiat currency in multiple dimensions because it can be transferred internationally without any limits, transactions have either no fees or a very low fee, currently, it does not need any personal information, is transparent as every user has a copy of the public ledger, and secure as the underlying cryptographic algorithm provides security [3].
Blockchain and Bitcoin
Blockchain
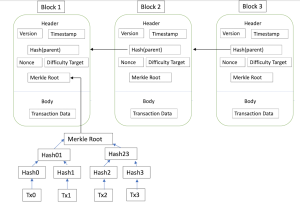
Blockchain is a data structure that makes it possible to create a digital ledger of transactions and share it among a distributed network of computers, continuously updated simultaneously and secure with encryption. Anyone can access and get the same information.[1] How does Blockchain work? Each block contains some data, the hash of the block and the hash of the previous block. The hash of the block is calculated as a Merkel Tree.
The Merkel Tree is sort of hash binary tree that allows for the speedy and efficient summarization of enormous volumes of data. In addition, the integrity of the data is controlled at the same time. The entire data is made of several documents where for each leaf node a hash of one of these documents is created. Then the hash is calculated recursively from the bottom up. Finally, the value of the Merkle Tree Root represents the hash value of the entire data block.[4]
The data that is stored inside a block depends on the type of blockchain. The Bitcoin blockchain for example stores the details about a transaction such as the sender, receiver, and amount of coins. A block also has hash, you can compare a hash to a fingerprint. It identifies a block and all of its contents, and it is always unique. Once a block is created, its hash is being calculated. Changing something inside the block will cause the hash to change. So, in other words, hashes are very useful when you want to detect changes to blocks. If the fingerprint of the block changes, it no longer is the same block.
The third element inside each block is the hash of the previous block. This effectively creates a chain of blocks, and it is this technique that makes a blockchain so secure. The first block is special; it cannot point to previous blocks because it is the first one, it is called “Genesis Block”.
Changing a single block will make all following blocks invalid. But using hashes is not enough to prevent tampering. Computers these days are very fast and can calculate hundreds of thousands of hashes per second, so to mitigate this, blockchain have something called proof-of-work, which is a mechanism that allows down the creation of new blocks. In other words when new chain was created the proof-of-work on blockchain concept is the consensus mechanism on so-called miners.[1] In the case of Bitcoin, it takes about 10 minutes to calculate the required proof-of-work and add a new block to the chain. This mechanism makes it very hard to tamper with the blocks, because if you tamper with one block, you’ll need to recalculate the proof-of-work for all the following blocks [5]. So, the security of a blockchain comes from its creative use of hashing and the proof-of-work mechanism [5]. But there is one more way that blockchain secure themselves and that is by being distributed. Instead of using a central entity to manage the chain, blockchain uses a peer-to-peer network and anyone is allowed to join [5]. When someone joins this network, he gets the full copy of the blockchain .
What happens when someone creates a new block? The new block is sent to everyone on the network. Each node then verifies the block to make sure that is has not been tampered with. If everything checks, each node adds this block to their own blockchain. All the nodes in this network create consensus. They agree about what blocks are valid and which are not [5]. Blocks that are tampered with will be rejected by other nodes in the network [5]. So, to successfully tamper with a blockchain you will need to tamper with all blocks on the chain, redo the proof-of-work for each block and take control of more than 50% of the proof-of-work network. Only then will your tampered block become accepted by everyone else. This is almost impossible to do. The blockchain has complete information about different user addresses and their balances right from the genesis block to the most recently completed block. The blockchain was designed so these transactions are immutable, meaning they cannot be deleted. The blocks are added through cryptography, ensuring that they remain meddle-proof: The data can be distributed, but not copied. [1]
-
There are basically three types of blockchains. The use case will determine which type of blockchain is needed.
- Public Blockchains In a public blockchain, a user can become a member of the blockchain network. This means they can store, send and receive data after downloading the required software on their device. Allowing anyone to read and write the data stored on the blockchain as it is accessible to everyone in the world. A public blockchain is completely decentralized. The permissions to read and write data onto the blockchain are shared equally by all connected users, who come to a consensus before any data is stored on the database. The most popular example of a public blockchain is Bitcoin. The digital currency allows users to use a platform for making transactions directly between them.
- Private Blockchains In a private blockchain, permission to write, send and receive data is controlled by one organization. Private blockchains are typically used within an organization with only a few specific users allowed to access it and carry out transactions. The organization in control has the power to change the rules of a private blockchain and may also decline transactions based on their established rules and regulations. An example of this is a blockchain deployed by a corporation to collaborate with other divisions or a few permissioned participants.
- Consortium Blockchains A consortium blockchain, also called permissioned blockchain can be considered as a hybrid model between the low trust offered by public blockchains and the single highly trusted entity model of private blockchains. Instead of allowing any user to participate in the verification of the transaction process or on the other side just allowing one single company to have full control, in a consortium blockchain a few selected parties are predetermined. It only allows a limited number of users the permission to participate in the consensus process.For example, imagine a group or network of ten banks, each of which is connected to the blockchain network. In this example, we could imagine that for a block to be valid, seven of the ten banks have to agree.
-
Some of the use cases of blockchain technology currently being explored across the world :[6]
- Use Case 1: Banking One of the essential issues in banking is the security, therefore the blockchain is suitable for this purpose. Furthermore, its use can reduce the costs and speed of banking operations, making them more profitable and convenient for customers.
- Use Case 2: Insurance The insurance industry suffers from many challenges such as inefficient exchange of data, fraudulent claims, high transaction costs, and slow claims processing. Blockchain can help the industry address these issues. With the blockchain, the exchange of data will be instant and can be carried out securely, which will increase the proportion of claims in the process. With no room for data manipulation, the rate of fraudulent claims is bound to fall.
- Use Case 3: Healthcare When technology is used, the exchange of health information becomes easier and safer, and it also helps eliminate the difficulty of keeping records without errors.
- Use Case 4: Identity Validation Blockchains simplify online verification and identity verification processes easily and quickly. A central repository of people's identities can be created using this technology. They can verify this identity with a blockchain once and then use it again to authenticate transactions for different service providers. A repository of documents such as birth certificates can also be created. With a secure repository in place, authorized personnel can be granted secure access to the certificate.
- Use Case 5: Cryptocurrencies Blockchain has introduced very dramatic changes into the financial field by creating cryptocurrencies, which rival fiat currencies in their use. The first-ever cryptocurrency transaction happened in 2009. Satoshi Nakamoto sent Hal Finney 10 Bitcoins, on January 11, 2009, Hal Finney tweeted, “Running bitcoin”.
Bitcoin
Research on digital cash emerged in the 1980s, and in the 1990s DigiCash Inc. made the first attempt to provide a cryptocurrency system. After that, other systems began to appear, such as DigiCash and b-money, but they suffered from many problems, especially since they were not using the blockchain technology. In 1991 Haber and Stornetta proposed the first Blockchain concept, which was intended to numerically seal digital records, however this technique was not effective due to the problem of the temporal independence of each record. Finally, Nakamoto implemented the first true blockchain and used it as the core technology of the Bitcoin cryptocurrency system.[7] Bitcoin is a digital currency and that means it is implemented with a lot of software. This software is called Bitcoin improvement proposals (BIPs) and it established the rules to which everyone should agree if they want to use Bitcoin. This includes how large a block is, what rewards miners get, how fees are calculated, etc. Bitcoin runs over a P2P network, which allows the data of all nodes to achieve agreement in a very flexible way. Bitcoin uses the network to quickly transmit data between all connected nodes. The process in which Bitcoin uses the network to broadcast data between all nodes connected to is called the flood, which continues until the nodes receive the broadcast data. data flooding include IP addresses of the nodes, newly generated transactions, and blocks of verified transactions that extend the blockchain. Nodes in the Bitcoin P2P network are defined based on their tasks. The main tasks are:[7]
- transaction generation,
- block/transaction routing,
- block/transaction verification, and
- transaction mining.
-
There are two types of nodes:
- Full node is a node that can perform all the functions, which continuously maintains a copy of the full blockchain making it able to verify any transaction without reference to other nodes. It also has a BTC wallet that can create transactions and calculate the value of BTC owned by the node.
- Simplified payment verification (SPV) nodes or lightweight nodes are a node does not store a full copy of the blockchain that is why they need support from full nodes when they want verifying a transaction.
Some nodes may perform only one particular function. The items that participate in the mining process are referred to as mining nodes while other items that create transactions are referred to as wallets. In most Bitcoin software applications, all nodes are handled evenly and can be identified by their IP addresses.[7]
Bitcoin transaction
Bitcoin transaction is the transfer of an amount of BTC ownership rights from the wallet of the buyer (from one address ) to the wallet of the seller (to another address), in exchange for a product or service. There are two types of Bitcoin transaction: Standards and Nonstandard transactions. The list of standards transactions is described as follows.[7]
- Pay to Public Key Hash (P2PKH).
- Pay to Public Key.
- Multisignature (MultiSig).
- Pay to Script Hash (P2SH).
- Data Output.
Nonstandard transactions use more complicated scripts that aim to provide higher complexity and security. Sometimes these transactions may be the result of bugs or mistakes which leads to loss of BTC.
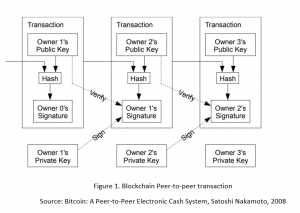
How does the transactions work?
Bitcoin uses the public-key cryptography to ensure the integrity of transactions created on the network. In order to be able to transfer Bitcoin, each user owns a pair of public key and private key and thus can control the amount of bitcoin they own. A public key is a string of characters (letters and numbers) that a user must share it with the other users so that can be able to receive funds. While a private key must be kept secret because it controls the amount of Bitcoin owned or received by the user. The user signs the transactions using his private key to transfer the value to a new owner, and this transaction is then broadcast over the network to be added to the blockchain. And then comes the last stage, which is the mining stage, where the transaction is added to the Blockchain after confirming that it is correct, and so that it is public for all users.
Bitcoin Mining
A miner is a node on the bitcoin network which installed and runs a special Blockchain mining software to communicate securely with the other nodes on the network. The process of mining bitcoins consume a lot of computing power, hence, it requires a special set of hardware and software that works well for that purpose [4]. Each block in the Blockchain is created by one of those miners, whose goal it is, to solve a crypto task that verifies the creation of a block. As compensation, the fastest miner whose block is actually attached to the Blockchain receives a certain number of bitcoins. A new mined block will get broadcasted to the network where each node validates it by first checking the proof of work and if the merkle tree coincides with the transactions listed inside the block. A transaction is only confirmed when a certain number of new blocks got added to the block the transaction is located. This is called maturity and the Bitcoin documentation recommends 6 block as a maturity level [8]. Part of the Block header is the Nonce. Nonce stands for a Number Used Once, meaning that the block´s hash meets certain criterion to be valid. This criterion in Blockchain Hashes is, that the hash must include a predefined number of leading zeros. The number of zeros the hash needs to have, is defined by the Difficulty Target. The higher the Difficulty Target, the more leading zeros the hash must provide. A nonce is a random number that enables to block to provide a valid hash. There is no other way than to calculate that number manually. The miner typically begins with a Nonce value of 1 and keep increasing it until the resulting hash satisfies the required threshold. As a result, it can take a fair amount of repetitions to obtain the appropriate hash with the demanded leading zeros. The Bitcoin system anticipates a block to be generated in 10 minutes and adapt the Difficulty Target to meet that time [4]
After Bitcoin, many cryptocurrency systems emerged, where Blockchain technology is a common property shared by many newly emerging cryptocurrency systems. This system looks like Bitcoin with some differences like block size and coin width etc. The cryptocurrency market is similar to other exchange markets where cryptocurrencies are traded with multiple trading platforms. However, the digital currency market is distinguished by the fact that it is not regulated by a government or a specific party, and trading in it is all the time and all over the world, which the nature of the encrypted currency allows, which results in a more volatile market due to the high and low prices Cryptocurrency permanently.
Bitcoin's Lightning Network
Bitcoin may become the basis of the financial system one day and to achieve this it has to overcome the big obstacle it faces, which is scalability. When compared to other transactions Bitcoin can handle up to 7 transactions per second with the current block size of 1 Mb. Clearly, the main blockchain is not very scalable. A new technique called the Lightning network is coming out to solve the scalability problem. The key idea is that small everyday transactions do not have to be stored on the main blockchain. So how does it work? Creating a transaction on the blockchain for a small fee is really overkill, however, with the lightning network, for example, user1 can set up a payment channel with the user2. To do that, both user2 and user1 deposit a certain amount of Bitcoin in what is called a Multi-signature address. The multi-signature address is basically like a safe that can only be opened when both parties agree. Opening the payment channel, which occurs on the main blockchain, makes a balance sheet reports how much money in the address has to be distributed and that guarantees full transparency. Now the channel is open, user1 can order what he wants to buy from user2, by changing the balance sheet. He subtracts the cost from his balance and adds it to user2’s balance. User1 and user2 now sign the updated balance sheet with their private keys, then they each keep a copy of it, but they do not do anything else with it. User1 can keep ordering as long as he has a balance in the payment channel. There is no limit because this happens away from the main blockchain. The payment channel can be closed at any time by either user1 or user2, all they have to do is take the latest balance sheet, which was signed by both users, and transmissions it to the Bitcoin network. After that by the mining stage, it will be checked if everything is correct (validate the signatures) and then transfer money according to the balance sheet. Whereupon only one transaction will be made on the Bitcoin blockchain. And thus, the reduction of the load on the main blockchain happened, all we need is two transactions, one for opening the payment channel and another one to close it. It is also very safe. The system ensures that only the latest signed balance sheet can be used to unlock money and because both parties have a signed copy of the balance sheets, they can release the funds at any time, even if the other does not want to cooperate anymore. Also, you do not need to open a direct payment channel with everyone you want to send bitcoin to. In the lightning network, your payment tries to find a route from person A to person B and it tries to do this with the least amount of intermediates and the least amount of fees. This further reduces the strain on the blockchain, but it requires the intermediates to have enough money in the payment channels. After Bitcoin, many cryptocurrency systems emerged, where Blockchain technology is a common property shared by many newly emerging cryptocurrency systems.[9] This system looks like Bitcoin with some differences like block size and coin width etc. The cryptocurrency market is similar to other exchange markets where cryptocurrencies are traded with multiple trading platforms. However, the digital currency market is distinguished by the fact that it is not regulated by a government or a specific party, and trading in it is all the time and all over the world, which the nature of the encrypted currency allows, which results in a more volatile market due to the high and low prices Cryptocurrency permanently.
Bitcoin Wallets
A Bitcoin wallet is a software wallet (or file) that stores private and public key pairs in order to manage your Bitcoins. Wallets monitor Bitcoin addresses on the Blockchain and update their balance with each transaction. Bitcoin wallets can be classified according to key generation into three types [7] [10]:
- Non-deterministic or Type-0 wallets: These are the simpler wallets because when a new pair of keys is requested, the wallet generates a random private key. Then, the wallet derives its corresponding public key. The generated key pair is completely random and is not associated with the previously generated keys. However, these wallets require sophisticated management and can fail to perform well because the number of keys stored exceeds the storage capacity of the wallet. Consistent backup of the generated keys is also essential to ensure that users can still access BTC when the wallet is not available. However, backups are vulnerable to theft and can lead to all keys belonging to the wallet being exposed.
- Deterministic wallets or Type-1 wallets: In this type of wallet, each key pair is generated from a single point called a seed. The keys are generated either sequentially or hierarchically. New public and private keys are computed from the previously generated keys using a one-way hash function with some additional data. In contrast to nondeterministic wallets, deterministic wallets need only to keep a backup of s to regenerate all of the previously derived keys.
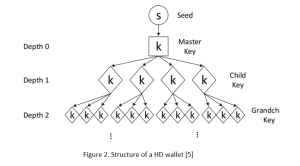
- Hierarchical deterministic (HD) wallets, or Type-2 wallets: HD wallet enables the creation of several child public keys without accessing the parent's private keys. HD Wallet is based on Bitcoin BIP32 protocol to create child keys in the tree structure as shown in Fig. 2.[7] BIP32 protocol uses Elliptic Curve Digital Signature Algorithm (ECDSA) key generation to convert the given random value or private key into graph points or public key.
The key generation begins at depth 0, which derives the root node (master) key components using a randomly chosen seed (s). In many wallets, seed is in the form of a mnemonic word sequence as described in the BIP0039 standard.[11] A mnemonic word sequence is a sequence of English words that represents a random number used to derive s. If your wallet gets destroyed or stolen, you can enter this seed in order to reconstruct the private key.
Bitcoin wallets can also exist in different forms based on different installation and infrastructure, there are two forms[12]:
- Hot wallets: this refers to a Bitcoin wallet which is connected to internet, it can be:
- Web wallet (online): In this type, you deposit money into market wallets and other online Bitcoin services wallets in order to run your business. These web wallets are the least secure option for storing bitcoins since you do not have any access to your private keys. You are basically asking someone else to hold your coins for you.
- Desktop wallet (software): These types of hot wallets store your private key on your computer. Thus, your bitcoins are safe as long as your computer is protected and free from malware, which is quite difficult to achieve perfectly, and this makes internet-connected desktop wallets a valuable target for hackers.
- Mobile wallet: These are wallets that store your private key on your mobile phone. They are practical and convenient, but they are the worst in terms of security and privacy, as mobile phones are vulnerable to theft or breakage.
- Cold wallets: In contrast to hot wallets, these wallets are not connected to the internet. They can be:
- Hardware wallet: They are physical devices which safely store your private key so that it cannot be hacked even if your device is compromised by malware. These wallets are safe and easy to use, but you need to always keep them connected to your computer to manage your coins.
- Paper wallet: They are just pieces of paper with a Blockchain address and its private key (or seed) in QR code format written on them, by scanning the QR code, funds can be send or received. By keeping your private key on a piece of paper, only someone who can physically access that data can steal your bitcoins, and because it is made of paper it can be easily damaged, so it is better to make multiple copies of it in order to recover your bitcoins in case you lose the original copy.
We can also categorize Bitcoin wallets into:[7]
- A full-service wallet is one that can perform all functions required to spend and receive BTC. These functions include:
- generating private keys needed to spend BTC,
- signing transactions with the private keys,
- deriving public keys needed to receive payments of BTC,
- broadcasting the derived public keys to the network,
- and monitoring how much has been the BTC spending and receiving of a wallet. Full-service wallets must be online connected to the Bitcoin network. The most popular desktop full-service wallets today are Armory, Electrum, and Bitcoin core. Airbitz wallet is an example for mobile wallets, for both iOS and Android. Other distributing-only wallets are capable of generating the public keys.
- The second type of wallets are signature wallets only: Its main purpose is to enhance wallet security by generating private keys in secure offline environments. This type of wallet can only interact with the Bitcoin network via the network wallet, and it generates pairs of private and public keys as needed to transfer the public key to the network wallet. Signing wallets can be offline wallets like hardware wallets.
- The final type of wallets are the distributing-only wallets: These wallets also strive to reduce the security issues caused by the full-service wallets. They are in the form of networked wallets for public key distribution in a prepopulated manner, where the public keys are derived and distributed as needed by the network, as in HD wallets.
Bitcoin Wallets and Security Risks
Security and privacy are inseparable properties and wallet security is considered for privacy. Each wallet type has its positive and negative sides, which makes it offer different levels of "security".[10]
The security level of the online wallet is low, and the hardware wallet is high compared to desktop and mobile wallets. The security level of a paper wallet is very high compared with other wallet types. Using the hardware wallet, the private key is secured with an integrated circuit and only the owner of the hardware alone can be able to generate the cryptographic signature. Using a paper wallet, the pair of the private and public key is printed on the paper for signing transactions. Armory, Bitcoin Core, Bitcoin Knots, Wasabi, and mSIGNA are privacy improved wallets.[10]
Another way to secure the funds is to store them in the sub wallets generated from super wallet seed. Losing a single sub wallet key may not result in the loss of the entire fund.[10] Other measures also can be taken in order to increase the security of storing keys in Bitcoin wallets. Practices, such as Multi-Sig transactions increase the security of the BTC stored in the wallet.[7]
Multi-signature or threshold signature is a process of combining more than one cryptographic key from a group of users into a single key.[7] Multi-signature helps to avoid a single point of failure. An attacker may not spend the fund by learning a single key alone from the group of users. Using this scheme user identity is masked with high security. Multi-signature schemes become inflexible to add or remove a user to and from the group.[7]
A major problem with current hardware wallets is the current backup and restore process , as almost all use a list of words (mnemonics) to restore the backed up private key if necessary. The passwords must be written on a piece of paper and kept safe. However, this method also poses a security risk as the slip of paper with the information can get stolen or lost. In the first case, if a hacker discovers the word list, he may be able to attempt the passphrase via brute force. Therefore, the user have to pick a long, difficult passphrase. In the second case, the user will be unable to retrieve the keys and forfeit all money if she selects a difficult-to-remember long passphrase [13]. It is very important to create secure passwords for any wallet you may choose and take regular backups of the seed phrases, private keys, and wallet data files.
Another problem useres of Bitcoin wallets face are risks of social engineering and phishing attacks, which exploit human psychology rather than technical vulnerabilities. These techniques trick people into disclousing sensitive information or granting access to their assests. The most common attacks are deceiptive mails, messages, or fake websites which aim to get access to all kind of different information, like target IP, username and password. Once an attacker has access to this data, they gain full control, allowing unauthorized access and trasactions. Phishing websites most commonly mimic legitamate services or websites, like PayPal for example, making them difficult to distinguish from the real provider [14].
After examining and studying different threats and risks, it becomes evident, that the human being is the most vulnerable in the cyber security chain because of the so called "Social Engineering" techniques. Therefore, educating users in terms of threats like phishing attempts, passwords, and storage options becomes decisive in defending against theses kinds of attacks. A well-informed user is more likely to recognize threats like phishing emails by identifying suspicious communication, taking preventive steps like haveing a strong password with two-factor authentication, and carefully decideing when choosing a wallet for storing digital assets [15].
Conclusion
Blockchain has many benefits and provides real levels of security and has many beneficial uses, one of these uses is cryptocurrency and thus Bitcoin wallets. This paper gave a general idea about Blockchain and Bitcoin, presented the types of Bitcoin wallets, their pros and cons, and the best ways to keep Bitcoin wallets safe and secure against hacker attacks. Bitcoin supersedes fiat currency in multiple dimensions because it can be transferred internationally without any limits, transactions have either no fees or a very low fee. Currently, it does not need any personal information, is transparent as every user has a copy of the public ledger, and secure as the underlying cryptographic algorithm provides security [3], yet, and although about 12 years have passed since the launch of the first digital currency, it still faces many limitations, especially in the field of cybersecurity, as it is open source and faces instability in its value, but it has undoubtedly become (albeit partially in some countries) one of the currencies that can be traded.
References
- ↑ 1.0 1.1 1.2 1.3 1.4 P. Ratanasopitkul, "Blockchain – Revolutionize Green Energy Management," 2018 International Conference and Utility Exhibition on Green Energy for Sustainable Development (ICUE), 2018, pp. 1-6, doi: 10.23919/ICUE-GESD.2018.8635666.
- ↑ Nakamoto, S., “Bitcoin: A Peer-to-Peer Electronic Cash System,” 2008. https://bitcoin.org/bitcoin.pdf
- ↑ 3.0 3.1 P. K. Kaushal, A. Bagga and R. Sobti, "Evolution of bitcoin and security risk in bitcoin wallets," 2017 International Conference on Computer, Communications and Electronics (Comptelix), 2017, pp. 172-177, doi: 10.1109/COMPTELIX.2017.8003959.
- ↑ 4.0 4.1 4.2 Buquan Liu. "Overview of the basic principles of blockchain". In 2021 Interna- tional Conference on Intelligent Computing, Automation and Applications (ICAA), pages 588–593, 202
- ↑ 5.0 5.1 5.2 5.3 5.4 5.5 Yaga, D., Mell, P., Roby, N., & Scarfone, K. (2018). Blockchain technology overview. arXiv: Cryptography and Security
- ↑ Shawn Tracy Robinson & David John Robinson & Christopher Dryja, Bitcoin Crypto What's in Your Wallet? ,2021, Pages 18-20
- ↑ 7.0 7.1 7.2 7.3 7.4 7.5 7.6 7.7 7.8 7.9 E. Zaghloul, T. Li, M. W. Mutka and J. Ren, "Bitcoin and Blockchain: Security and Privacy," in IEEE Internet of Things Journal, vol. 7, no. 10, pp. 10288-10313, Oct. 2020, doi: 10.1109/JIOT.2020.3004273.
- ↑ Raj Roshan. "History of blockchain" . https://intellipaat.com/blog/ tutorial/blockchain-tutorial/history-of-blockchain/, 2022
- ↑ G. Hileman and M. Rauchs, Global Cryptocurrency Benchmarking Study, Cambridge Centre Alternative Finance, Cambridge, U.K., 2017.
- ↑ 10.0 10.1 10.2 10.3 S. Banupriya and K. Kottilingam, "An Analysis of Privacy Issues and Solutions in Public Blockchain (Bitcoin)," 2021 2nd International Conference for Emerging Technology (INCET), 2021, pp. 1-7, doi: 10.1109/INCET51464.2021.9456350.
- ↑ M. Palatinus, P. Rusnak, A. Voisine, and S. Bowe. (2013). Mnemonic Code for Generating Deterministic Keys. [Online]. Available: https:// github.com/bitcoin/bips/wiki/Comments:BIP-0039
- ↑ Sabine Houy, Philipp Schmid, and Alexandre Bartel. 2023. Security Aspects of Cryptocurrency Wallets—A Systematic Literature Review. ACM Comput. Surv. 56, 1, Article 4 (January 2024), 31 pages. https://doi.org/10.1145/3596906.
- ↑ Hossein Rezaeighaleh and Cliff C. Zou. "New secure approach to backup cryptocurrency wallets". In 2019 IEEE Global Communications Conference (GLOBECOM), pages 1–6, 2019
- ↑ A. A. Andryukhin, "Phishing Attacks and Preventions in Blockchain Based Projects," 2019 International Conference on Engineering Technologies and Computer Science (EnT), Moscow, Russia, 2019, pp. 15-19, doi: 10.1109/EnT.2019.00008.
- ↑ Ivanov, M.A. et al. (2021) ‘Phishing Attacks and Protection Against Them’. Available at: https://doi.org/10.1109/elconrus51938.2021.9396693