Introduction to APK Reversing techniques
Summary
This page describes various methods that can be used to reverse engineer mobile phone applications. An Android Package Kit (APK) is the package file format used by the Android operating system for distribution and installation of mobile apps.
Background
The main difference of IoT devices to arbitrary devices is that they offer network connectivity to allow mobile apps to read from sensors or control actuators. These apps can be used for monitoring e.g. smart fitness devices or the remote control of these devices e.g. smart lightbulp. In the OWASP IoT Top 10 security vulnerabilities mobile interfaces are included in the Insecure Ecosystem Interfaces at the third rank. Therefore a security assessment of the android app is part of the security analysis of an IoT device.
Android System
Android is based on a security hardened Linux which supports various security features such as Address Space Layout Randomization (ASLR), Canaries, non executable stack (NX memory areas) and allows only position-independent executable code. Further all system calls are firewalled and each application runs isolated for one user, the apps are usually sandboxed. Android provides a permission system for the access of resources such as contacts or camera.
Android Runtime (ART)
The Android runtime is the managed runtime used by applications and some system services on Android.The ART predecessor Dalvik VM was using a just-in-time (JIT) compiler at runtime whereas ART primarily generates a native executable in ELF format during the installation. This is also called ahead-of-time (AOT) compilation, furthermore ART includes a JIT compiler for performance reasons and update processes [1]. Both Dalvik VM and ART use the Dalvik Executable format[2] and Dex bytecode specification[3]. Android recommends writing your apps in Java code with Android SDK instead of using the native code interface Android NDK.
Android Package Format APK
An Android Package Kit (APK) is the package file format used by the Android operating system for distribution and installation of mobile apps.
The requisition of an APK is usually done via a play store or web download or directly from the phone using the Adroid Debug Bridge over a USB cable.
Installation of the Adroid Debug Bridge (adb)
The adb is a command line tool which enables the interaction over USB with a mobile phone. The main usage of adb is to install APKs and debug apps, it additionally allows command line access on the device [4].
1. Unlock Developer Options
The developer options on Android devices are usually hidden and need to be unlocked by finding the Android Build number. Where the Android Build number is located is dependent on the device, a search path similar to (Settings > About phone > Software information > Build number) can be used. For the activation of the developer options the Build number needs to be tapped seven times. After the first few taps a message appears telling that "You are now X steps away from being a developer", where X is the number of taps missing. After you succeeded the 7th tap the developer options will appear in the settings menu.
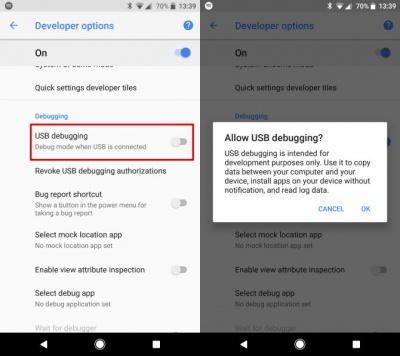
2. Enable USB Debugging
Then USB Debugging located in the Developer Options needs to be enabled.
3. Install the Debug Bridge
Install adb on the computer connected to the phone via USB cable and start the adb server
apt install adb adb start-server
Usage of adb
- Installation/Uninstallation of.apk files via USB
adb install <apk_filename>
- Retrieve/transfer of files and databases
adb pull/push <filename>
- Get active logs
adb logcat
- List applications installed on the phone
adb shell pm list packages
- Discover the path to the .apk file
adb shell pm path com.myapplication
Then use the pull command to retieve the APK file from the phone.
APK Content
Unzipped APK Content
An APK file is a packed and compressed file, essentially a ZIP file containing the compiled code, the resources, signatures, manifest and every other file the software needs in order to run. The content of an APK can be extracted via command line on the computer:
unzip <apk_filename>
The extracted content of an APK is shown in the table below.
| AndroidManifest.xml | the manifest file in binary XML format |
| classes.dex | application code compiled in dex format |
| resources.arsc | file containing pre-compiled application resources, in binary XML |
| res/* | resources not compiled into resources.arsc |
| assets/* | optional - applications assets for AssetManager |
| lib/* | optional folder containing compiled code - i.e. native code libraries. |
| META-INF/ | |
| MANIFEST.MF | stores meta data SHA1 hashes about the contents of the JAR\\ |
| CERT.SF | list of resources and SHA1 digest signed with RSA\\ |
| CERT.RSA | developer RSA public key for signing CERT.SF\\ |
All resources and files of an APK are signed by a developer, the public key in CERT.RSA can be examined using openssl with.
openssl pkcs7 -in CERT.RSA -inform DER -print
During the installation of an APK file on an Android device,the Package Manager verifies the signatures. If modifications have been applied to an APK during debugging or reversing, the APK needs to be newly signed before installation.
Reversing APKs
Some Static Tools
| apktool | decompiling layout, values, resources XML files | https://ibotpeaches.github.io/Apktool/ |
| dex2jar | decompiling dex(Dalvic executable) to a jar file | https://github.com/pxb1988/dex2jar |
| jd-gui | java decompiler and .class viewer | https://github.com/java-decompiler/jd-gui |
| jadx | java decompiler | https://github.com/skylot/jadx |
| Android Studio - APK Analyzer | profile and debug apks | https://developer.android.com/studio/command-line/apkanalyzer |
| Ghidra | NSA tool for reversing (basically dex2jar) | https://ghidra-sre.org/ |
Some Dynamic Tools
| Android Debug Bridge adb | USB debugging | https://developer.android.com/studio/command-line/adb |
| Emulators | f.e AVD Android Virtual Devices in Android Studio | https://androidemulator.org/ |
| bettercap | network analysis | https://www.bettercap.org/ |
| burp suite | mock the app | https://portswigger.net/burp |
| Frida | hook in function call of an .apk | https://frida.re/ |
| Fuzzers [5] | .... |
Hands on Lab
Get the resources a beginners tutorial for apk reversing from the git repository.
git clone https://git.fh-campuswien.ac.at/CampusCyberSecurityTeam/ccst cd ccst/apk_rev_intro
OWASP_app MSTG-Android-Java.apk
Mobile application to learn apk security issues.
- Install app on your phone with adb - try it out
- Unzip MSTG-Android-Java.apk
- Examine the certificate who is subject and issuer?
- Examine classes.dex
- Unpack MSTG-Android-Java.apk with apktool
- What are the app permissions?
- What entry point has the app?
- Examine smali folder
- Use dex2jar to decompile MSTG-Android-Java.apk to a packed .jar file
- Use jd-gui to examine the java classes of the .jar file
Walk through the security app (beginners) or try the CTF challenges (advanced)
Android CTF Challenges
Secrets - easy
Source: TAMUCTF 2019 https://tamuctf.com Can you find my secrets? flagformat: gigem{..}
localnews - medium-hard
Source: TAMUCTF 2019 https://tamuctf.com Be sure to check your local news broadcast for the latest updates! flagformat: gigem{..}
36c3_1337_skills - medium hard
Source: 36c3 It’s too hard to gain all 1337 h4x0r skills required by nowadays CTFs ._.! I am glad a friendly hacker told me about an App he got during a (growth) hacking course. Sadly, he didn’t wrote down any activations codes. Ready for your hacking exam?
Find following codes:
- Activation code
- Sales activation code
- Leadership activation code
- Service Roadmap (SRM) activation code
KGB Messenger - CTF App written for apk Reversing
- Source: https://github.com/tlamb96/kgb_messenger
- APK Download: https://drive.google.com/file/d/14hXB4vXoEk6l-RGJh5B5XRwNhYr1b9bm/view
- Video Lectur: https://youtu.be/m9UZnWLLurY
- Video Walkthrough: https://youtu.be/ddxhuz1bmj4)
- MasonCC: https://competitivecyber.club/
- Introduction
KGB Messenger is a open source CTF practice challenge that aims to help people learn how to reverse engineer Android applications. If you're completely new to Android application reverse engineering, I'd suggest you start by watching the video lecture from George Mason University's MasonCC club. If you're stuck on any of the challenges, feel free to peek at the video walkthrough for some help. Timestamps have been provided in the walkthrough video's description to prevent unwanted spoilers. To get started, download the APK and read the challenge descriptions below.
- Challenges
You are working for the International Secret Intelligence Service as a reverse engineer. This morning your team lead assigned you to inspect an Android application found on the phone of a misbehaving agent. It’s rumored that the misbehaving agent, Sterling Archer, has been in contact with some KGB spies. Your job is to reverse engineer the application to verify the rumor.
The challenges should be solved sequentially. The flag format is FLAG{insert_flag_here}. Good luck!
- Alerts (Medium)
The app keeps giving us these pesky alerts when we start the app. We should investigate.
- Login (Easy)
This is a recon challenge. All characters in the password are lowercase.
- Social Engineering (Hard)
It looks like someone is bad at keeping secrets. They're probably susceptible to social engineering... what should I say?
Used Hardware
Motorola Moto G4 Play Smartphone 16 GB, Android, Dual-SIM, black
Courses
- Campus Cyber Security Team (2020), presentation Media: Ctf_apkreversing.pdf
Online Tutorials
References
- ↑ https://source.android.com/devices/tech/dalvik/jit-compiler
- ↑ https://source.android.com/devices/tech/dalvik/dex-format
- ↑ https://source.android.com/devices/tech/dalvik/dalvik-bytecode
- ↑ https://developer.android.com/studio/command-line/adb
- ↑ https://www.blackhat.com/docs/eu-15/materials/eu-15-Blanda-Fuzzing-Android-A-Recipe-For-Uncovering-Vulnerabilities-Inside-System-Components-In-Android-wp.pdf
Cite error: <ref> tag with name "apktool" defined in <references> is not used in prior text.