Difference between revisions of "Hak5 Signal Owl"
| Line 161: | Line 161: | ||
Settings | Settings | ||
NMAP_OPTIONS="-sP" | NMAP_OPTIONS="-sP" | ||
LOOT_DIR=/root/loot/open_ap_nmap_scan | LOOT_DIR=/root/loot/open_ap_nmap_scan | ||
MAX_CIDR=20 | MAX_CIDR=20 | ||
DEBUG=1 | DEBUG=1 | ||
Revision as of 17:53, 21 December 2021
Summary
The Signal Owl is a hardware product developed by the company Hak5. It is a simple payload-based signals intelligence platform with a unique design for discreet planting or mobile operations on any engagement. The most popular application cases include classic network mapping and basic penetration tests for various wireless technologies.
Description
The Signal Owl is designed to be rapidly deployed in all kinds of environments, allowing it to be an entry point for network analysis and basic wireless attacks in a variety of locations. With a power consumption of 100-200 mAh and the thermally optimized architecture, mobile operations as well as long term deployments, are enabled.
Components
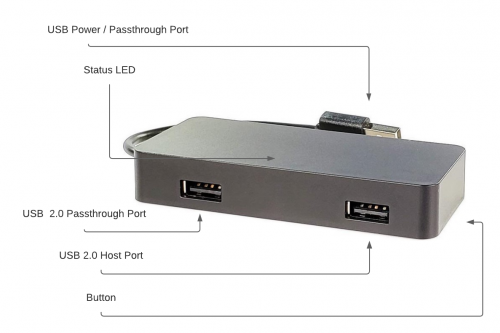
This device features several components of which some may not be visible to the human eye at first sight.
USB Power / Passthrough Plug
The USB power or passthrough plug is used to power the device. It can be powered from any reliable USB source.
USB 2.0 Passthrough Port
The USB 2.0 passthrough port is the port closest to the pigtail. Data and power pass through to that port, allowing for implant operations. With devices like keyboards plugged plugged inline between this passthrough port and the power plug connected to the target computer, the Signal Owl will remain undetected from the operating system. Only the keyboard will be visible.
USB 2.0 Host Port
The USB 2.0 host port is the port farthest away from the pigtail. It is connected to the Linux socket of the Signal Owl and supports USB flash drives formatted with FAT32 and EXT4 file systems as well as many Wi-Fi, Bluetooth and other RF transceivers.
Button
The button on the bottom of the device is used to enter Arming Mode and to interact with payloads. It is not pressable without special tools like paperclips.
Status LED
The status LED indicates the current status of the Signal Owl. When turned off, it is not visible.
Implant / mobile operations
Implant operations
During long term wireless engagements, the Signal Owl may be planted inline between any typical 5V USB power source. This may be useful in situations where ports are occupied, or to deter the unit from being unplugged.
Mobile operations
The Signal Owl features a low power consumption profile, with a typical power draw averaging 100-200 mAh. Additionally, it is thermally optimized for long term deployments in many indoor environments. One can expect a large 20,000 mAh USB battery bank to operate the unit for up to 4 days.
Default Settings
Default settings that are used in order to access the device via SSH are pictured in the table below.
| Default Settings | |
|---|---|
| Username | root |
| Password | hak5owl |
| SSID | Owl_xxxx |
| IP Address | 172.16.56.1 |
| SSH command | ssh root@172.16.56.1 |
The SSID during Arming Mode is Owl_xxxx in which xxxx indicates the last two octets of the devices MAC address.
LED Status Indications
The Signal Owl features a red LED with the following default status indications:
| LED | Status |
|---|---|
| Blinking | Booting |
| Solid | Mounting external storage / Running upgrade |
| Single blinking | Attack Mode |
| Double blinking | Arming Mode |
| Slow blinking | Error running payload |
Modes of Operation
The Signal Owl comes with two modes of operation, Attack Mode and Arming Mode. By default, the device will boot into Attack Mode. In order to access Arming Mode, the button on the bottom of the device has to be pressed while in Attack Mode. It is not recommended to press the button during the boot sequence as this can possibly brick the device and render it useless. The arming mode is used for firmware updates and shell access, while the attack mode is used to load and execute the payload.
Attack Mode
Attack Mode is the default mode, the Signal Owl boots into. It provides two basic functions, being the payload loading function and the payload execution function. The payload loading function checks for any USB flash drives plugged into the host port of the device and copies payloads and extensions to the root of the Signal Owl. The payload execution function is responsible for executing the payload that is currently stored on the root of the Signal Owl. In case no payload is found, the device will blink slowly, indicating the FAIL status.
Arming Mode
The Arming Mode provides two basic functions, being the firmware update function and the shell access function. The firmware update function checks for any USB flash drives plugged into the host port of the device and copies firmware upgrade files into the internal storage of the device and flashes it. The shell access function starts an open access point with the SSID Owl_xxxx in which xxxx indicates the last two octets of the devices MAC address. Additionally, a SSH server providing access to the shell of the Signal Owl is enabled.
Initial Setup
When first unboxing the Signal Owl, the device runs a stager firmware that is designed to flash the latest firmware from a USB flash drive. In order to update the Signal Owl, the latest firmware has to be downloaded. Then, the downloaded file must be copied to the root of an EXT4 or FAT32 formatted USB flash drive. It is important not to modify this file. The next step is to plug the USB flash drive into the powered off Signal Owl. Afterwards, the device has to be powered on by a reliable USB source. The upgrade itself takes approximately five to ten minutes and is indicated by a solid red LED light. When finished, the device will reboot, enter Attack Mode and blink slowly, indicating an error running the payload because no payload has been found.
Payload Development
Payloads for the Signal Owl are written in bash with Ducky Script and can be created with any standard text editor. All payloads should begin with an interpreter directive, like the shebang #!/bin/bash for bash payloads and payloads must be named either payload.txt or payload.sh. In order to create effective payloads, the Signal Owl comes with several preinstalled penetration testing tools. These are as follows: Nmap, Aircrack-ng, MDK4 and Kismet.
Tools
• Kismet - detector for wireless networks and devices.
• MDK4 - Wi-Fi testing tool.
• Aircrack-ng Suite - a complete suite of tools for WiFi network security assessment.
• Nmap - open source utility for network discovery and security auditing.
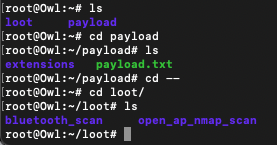
Adding Payloads and Extensions
Payloads can be stored on the internal storage of the Signal Owl as well as on a USB flash drive. When booting, payloads on USB flash drives are given priority and will override payloads stored on the Signal Owl. If no payload is found on the external storage and a payload is present on the internal storage, the internally stored payload will be executed. In case no payload is found on both internal and external storage, the Signal Owl will blink slowly. To successfully copy a payload to the Signal Owl and execute it, the payload must be named payload.txt or payload.sh and it has to be placed in the root directory of the flash drive. Similarly, payload extensions should be stored in a /extensions directory on the flash drive.
After plugging the Signal Owl into a USB source, it will boot and then copy the payloads and payload extensions to the /root/payload and /root/payload/extensions directory respectively. Then, the device will enter Attack Mode and execute the payload.
Fake Beacon Flooding Attack
The fake beacon flooding attack is one possible use case for the Signal Owl. With that attack, fake beacon frames are broadcasted to nearby devices. Beacon Frames include various parameters like the SSID, the type of encryption used and timestamps. This results in the creation of multiple fake Wi-Fi networks. Devices with Wi-Fi browsers are then flooded with these fake networks, causing potential network scanner and driver crashes. Furthermore, the attack may prevent legitimate users from finding their networks and lead to denial of service. To execute the attack with the Signal Owl, the preinstalled tools Aircrack-ng and MDK4 are used. The following bash script is saved as payload.sh and placed on the root of an USB flash drive. Then the USB flash drive is plugged into the Signal Owl. After powering on the device, multiple fake networks with random SSIDs are generated and broadcasted to all nearby devices.
#!/bin/bash LED SETUP #creates monitor mode interface on wirelss card of the Signal Owl airmon-ng start wlan0 LED ATTACK #floods nearby devices with random SSIDs mdk4 wlan0mon b -w a -m -s 1000
The results as seen from a victim running a Windows 10 system are pictured in the figure below.
Open AP Nmap Scanner
Description: First access points are scanned, then a connection is established to the open access points, after connecting, the nmap scan runs and analyses the AP, the results are saved in the loot folder.
Settings NMAP_OPTIONS="-sP" LOOT_DIR=/root/loot/open_ap_nmap_scan MAX_CIDR=20 DEBUG=1
Step-by-step guide
1) download the payload payload 2) store the payload in a usb stick and plug the stick into the signal owl 3) after connecting the signal owl, the payload is loaded on the root folder and the scan starts. 4) once successfully executed, you can start the signal owl in arming mode and see the results in the loot folder. example loot Directory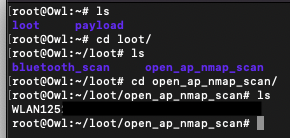
Arming Mode connection
Step-by-step guide for accessing the arming mode
1) click on the button located on the bottom of the signal owl while it is in attack mode. After pressing the button, the signal owl enters the arming
mode and provides an open access point with the name Owl xxxx (where xxxx stands for the last two digits of the MAC address of the device).
2) Connect to the access point.
 3) Now you can connect via ssh by using the username and password (default: Username: root, Password: hak5owl, IP Address: 172.16.56.1)
4) after successful connection you will end up in root@Owl directory
3) Now you can connect via ssh by using the username and password (default: Username: root, Password: hak5owl, IP Address: 172.16.56.1)
4) after successful connection you will end up in root@Owl directory
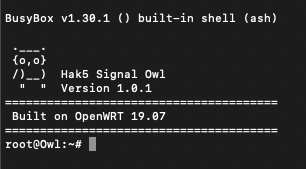 5) Now you can enter the directories loot and payload to either view the results or to make further settings
5) Now you can enter the directories loot and payload to either view the results or to make further settings
example Directory structure
Use Cases
The Signal Owl has a variety of different use cases. Among the most popular ones are classical network mapping and wardriving as well as basic penetration tests for different wireless technologies.