MITRE ATT&CK
Developed by MITRE, ATT&CK is a globally accessible knowledge base focused on adversary behaviour - also called cyber threat intelligence . Cyber adversaries are known for their intelligence, adaptability, and persistence, learning from each attack, whether successful or unsuccessful. Their capabilities range from stealing personal information an data to disrupting infrastructure and/or damaging business operations. The MITRE ATT&CK knowledge-base is freely available to everyone. The knowledge base documents the common tactics, techniques and procedures used by cyber threat actors. The framework can be used as a resource for the development of specific threat models and methodologies, as well as the development of specific countermeasures. [1]
MITRE ATT&CK Groups
The groups are "activity clusters" that are often observed in the cyber security bubble under a specific name. It should be noted that groups in the cybersecurity sector are often loosely connected and may be known by several names. In addition, it can happen that the same clusters are tracked by different actors under different names. In the context of the MITRE Groups documentation, the MITRE team endeavours to document the overlaps under the Associated Groups/Aliases section. Groups are in turn linked to techniques that are assigned to the respective tactics. As a result, there is a separate ATT&CK matrix for many groups. [2]
MITRE ATT&CK Software
According to MITRE, software is defined as "operating system utilities, open-source software, or other tools used to conduct behaviour modeled in ATT&CK". Analogous to offender groups, there are also artefacts in the area of software that are known by different names but are the same software. Each entry in the software documentation contains a technical artefact, which in turn can be assigned to a group. The information is based on open source.
MITRE distinguishes between tools and malware: A tool is software that can be used by Defender, Pentester as well as redteamer or threat actors. This includes software that is not found in the corporate context as well as software that is used in the corporate context. In contrast to tools, malware is designed to carry out malicious actions on the targetsystem.[3]
MITRE ATT&CK Techniques
Techniques in the context of the MITRE ATT&CK knowledge base describe how an attacker achieves a tactical objective, i.e. which actions they perform to achieve it. As a striking example, the threat actor can, for example, dump credentials in order to gain access to the victim's credentials. As of January 2023, a total of 201 techniques are documented with a total of 424 sub-techniques. [4]
MITRE ATT&CK Tactics
Tactics documented the why of an ATT&CK technique or sub-technique, it is therefore the actual target of the attacker. The targets reflect the respective process steps of the MITRE ATT&CK matrix - i.e. from reconnaissance to impact. For example, an attacker can use credential access or privilege escalation as a tactic. [5]
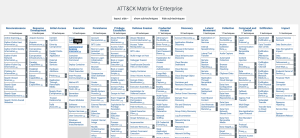
MITRE ATT&CK Matrix
The MITRE ATT&CK matrix is part of the knowledge base and provides actor-specific techniques and procedures for each phase of the attack. The process begins with reconnaissance and ends with impact. Different techniques and tactics are assigned to each process step, which can be clicked on and which then lead to documentation. [6]
In addition to the Enterprise Matrix, there is a matrix for Mobile and one for ICS
Reconnaissance
Reconnaissance involves adversaries actively or passively collecting information to support their targeting efforts an reach their target, which consist in an successfull attack. This gathered informations may include details about the victim organization, its infrastructure, used software or hardware or personnel. Threat actors can utilize this information across different phases of the mentioned process (MITRE ATT&CK Matrix), using it for tasks like planning and executing Initial Access, determining post-compromise objectives, or guiding subsequent Reconnaissance efforts. [7]
Ressource Development
Resource development encompasses methods by which adversaries generate, acquire, or steal resources to support their targeting activities. These resources may include infrastructure, accounts or capabilities. The threat actors can use these resources at different stages of their lifecycle - for example by using purchased or stolen domains for command and control infrastructure, using email accounts for phishing during initial access or acquiring code signing certificates to facilitate defence evasion. [8]
Initial Access
Initial access consists of methods that the attackers use to gain a foothold in the victim's infrastructure. These include spearphishing, content injection or exploiting a vulnerability. A distinction can be made between measures that grant continuous access or temporary access, as passwords change continuously, for example. [9]
Execution
Execution consists of executing the attacker's malicious code on the target system. Techniques from this phase are often combined with techniques from other phases in order to achieve several goals at once. Examples of techniques include the use of a command and script interpreter such as Powershell to execute malicious scripts or user execution of a malicious file. [10]
Persistence
Once threat actors have gained access to the system, they want to maintain access. This is ensured in the course of persistence. The attackers ensure that access is maintained by restarting the system, changing access data and making other changes. An example of this technique is the addition of code during boot or logon autostart execution.[11]
Privilege Escalation
The aim is to ensure higher privileges - higher level permissions on systems and networks - based on the existing access. Higher privileges are often needed to achieve the actual goals. System weaknesses, misconfigurations and vulnerabilities are often exploited to achieve higher privileges. According to MITRE, the target stages are, for example [12]:
- SYSTEM/root level
- local administrator
- user account with admin-like access
- user accounts with access to specific system or perform specific function
Defense Evasion
To avoid the compromise being noticed, use attack techniques of defence evasion. For example, security software can be switched off or uninstalled, or payloads and data can be encrypted and obfuscated. In addition, legitimate processes can be misused to carry out the attackers' activities and thus conceal them. [13].
Credential Access
The aim of the attacker is to steal credentials in order to be able to move laterally in the network, for example. Techniques such as keylogging or credential dumping using Mimikatz are used for this purpose. If the attackers obtain legitimate credentials, it is also much more difficult to track down the attackers in their own systems and networks. [14].
Discovery
In order to obtain further information about the system landscape and the network, the perpetrators observe the digital environment so that they can then plan further steps. They always look at what the attackers can currently control and what they can gain from this or how they can use it to achieve their goals.[15].
Lateral Movement
Lateral movement consists of techniques to compromise other systems in the victim network and make their way through the system landscape to the target. This involves repeatedly gaining access to the various systems that have been discovered. This can be done using own tools for lateral movement or using stolen credentials, which allows the use of native OS tools and is therefore less conspicuous. Examples of techniques include internal spearphishing and remote services such as RDP.[16].
Collection
In the course of the collection, information is gathered as potentially useful sources. The second step after collection often consists of exfiltration, i.e. stealing data. Classic files such as audio, video, email, browsers etc. are often of interest here. Screenshots or keyboard input can also be exfiltrated. [17].
Command and Controll
Command and control is used to ensure that the compromised system can be communicated with in the victim network and can therefore be controlled. An attempt is made to package the C2 traffic in such a way that it imitates normal traffic. For example, different application layer protocols such as FTP, MAIL or DNS can be used for obfuscation. [18].
Exfiltration
Techniques in the exfiltration phase are used to steal data from the victim's infrastructure. Once the data has been collected, it is compressed and encrypted to prevent detection. Subsequently, the transfer between victim and threat actor often takes place via C&C. Exfiltration techniques are i.e. data transfer size limits to avoid detection and, as mentioned, exfiltration over C2 channels. [19]
Impact
Basically, the attackers have at least goal. This target is reached during the impact phase and systems or data are manipulated, disrupted or destroyed. Techniques are used that enable the threat actor to impair the availability or integrity of the business or processes. It should be noted that the symptoms are not always noticed immediately and the objectives can also be achieved without the victim realising it directly. A striking example would be the deletion of an account access or data destruction. [20]
References
- ↑ "MITRE ATT&CK" - available under: https://www.mitre.org/focus-areas/cybersecurity/mitre-attack - Retrieved 2024-01-01.
- ↑ "Groups" - available under: https://attack.mitre.org/groups/ - Retrieved 2024-01-01.
- ↑ "Software" - available under: https://attack.mitre.org/software/ - Retrieved 2024-01-01.
- ↑ "Enterprise Techniques" - available under: https://attack.mitre.org/techniques/enterprise/ - Retrieved 2024-01-01.
- ↑ "Enterprise tactics" - available under: https://attack.mitre.org/tactics/enterprise/ - Retrieved 2024-01-01.
- ↑ "ATT&CK Matrix" - available under: https://attack.mitre.org/# - Retrieved 2024-01-01.
- ↑ "Reconnaissance" - available under: https://attack.mitre.org/tactics/TA0043/ - Retrieved 2024-01-01.
- ↑ "Resource Development" - available under: https://attack.mitre.org/tactics/TA0042/ - Retrieved 2024-01-01.
- ↑ "Initial Access" - available under: https://attack.mitre.org/tactics/TA0001/ - Retrieved 2024-01-01.
- ↑ "Execution" - available under: https://attack.mitre.org/tactics/TA0002/ - Retrieved 2024-01-01.
- ↑ "Persistence" - available under: https://attack.mitre.org/tactics/TA0003/ - Retrieved 2024-01-01.
- ↑ " Privilege Escalation " - available under: https://attack.mitre.org/tactics/TA0004/ - Retrieved 2024-01-01.
- ↑ " Privilege Escalation " - available under: https://attack.mitre.org/tactics/TA0005/ - Retrieved 2024-01-01.
- ↑ "Credential Access" - available under: https://attack.mitre.org/tactics/TA0006/ - Retrieved 2024-01-01.
- ↑ "Discovery" - available under: https://attack.mitre.org/tactics/TA0007/ - Retrieved 2024-01-01.
- ↑ "Lateral Movement" - available under: https://attack.mitre.org/tactics/TA0008/ - Retrieved 2024-01-01.
- ↑ "Collection" - available under: https://attack.mitre.org/tactics/TA0009/ - Retrieved 2024-01-01.
- ↑ "Command and Controll" - available under: https://attack.mitre.org/tactics/TA0011/ - Retrieved 2024-01-01.
- ↑ "Exfiltration" - available under: https://attack.mitre.org/tactics/TA0010/ - Retrieved 2024-01-01.
- ↑ "Impact" - available under: https://attack.mitre.org/tactics/TA0040/ - Retrieved 2024-01-01.