Difference between revisions of "Hak5 Bash Bunny"
| Line 54: | Line 54: | ||
! COMMAND !! Description !! Example | ! COMMAND !! Description !! Example | ||
|- | |- | ||
| ATTACKMODE || Specifies the USB device or combination of devices to emulate. || ATTACKMODE RNDIS_ETHERNET | | ATTACKMODE || Specifies the USB device or combination of devices to emulate. || <code>ATTACKMODE RNDIS_ETHERNET</code> | ||
|- | |- | ||
| DUCKY_LANG || Set the HID Keyboard language || DUCKY_LANG US | | DUCKY_LANG || Set the HID Keyboard language || <code>DUCKY_LANG US</code> | ||
|- | |- | ||
| LED || Control the RGB LED. Accepts color and pattern or payload state. || SETUP | | LED || Control the RGB LED. Accepts color and pattern or payload state. || <code>SETUP</code> | ||
|- | |- | ||
| QUACK || Injects keystrokes (ducky script) or specified ducky script file. || QUACK STRING Hello World | | QUACK || Injects keystrokes (ducky script) or specified ducky script file. || <code>QUACK STRING Hello World</code> | ||
|- | |- | ||
| Q || Alias for QUACK || Q STRING Hello World | | Q || Alias for QUACK || <code>Q STRING Hello World</code> | ||
|- | |- | ||
|} | |} | ||
Revision as of 19:47, 21 October 2020
Summary
This documentation is about the Bash Bunny from Hak5. This device is an multi-purpose USB Attack platform that combines a Rubberducky and a Debian based micro computer to perform a wide range of attacks.
General Information and File System
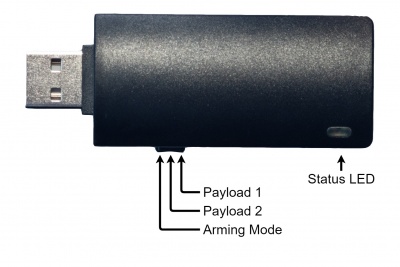
Switch Positions
The Bash bunny has 3 Switch positions to switch between Arming mode and the two Attacks Payloads. The most left position sets the Bashbunny in arming mode, as shown in the figure. If the device is in this mode, its filesystem will be accessible and the user can edit the Payloads as well as the config.txt.
File System
The filesystem is as shown below. Where config.txt is used to set the global configuration for all payloads like the language with the DUCKY_LANG EN. The payload.txt files contain the executed ducky script and bunny script commands for their corresponding switch position.
Bashbunny |- docs | |- EULA, License, this readme.txt | |- License | |- readme.txt | |- languages | |- HID languages that are placed here will installed at boot in arming mode. | |- loot | |- Where the stolen date can be saved. | |- payloads | |- extensions | | |- Additional Bunny Script commands/functions. | | | |- library | | |- Payloads backups. | | | |- switch1 | | |- payload.txt | | | |- switch2 | | |- payload.txt | | | |- arming | |- payload.txt | | -config.txt Global config script Sourced by all payloads
Bunny Script
Bunny Script is an simple easy to learn programming language with a small set of commands
| COMMAND | Description | Example |
|---|---|---|
| ATTACKMODE | Specifies the USB device or combination of devices to emulate. | ATTACKMODE RNDIS_ETHERNET
|
| DUCKY_LANG | Set the HID Keyboard language | DUCKY_LANG US
|
| LED | Control the RGB LED. Accepts color and pattern or payload state. | SETUP
|
| QUACK | Injects keystrokes (ducky script) or specified ducky script file. | QUACK STRING Hello World
|
| Q | Alias for QUACK | Q STRING Hello World
|
Attack modes
The Bash Bunny can be used as many attack modes simultaneously, like an USB Rubber Ducky, LAN adapter, or storage device.
| Attackmodes | VID / PID (Vendor ID/Product ID) |
|---|---|
| SERIAL | 0xF000 / 0xFF11 |
| ECM_ETHERNET | 0xF000 / 0xFF13 |
| RNDIS_ETHERNET | 0xF000 / 0xFF12 |
| AUTO_ETHERNET | |
| STORAGE | 0xF000 / 0xFF10 |
| HID | 0xF000 / 0xFF01 |
SERIAL
Opens an serial console interface. This interface can be used to access the Bash Bunny and configure it or to perform an attack with it.
ECM ETHERNET
Ethernet Control Model (ECM) is an driver model for USB Ethernet adapter that work on Linux, Android and MAC
RNDIS ETHERNET
Remote Network Driver Interface Specification (RNDIS) is the proprietary counterpart devolved by Microsoft and work only on Windows 7 and newer machines.
AUTO ETHERNET
This Ethernet attack modes combines both by first trying to deploy an ECM Ethernet and if it is not successful changing to RNDIS.
STORAGE
The Storage attack mode let the Bash Bunny act as an USB Mass Storage (UMS). This method is manly used to transfer data to the victim device, like an image for an background change prank.
HID
Human Interface Device (HID) lets the Bash Bunny act as an self typing Keyboard also called USB Rubber Ducky.
Combinable Attack Modes
The Bash Bunny allows us to combine some of the attack modes, which combinations are valid is shown in the table below. The attack modes and their combinations can be changed multiple times during the attack with the bunny script.
| Attackmodes | VID / PID (Vendor ID/Product ID) |
|---|---|
| SERIAL STORAGE | 0xF000 / 0xFFF0 |
| HID SERIAL | 0xF000 / 0xFF14 |
| HID STORAGE | 0xF000 / 0xFF02 |
| HID RNDIS_ETHERNET | 0xF000 / 0xFF03 |
| HID ECM_ETHERNET | 0xF000 / 0xFF04 |
| HID STORAGE RNDIS_ETHERNET | 0xF000 / 0xFF05 |
| HID STORAGE ECM_ETHERNET | 0xF000 / 0xFF06 |
| SERIAL RNDIS_ETHERNET | 0xF000 / 0xFF07 |
| SERIAL ECM_ETHERNET | 0xF000 / 0xFF08 |
| STORAGE RNDIS_ETHERNET | 0xF000 / 0xFF20 |
| STORAGE ECM_ETHERNET | 0xF000 / 0xFF21 |
Gain Access to the Bash Bunny
There are three main ways to gain access to the Bash Bunny:
- from the File System
- with an Serial Console Interface
- with SSH
| hostname | root |
|---|---|
| password | hak5bunny |
Serial Console Interface
The Serial Console Interface can be used when the Bash Bunny is in attack mode. It is independent from the operating system but the ways are different.
Windows (Putty)
Putty is the best way t access serial consoles when working on an Windows machine. Just download it on the manufacturer website and install it and follow the steps.
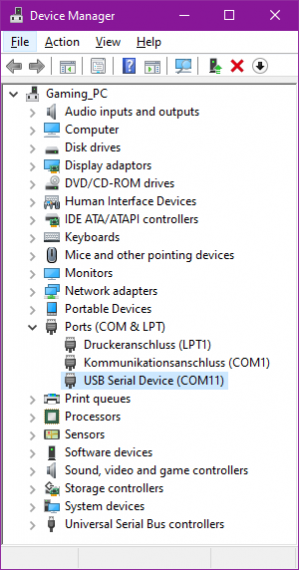
Step 1:
Get the comport by entering
[Windows key] device manager [enter]
Extend the "Ports (COM & LPT) line and search for the "USB Serial Device(COM..)"
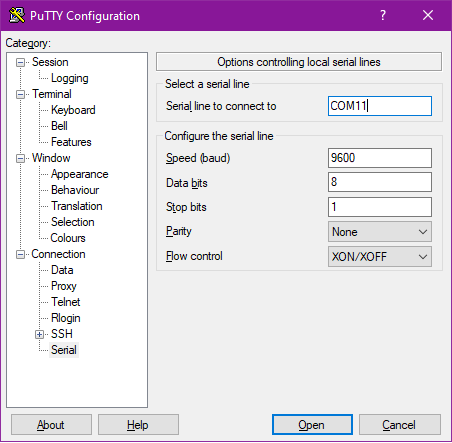
Step 2:
Open Putty and go to the Serial TAB and enter the following parameters:
| Serial line to connect to | COM.. |
|---|---|
| Speed (baud) | 115200 |
| Data bits | 8 |
| Stop bits | 1 |
| Parity | No |
| Flow control | XON/XOFF |
Go back to the session tab and check "Serial" and Open the Connection
Linux
1. When using Linux it is preffered to use the package screen install it with
sudo apt-get install screen
2. Search for the device with
dmesg | grep tty Output: [195.328289] cdc_acm 1-1.1.2.3:2.0: ttyACM0: USB ACM device
3. Connect with the command
sudo screen /dev/ttyAMC0 115200
SSH
Set the bash bunny in attack mode (Switch at the nearest position to the USB connector) and plug it in. Enter the device and follow the path BashBunny/payloads/switch1 (switch 2 can be used as well)and edit the payload.txt file Windows Change the third line to
ATTACKMODE STORAGE RNDIS_ETHERNET
MAC and Linux Change the third line to
ATTACKMODE STORAGE ECM_ETHERNET
The RNDIS_ETHERNET and ECM_ETHERNET are used to display the Bash Bunny as an USB Ethernet adapter. Windows uses for this adapters proprietary drivers so it is not compatible with the Ethernet Control Model (ECM).
Connect whit:
ssh root@172.16.64.1
Connect the Bash Bunny with your internet.
The deployed internet connection is for the preparation phase only. During the attack phase the Bash Bunny is able to deploy its own little network, which does not have an gateway to the internet. But the LAN can be used to connect the victim to an Server Message Block NAS server that runs on the Bash Bunny to copy data to the victim machine. The internet connection is mainly used for downloading Debian software repository.
Linux Hak5 published a shell script that guides you threw the process. It needs root privileges but only performs two iptables NAT entries. Due to the habits of the iptbales service all entries get deleted during an machine restart, if the are not saved with the iptables-persistent service. But the entered data gets saved in the script it self and connection can be rebuilt with one command.
wget bashbunny.com/bb.sh pi@raspberrypi:~ $ sudo chmod +x ./bb.sh pi@raspberrypi:~ $ ./bb.sh
This Bash Bunny Connection script requires root.
_____ _____ _____ _____ _____ _____ _____ _____ __ __
(\___/) | __ || _ || __|| | | | __ || | || | || | || | |
(='.'=) | __ -|| ||__ || | | __ -|| | || | | || | | ||_ _|
(")_(") |_____||__|__||_____||__|__| |_____||_____||_|___||_|___| |_|
Bash Bunny by Hak5 USB Attack/Automation Platform
v1
Saved Settings: Share Internet connection from eth0
to Bash Bunny at eth1 through default gateway 192.168.1.1
[C]onnect using saved settings
[G]uided setup (recommended)
[M]anual setup
[A]dvanced IP settings
[Q]uit
Make Sure that you unplug the Bash Bunny and press G to start the 3 step guided setup. Reconnect the Bash Bunny when step 3 demands it.
Bash Bunny detected. Please disconnect the Bash Bunny from this computer and press any key to continue with guided setup. Step 1 of 3: Select Default Gateway Default gateway reported as 192.168.1.1 Use the above reported default gateway? [Y/n]? Y Step 2 of 3: Select Internet Interface Internet interface reported as eth0 Use the above reported Internet interface? [Y/n]? Y Step 3 of 3: Select Bash Bunny Interface Please connect the Bash Bunny to this computer. ................[Checking] Detected Bash Bunny on interface eth1 Use the above detected Bash Bunny interface? [Y/n]? Y Settings saved. Saved Settings: Share Internet connection from eth0 to Bash Bunny at eth1 through default gateway 192.168.1.1 [C]onnect using saved settings [G]uided setup (recommended) [M]anual setup [A]dvanced IP settings [Q]uit
Enter C to connect the Bash Bunny to the Internet
Detecting Bash Bunny.........found.
_ . ___ (\___/)
( _ )_ <--> [___] <--> (='.'=)
(_ _(_ ,) \___\ (")_(")
Access the Bash Bunny with SSH and validate if the Bash Bunny hast access to the world wide web.
ssh root@172.16.64.1
root@172.16.64.1's password:
_____ _____ _____ _____ _____ _____ _____ _____ __ __
(\___/) | __ || _ || __|| | | | __ || | || | || | || | |
(='.'=) | __ -|| ||__ || | | __ -|| | || | | || | | ||_ _|
(")_(") |_____||__|__||_____||__|__| |_____||_____||_|___||_|___| |_|
Bash Bunny by Hak5 USB Attack/Automation Platform
Last login: Fri Jun 5 01:16:09 2020 from 172.16.64.64
root@bunny:~# ping 8.8.8.8
PING 8.8.8.8 (8.8.8.8) 56(84) bytes of data.
64 bytes from 8.8.8.8: icmp_seq=1 ttl=55 time=17.7 ms
64 bytes from 8.8.8.8: icmp_seq=2 ttl=55 time=17.7 ms
64 bytes from 8.8.8.8: icmp_seq=3 ttl=55 time=17.7 ms
64 bytes from 8.8.8.8: icmp_seq=4 ttl=55 time=18.6 ms
^C
--- 8.8.8.8 ping statistics ---
4 packets transmitted, 4 received, 0% packet loss, time 3003ms
rtt min/avg/max/mdev = 17.701/17.990/18.694/0.439 ms
Bunny Script
Todo Example Script
# Defines and creates the loot directory and filename
LOOTDIR='/root/udisk/loot/osscan'
mkdir -p $LOOTDIR
FILENAME="${LOOTDIR}/os.log"
# Setup Phase:
# Set Atackmode to Microsoft network adapter
LED SETUP
ATTACKMODE RNDIS_ETHERNET
# SGrab the targets ipaddress
GET TARGET_IP
# Logs the IP address and timestamps
echo Timestamp: `date +"%Y-%m-%d-%T"` > $FILENAME
echo Target IP: ${TARGET_IP} >> $FILENAME
echo "Starting Nmap Scan: " >> $FILENAME
# Attack Phase:
# Bash Bunny Performs an nmapt with OS guessing
LED STAGE1
nmap -O -- fuzzy $TARGET_IP >> $FILENAME
echo Timestamp: `date +"%Y-%m-%d-%T"` >> $FILENAME
LED FINISH
Used Hardware
References
Category:Pentesting