Difference between revisions of "Hak5 LAN Turtle"
| Line 76: | Line 76: | ||
# Open AutoSSH and insert the following parameters: | # Open AutoSSH and insert the following parameters: | ||
#* <code>user@host</code> user and host to establish the SSH tunnel | #* <code>user@host</code> user and host to establish the SSH tunnel | ||
#* <code>remote port</code> remote port to bind through the SSH tunnel | #* <code>remote port</code> remote port to bind through the SSH tunnel (default 2222) | ||
#* <code>local port</code> local port to bind tunnel (default 22) | #* <code>local port</code> local port to bind tunnel (default 22) | ||
# Submit the changes and start AutoSSH (or enable it for autostart) | # Submit the changes and start AutoSSH (or enable it for autostart) | ||
Revision as of 18:02, 23 November 2020
Summary
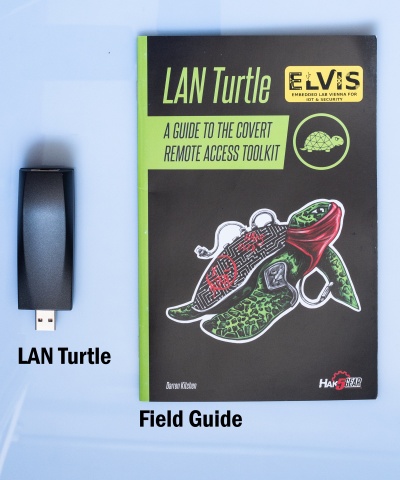
The Lan turtle is an tool for Penetration testers and Systems Admins disguised as an simple USB Ethernet adapter.
Description
Setting up the LAN Turtle
- Plug the LAN turtle into one of the USB-ports of your computer.
- Your computer will get an 172.16.84.x address as soon as the startup sequence of the turtle finished. If not, than statically configure an IP out of the 172.16.84.0/24 range.
- Connect to it with
ssh root@172.16.84.1and enter the passwordsh3lls - The simplistic graphical shell interface will prompt you to change the password but the old one is also allowed.
- Then the LAN turtle can be configured and modules can be installed in the interface.
- If you end the interface you will be greeted with an normal Linux shell but you can open it again with the
turtlecommand
Using the Turtle modules
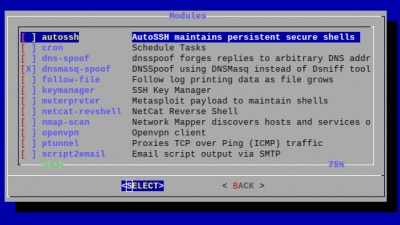
The LAN Turtle comes packed with pre-installed tool. Furthermore it is possible to program your own or download them from the internet and configure them with the module manager as well.
AutoSSH
AutoSSH is a service which provides persistent SSH connections. If an SSH session drops, it will be quickly re-establish by AutoSSH. This service is typically used to provide a convenient and persistent reverse shell into the LAN Turtle on the standard SSH port 22 - though it may be configured with any standard SSH parameters to forward any arbitrary port.
host- The username and hostname (DNS or IP) separated by @ for which to establish the SSH connection.port- The port number from which the remote server will bind.listen port- The port number to which the remote port will bind.
Example: Per the defaults, the public server will bind its local port 2222 back to the LAN Turtle port 22. In this scenario one may establish a persistent connection to their LAN Turtle from this reverse shell by first connecting to the public server, and then from there establishing an SSH connection to port 2222.
Cron
Cron is a job scheduler which can be used to start and stop modules at specific times or regular intervals using the 'start' and 'stop' commands.
DNSSpoof
DNSSpoof forges replies to arbitrary DNS address / pointer queries on the LAN. This is useful in bypassing hostname-based access controls, or in implementing a variety of man-in-the-middle attacks. For example, the IP address returned for a client lookup of the domain \"example.com\" can be replaced with that of the LAN Turtle itself, or a 3rd party server. In this scenario, the computer connected to the Internet through the LAN Turtle attempting to browse to this domain may be redirected to the spoofed IP.
Keymanager
With this tool you can create RSA keypairs and copy them to the public server. This is needed when AutoSSH is configured.
Meterpreter
This module deploys an persistent shell to the Metasploit Framework of an other Machine.
namp-scan
This module uses nmap for discovering running devices and their port of the current LAN network.
OpenVPN
OpenVPN enables remote access the LAN Turtle and optionally the network on which it resides. It allows to send the captured data to your operating network.
SSHFS
SSHFS (Secure SHell FileSystem) is a file system for Linux (and other operating systems with a FUSE implementation, such as Mac OS X or FreeBSD) capable of operating on files on a remote computer using just a secure shell login on the remote computer. On the local computer where the SSHFS is mounted, the implementation makes use of the FUSE (Filesystem in Userspace) kernel module. The practical effect of this is that the end user can seamlessly interact with remote files being securely served over SSH just as if they were local files on his/her computer. On the remote computer the SFTP subsystem of SSH is used.
URLSnarf
URLSnarf allows you to capture which websites were accessed by the plugged in computer. URL Snarf only works with http webpages which are hard to find today.
Use Cases
The LAN turtle can be deployed in various use cases, which can be divided into three categories:
- Remote-Access attacks with AutoSSH or OpenVPN
- Man-in-the-Middle attacks with URLSnarf or DNSSpoof
- Information Gathering with nmap
The following step-by-step instructions will outline how to configure the LAN turtle in order to perform these attacks.
Remote-Access attacks with AutoSSH
In this example consider an internal network which is secured by a firewall and a public server in the internet controlled by the attacker.
Step 1: Generate RSA keypairs with Keymanager
- Open the Keymanager module and select
generate_key - Select
copy_keyand inserthostremote SSH serverportremote SSH server port (typically 22)useruser on the remote SSH serverpasswordpassword for the user on the remote host
Step 2: Configure AutoSSH
- Open AutoSSH and insert the following parameters:
user@hostuser and host to establish the SSH tunnelremote portremote port to bind through the SSH tunnel (default 2222)local portlocal port to bind tunnel (default 22)
- Submit the changes and start AutoSSH (or enable it for autostart)
Step 2: Access LAN turtle from remote server
- Connect to the remote server
- Connect locally to the remote port of the AutoSSH configuration by
ssh root@localhost:2222
Man-in-the-Middle attacks with URLSnarf
Information Gathering with nmap
As an example project we use the following modules:
cronto periodically start the attacksshfsto save the caputred information in a file on the remote servernmap-scanto sniff the configuration and devices of the network
Step 1: Configure sshfs
- Access the sshfs module via the module manager
- Go to the configure tab and insert
- Host: IP address of the remote server
- Port:
22 - User: the username
- Path: This can be left blank if you want to use the users home directory
- Start ssfs and enable it for start up
Step 2: nmap-scan
- Access the nmap-scan module via the module manager
- Go to the configure tab and insert
- target:
192.168.0.1-255(This may differ for our network) - logflie:
/sshfs/ - use the desired attack profile
- save the configuration with execute
- target:
Step 3: cron job
- add in the con config
*/15 * * * * start nmap-scan
This line start an nmap-scan every 15 minutes.