OS Hardening
Summary
In this article the term security is explored and applied to the security requirements of an operating system (OS). A general overview is given on how OS security is defined. Then, the three main sectors on OS security are presented as a high-level overview.
This article also focuses on the following two operating systems:
- Windows operating system
- Linux operating system
OS Hardening
Securing a system completely is a formidable challenge, particularly due to the diverse range of applications that a general-purpose operating system must accommodate. The inherent complexity arises from the limited influence the operating system has over the behavior of third-party programs, given that their source code is usually controlled externally. The primary responsibility of the operating system lies in effectively managing all programs to establish a secure environment for users and applications.
Notably, security measures or checks are often lacking within the kernel, where all components are implicitly trusted, and no procedures segregate different parts of the kernel. This lack of self-defense in kernels makes them vulnerable to exploitation. In the event of a security flaw in the operating system, an attacker exploiting it can gain complete control of the machine through specific software programs. Crafting self-protecting kernels proves challenging, often with a trade-off in performance. Despite these challenges, both Linux and Windows operating systems have their distinct advantages and disadvantages. This article aims to provide an overview of available hardening mechanisms for both Linux and Windows, recognizing their significant roles in everyday computing.
Benefits of OS Hardening
Enhancing the security of your system through OS hardening brings unequivocal advantages. This process not only fortifies your system but also amplifies its overall functionality. By reducing the number of programs and functionalities, the risk of misconfiguration and related issues is minimized.
The primary benefit lies in the substantial improvement of security. A diminished attack surface translates to a lower risk of unauthorized access, hacking, and malware. Simultaneously, the auditability of the system is streamlined. With fewer programs and accounts, auditing the environment becomes more transparent and efficient.
The goal of OS Hardening
The primary objective of OS hardening is to elevate global security standards. Recent analytics indicate that just over 50% of Linux OS users have the latest version installed, while in Windows, only 35% are up-to-date—an indication of the need for more robust patch management. Implementing proactive measures can significantly increase these percentages. One effective strategy is to enhance automatic processes already present in many operating systems. These processes, including core automatic updates, should evolve to ensure critical fixes are promptly applied, even for users who may not proactively manage their updates.
The consequences of insufficient OS Hardening
The gravest consequence of inadequate system security is the occurrence of data breaches. In these scenarios, private personal information for individual users may be compromised, potentially impacting their daily lives. For businesses, such breaches can result in severe repercussions, including financial losses, regulatory fines, and damage to their reputation within their respective industries. For governments, the consequences can extend far beyond trust and reputation damage, potentially jeopardizing the safety and well-being of their citizens, as witnessed in the July 2023 US government hack.
These breaches are often attributable to human error, which can stem from security vulnerabilities within the operating system or associated software. Such vulnerabilities could have been mitigated if users or administrators had regularly applied security updates and patches. One contributing factor to these errors is the lack of proper training for users or administrators.
Security Baselining
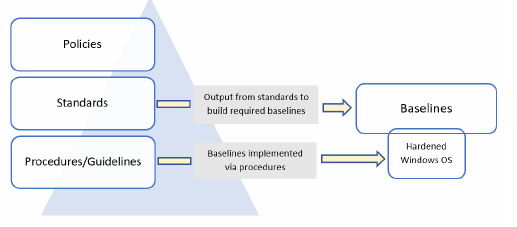
Security baselining is the method of putting a minimal set of guidelines in place and configurations for the environment e.g. establishing a minimal Windows device setup [Dun20]. The creation of a baseline offers a minimally defined norm that will assist in assuring a better secure environment if the organization or the organizational institution deploys systems and devices. Baselines can range from checklists or spreadsheets that someone uses to ensure sure the predetermined security controls have been implemented to a taken snapshot or picture that is already preloaded with the predefined security rules, depending on the size of your business. An aspect of the baseline, it is important to confirm that policies, standards, and processes are in place, are clearly defined, and have received the approval of the leadership and all other stakeholders who are responsible for e.g. data protection. It is essential to have these specified for security, compliance, and auditing reasons. To begin, policies for the firm are to be established and defined. The baselines are then to be constructed using the standards as the framework.
Security Policies, Standards and Procedures
After these baselines are established, policies and procedures is to be developed to apply the baselines and support the achievement of the ultimate result. In the long run, deploying baselines without clear policies, procedures, and a framework is not presumed as effective and leaves the business open to risk. Additionally, having these foundations in place provides a platform with ensuring leadership participation and sign-off, which sends a consistent message to the company about the significance of each associate in its success.[Dun20] It is strongly advised to start with the fundamentals if the business does not already have any rules in place that pertain to, for example, Windows security. In order to protect the devices, at the very least, the following few examples are to be mentioned in a policy [Dun20]:
- Security updates
- Firewall
- Encryption
- A password policy, multi-factor authentication (MFA) and biometrics
A policy that demands that all systems be maintained up to date with the most recent security updates is an example. Policies are followed by standards, which are obligatory and describe the specifics of each policy. In addition to providing details on the technology to be used, standards help maintain consistency within an organization. A few examples of standards regarding windows servers for the proposed elements described in the preceding section include the following [Dun20]:
- Windows Update for Business is to be used to setup all Windows 10 computers, while Windows Servers use either Windows Server Update Services (WSUS) or Azure Update Management. The business use case will specify and store update
schedules.
- On all Windows end-user devices and servers, the Windows firewall is to activate and set up. The connection requirements are to be defined.
- Using BitLocker and/or Azure Disk Encryption, all Windows servers and end-user workstations are to be encrypted.
- PINs and Windows Hello biometrics are to install, and accounts require utilizing passwords with a minimum of 12 characters. Passwords requisite updates yearly and contain capital, lowercase, number, and special characters
The detailed instructions including a step-by-step guide required to complete a repetitive operation or process are known as procedures. These collections or set of guidlines are meant to help with the implementation of the stated policies, standards, and as well as guidelines to achieve a specific aim. Procedures require updates periodically as technology and software versions advance. A third-party tool is also an option with the aim of being more organized and completing procedures. One instance is a program called Nintex Promapp [Pro], which aids in documenting and sharing your company’s procedures [Dun20].
The following four steps are an illustration of a procedure:
- Set up a new Windows 10 device.
- Verify that the device is provided with internet connection.
- Verify the configurations of the device, the device setups, and so on.
- Verify the device’s compliance.
The following figure shows an overview of policies, standards, procedures and baselines and how they are linked to one another [Dun20]:
Linux Hardening
The Linux kernel and operating system present inherent complexities and pose challenges during setup. Despite their intricacies, Linux systems demonstrate remarkable adaptability, where even minor configuration adjustments can exert a profound impact on security. As a result, not all security exposures and vulnerabilities are immediately apparent, and failure to consider the broader consequences of modifying configuration items might result in unintended exposures. Additionally, security in Linux systems is dynamic. The system may not always actually secure once it has been secured by a user, with the notion that a system loses its security over time due to operational or functional changes exposing it to risks, or the discovery of new vulnerabilities in software packages and applications. System security is a continuous and active process[At22]. Finally, many distributions provide a suggested default set of packages, programs, and settings upon setup, often based on the author or vendor's understanding of the distribution's end user needs. For instance, Red Hat is preconfigured to utilize Pluggable Authentication Modules (PAM) packages, programs, and settings upon setup, often based on the author or vendor's understanding of the distribution's end user needs.
Existing Tools and Limitations
System administrators and security teams can record actions carried out, for example, on a Linux system and send them to a central place for storage and analytics, relying to a rather limited set of open source tools. Linux system logs: By default, Linux systems record all system activity for debugging purposes rather than necessarily to help future security investigations. The following logs are provided on Linux systems to assist users to comprehend the various types of operations taking place.
- Syslog and messages : global system activity, including startup messages.
- Auth.log and secure : Security modules like PAM (Pluggable Authentication Module).
- Kern.log : kernel events, errors and warning logs.
- Cron : information about running cron jobs.
- Application specific logs : example /var/log/apache for web server logs.
Logs from the auditing daemon Auditd provide for verbose logging and even the recording of individual syscall usages by the system administrator. Numerous configuration factors, both at the operating system level and the application level, are required for the Linux operating system to be secure.
Windows Hardening
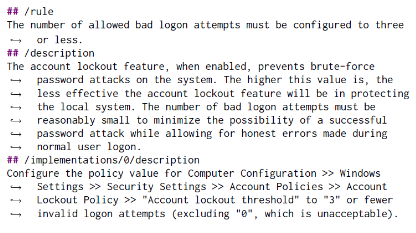
Misconfiguration weaken a system's security by creating vulnerabilities that are frequently hard to find. According to a recent research [CDF18], ignorance and lack of knowledge are the main causes of security misconfiguration from the operators' point of view. Utilizing already-existing security-configuration manuals is one method for overcoming the lack of knowledge. Each rule describes why it should be used and what parameter should be changed to increase system security, as shown in the following figure [SGP20]:
Windows Security Baselines
Microsoft includes suggested settings for hardening Windows systems in its service offerings for Windows security baselines. The following are considered by the Windows security baselines
- Windows 10
- Windows Server
- Office 365 ProPlus
There are more than 3,000 GPO settings for Windows 10 and more than 1,800 for Internet Explorer 11 to offer a better understanding of the complexity of securing Windows. This demonstrates the necessity of utilizing specified baselines to aid harden Windows devices.The following list of Microsoft tools are the ones that are most frequently used to implement these baselines [Dun20]:
- Microsoft Intune
- GPOs
- Microsoft Endpoint or System Center Configuration Manager
Implementing a Baseline - CIS
Once the organization has preferred which baseline controls to implement, it is required to analyze the controls, deploy them throughout the whole organization, and integrate them into the ongoing process. Moving forward with Center for Internet Security (CIS) benchmark [fIS22], it is necessary to download and modify according to the organization's requirements and needs. To make deployment simpler, CIS can also choose to purchase hardened images. The procedures below must be taken in order to download the most recent CIS benchmarks [Dun20]:
- Open a browser and navigate to https://www.cisecurity.org/.
- Click on Cybersecurity Tools.
- Click on Download under CIS Benchmarks.
- Enter the required information, agree to the terms, then click on Get Free Benchmarks Now.
- Go to your mailbox and look for an email from CIS (check your Junk email folder too).
- Open the email and click on Access PDFs. You will be provided with a list of all the available CIS benchmarks in PDF format.
- Scroll down and you will see the Windows Server benchmarks.
- Keep scrolling down and you will also see the Azure benchmarks.
- In addition, there are many more Windows-specific benchmarks for specific roles, such as IIS, SQL, Exchange, and so on.
- Once you have downloaded the PDFs, follow and implement the recommendations on them to strengthen your systems.
Operating System Security Evaluation
Creating a completely secure system is hard if not impossible to achieve. Striving to such a goal gets even harder when dealing with enormous complex systems.
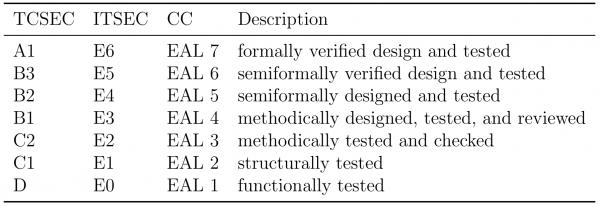
There are three main evaluation criteria for testing and classify computer systems:
- TCSEC: Trusted Computer System Evaluation Criteria
- developed under the United States Government Department of Defense
- ITSEC: Information Technology Security Evaluation Criteria
- published under the Commission of the European Communities
- CC: Common Criteria
- These two standards got unified under ISO/IEC 15408 standard.
These standards classify computer systems on a set of criteria ranging from minimal protection (EAL 1) to verified protection (EAL 7).
To bring these requirements into perspective here is a short list, for common OS classification:
- EAL 4+: Red Hat Enterprise 7.1 (2017), Windows XP (2005), Windows 2008 (2008)
- EAL 3: Apple Mac OS X 10.6 (2009)
- EAL 2: Ubuntu 16.04 (2018)
It has to be noted that the examination takes a long time to conduct and only applies to one specific version. This is one of the reasons why such investigations are performed rarely. Additionally, they are very costly, leading to only a marginal gain for the product.
Common Threats
The main security purpose of an operating system is the separation of user data and applications. Other applications or users should not be able to access data they are not authorized to. The operating system has different techniques for achieving this goal. But before we look into the protection and hardening of an operating system, the most prominent attacks are presented. This list of threats is by no means complete and should only give a brief overview.
- Application Exploit
- Application exploits utilize programming errors to take advantage of the system with the goal in mind to have some kind of privilege escalation and accessing files that should normally not be accessible to a not authorized user.
- Buffer Overflow
- Buffer overflows are a subtype of an application exploit. As they are one of the more common attacks out there we examine them closer. Buffer overflow is the practice of exploiting unprotected size-unrestrained memory buffers. The goal of such an attack is the modification of the return pointer of a program, enabling the attacker to jump to an arbitrary location in memory.
- Race Condition
- Race conditions can occur when concurrent processes can read or write on the same memory location. This attack is also known as time-to-check and time-of-use (TOC/TOU) as a shared value is checked and subsequently used to exploit some kind of software bug.
- For example, an attacker can create a symbolic link to a file in the precise moment a privileged program wants to write to it. If this symbolic link points to \textit{/etc/passwd}, the privilege program unwillingly overwrites the password file, allowing the attacker root access to the machine
- Privilege Escalation
- It is an exploitation technique that grants attackers elevated access to resources typically protected from regular users or programs. This enables them to perform actions otherwise restricted to administrators or software developers. This exploit poses a significant threat, with a track record of effectiveness and a growing popularity in recent years.
- Denial of Service Attacks
- It is an exploitation technique that leverages flaws in network protocol implementations or exhausts a target system’s resources through brute force. Its primary objective is to disrupt normal service provision or block access to resources, potentially causing the target to freeze or even crash.
- IP Spoofing
- It typically entails an attacker attempting to transmit network packets with a falsified IP address to a system, thereby deceiving the recipient. This deceptive practice involves forging the source address of a transmission with the aim of illicitly gaining entry into a secure system. IP Spoofing can be employed for various malicious activities, including launching a Denial of Service (DoS) attack, conducting anonymous port scanning, or deceiving access controls.
- SSH Security Issues
- SSH security issues are often overlooked compared to those of other technologies. This misconception stems from the belief that SSH is inherently secure by default; however, the default configuration of SSH is, in reality, vulnerable. Notably, SSH version 1 should \textit{never} be employed due to its inherent
security risks. Moreover, root user login, username/password logins, weak en- cryption algorithms, and default port settings are among several potential entry points for attackers attempting to breach your system.
- Other Attacks
- There are many more techniques attacking the CIA requirements of an operating system. Many malicious actors attack the confidentiality as it usually has the most value to an adversary.
- Other attacks on the CIA criteria include SQL injections, web exploits, password cracking, denial-of-service attacks, eavesdropping attacks and malware.
Background of attackers
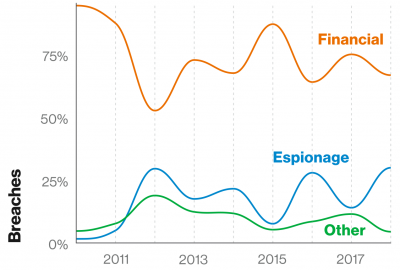
In the 2019 Verizon data breach investigations report shows that the motives of threat actors were 67% financially motivated, 20% espionage driven, 8% for fun and self-esteem related.
Overall Hardening
OS Hardening is one of the instances in which context the overall system can be secured. That means that OS hardening is just focused on the security measurements in the operating system. To have a overview of the whole tree structure a list below will introduce other instances of system hardening.
- Network Hardening
This type of hardening involves securing the basic communication infrastructure of servers and computer systems in a network.
- Physical-Server Hardening
Server hardening involves securing data, ports, components, functions and permission of a server.
- Application Hardening
This type of hardening involves updating or implementing additional security measures to protect standard and third-party applications installed on the server. Unlike server hardening, where the focus is on hardening the entire server system, application hardening focuses on the server´s application specifically.
- Database Hardening
Safe Environments
Even though all applications operate in the same memory and on the same CPU, they should not be able to access files that they are not authorized to.
- Kernel-Enforced Protection
- The kernel does not know the internal functionality of the executing program, therefore it can only modify the layout of the memory and enforce access control rights.
- Memory Access Control
-
- By creating non-executable (NOEXEC) memory spaces. This prevents the execution of injected shellcode in the heap or the stack of an application.
- Memory Address Randomization
-
- Address Space Layout Randomization (ASLR) introduces randomness of the placement in virtual memory. For an attacker it is therefore hard to know where the location of variables, binary, libraries, heap and stack are in memory, as it is different for each execution.
- Compiler-Enforced Protection
- This method tackles the problem during the compilation of the program. The compiler leverages the knowledge it has on the structure of the program and could modify it in the way of securing against buffer overflows.
- Stack Canaries
-
- The compiler can insert special data, called canaries, into different parts of the program memory that get checked during the program execution. If an attacker tries to overflow a buffer, the possibility of overwriting a canary is very high, since they are placed in strategical positions.
For a more practical visualization please visit Buffer Overflows.
Access Control
Access control on an operating system is needed to preserve the confidentiality of a multi-user and multi-application system. The system has to control who is allowed to access, modify and execute certain data.
Access Control List
In Linux basic file access control is based on the traditional UNIX file model. Each file and directory has a total of 9 bits and some special markers to set the permission. The three bits resemble the privilege to read (r), write (w) and execute (x) a given file.
Dividing the access control into three groups can be quite limiting, especially if there are users that need special permissions and is called simple ACL. Maybe we want to grant permissions to additional users or groups. This is where the traditional system becomes quite constricting.
$ ls -l example.txt -rw-r--r-- 1 root root 0 Jan 31 21:32 example.txt
Therefore, the extension for a extended ACL is provided in Linux per default and enables the definition of additional users (named user) and additional groups (named group). Accessing and viewing the extended ACL in Linux is possible with the command getfacl
// view extended ACL $ getfacl example.txt # file: example.txt # owner: root # group: root user::rw- group::r-- other::r-- // modify or add permissions $ sudo setfacl -m "u:someuser:rwx" example.txt $ sudo setfacl -m "g:somegroup:r-x" example.txt $ getfacl eammple.txt # file: example.txt # owner: root # group: root user::rw- user:someuser:rwx group::r-- group:somegroup:r-x mask::rwx other::r-- // view with ls command (note the # that indicates the extended acl) ls -l example.txt -rw-rwxr--+ 1 root root 0 Jan 31 21:32 example.txt // remove permissions $ sudo setfacl -x user:someuser example.txt $ getfacl example.txt # file: example.txt # owner: root # group: root user::rw- group::r-- group:somegroup:r-x mask::r-x other::r-- // view with ls command $ ls -l example.txt -rw-r-xr--+ 1 root root 0 Jan 31 21:32 example.txt
Mandatory Access Control
The aforementioned method of access control is called the Discretionary Access Control (DAC) method and is the most common mechanism to enforce confidentiality. The idea behind DAC is that the owner specifies who can access an object. This decision is based on the owner's discretion.
The so-called Mandatory Access Control (MAC) tries to tackle the problem with a changed fundamental concept. Instead of letting the user decide the permission of objects, each user is given a certain clearance and each object is given a security classification. Only when a user has a higher clearance level as the required security classification (secret, top-secret, confidential) the system allows access.
Well-known implementations in Linux that implement MAC is SE-Linux and AppArmor.
Reducing the Attack Surface
Reducing the attack surface is a vital part of securing the operating system. As seen before we can use access control to prevent flawed applications to breach confidentiality. We should not rely on this technique entirely and should reduce the possible attacks in the first place.
The most common techniques on reducing the attack surface include:
- Removing unnecessary services
- Secure the network (firewalls)
- Securing the hardware (physical)
Best Practices
The most used best practices which are used in many companies are:
- Analyze the OS version and keep it if possible always up to date.
- Prioritize the risks associated with potential vulnerabilities to the operating system.
- Maintain the cleanliness of program and service versions by consistently installing the latest updates. Verify the availability and safety of updates directly from the original source.
- Remove any unnecessary services or programs to minimize the attack surface, as discussed in more detail in the preceding section on the Attacking Surface.
- Establish predefined roles for users and administrators, ensuring alignment with their designated responsibilities. Remove unused user accounts, and consider disabling the guest user account, as it may pose security risks to the operating system.
- Adopt a security strategy by implementing security templates that define minimum security requirements for all users accessing the system. Compliance with these standards is essential for system use.
General Recommendation
For enhanced system security, it is advisable to adhere to these best practices.
Regardless of your operating system, proactively configure your system to minimize the risk of potential attacks. To ensure the trustworthiness of your system, be vigilant about sourcing both hardware and software from reputable and known sources. This guideline extends to additional hardware components, such as external data storage. When acquiring software, opt for direct downloads from the official websites of the developers. If obtaining software from online sources is necessary, always verify its integrity by checking the hash value provided by the developer. To thwart potential man-in-the-middle attacks, prioritize the transfer of software over secure and encrypted channels. Utilizing protocols like TLS not only ensures encryption but also authenticates the issuer, adding an extra layer of security. These measures collectively contribute to a more resilient and secure computing environment.
References
- Seminar paper
- References
- Commission of the European Communities. Information Technology Security Evaluation Criteria (ITSEC): Provisional Harmonised Criteria. Office For Official Publications Of The European Communities, Luxembourg, 1991.
- Luis Franco, Tony Sahama, and Peter Croll. Security Enhanced Linux to Enforce Mandatory Access Control in Health Information Systems. 2008.
- James Graham. Cyber Security Essentials. Auerbach Publications, 2011.
- Andreas Grunbacher. POSIX Access Control Lists on Linux. USENIX Annual Technical Conference, FREENIX Track, 2003.
- Aneesh Kumar, Andreas Grünbacher, and Greg Banks. Implementing an advanced access control model on Linux. 2010.
- Vasudevan Nagendra and Yaohui Chen. Access Control Lists in Linux & Windows. Stony Brook University, 2014.
- P. K. Patra and P. L. Pradhan. Hardening of UNIX Operating System. Int J. of Computer Communication and Technology, 1, 2009.
- Abraham Silberschatz, Peter B Galvin, and Greg Gagne. Operating System Concepts. 2013.
- Peter Silberman and Richard Johnson. A Comparison of Buffer Overflow Prevention Implementations and Weaknesses.
- Verizon. 2019 Data Breach Investigations Report. Technical report, 2019.
- Tevault, Donald A. Mastering Linux Security and Hardening: Secure your Linux server and protect it from intruders, malware attacks, and other external threats. Packt Publishing Ltd, 2018.
- [Dun20] Mark Dunkerley. Mastering Windows Security and Hardening. Packt Publishing, 2020.
- [Pro] Promapp. Business process management - www.nintex.com. Accessed: 2022-11-07
- [At22] Cybersecurity Researchers At. Linux devices ’increasingly’ under attack from hackers, warn security researchers — zdnet. Cybersecurity Researchers, 2022.
- [CDF18] Kevin Borgolte Constanze Dietrich, Katharina Krombholz and Tobias Fiebig. Investigating system operators’ perspective on security misconfigurations. In Proceedings of the 2018 ACM SIGSAC Conference on Computerand Communications Security, 2018.
- [SGP20] Patrick St ̈ockle, Bernd Grobauer, and Alexander Pretschner. Automated implementation of windows-related security-configuration guides. In 2020, 35th IEEE/ACM International Conference on Automated Software Engineering (ASE), pages 598–610, 2020.
- [fIS22] CIS Center for Internet Security. Our mission is to develop and promote timely best practice solutions, www.cisecurity.org. CIS, 2022. accessed: 2022-11-19.
- Donald A Tevault. Mastering Linux Security and Hardening: Protect your Linux systems from intruders, malware attacks, and other cyber threats. Packt Publishing Ltd, 2020.
- Shuangxia Niu, Jiansong Mo, Zhigang Zhang, and Zhuo Lv. Overview of linux vulnerabilities. In 2nd International Conference on Soft Computing in Information Communication Technology, pages 225–228. Atlantis Press, 2014.
- Michael Bartock, Suzanne Lightman, Ya-Shia Li-Baboud, James McCarthy, Karen Reczek, Joseph Brule, Karri Meldorf, Doug Northrip, Arthur Scholz, and Theresa Suloway. Foundational pnt profile: Applying the cybersecurity framework for the responsible use of positioning, navigation, and timing (pnt) services. Technical Report NIST IR 8323r1, National Institute of Standards and Technology, Gaithersburg, MD, January 2023.
- Links
- https://www.redhat.com/en/about/press-releases/red-hat-adds-common-criteria-security-certification-red-hat-enterprise-linux
- https://www.schneier.com/blog/archives/2005/12/microsoft_windo.html
- https://www.niap-ccevs.org/Product/Archived.cfm?par303=Microsoft%20Corporation
- https://www.trentonsystems.com/blog/system-hardening-overview
- https://ubuntu.com/blog/what-is-system-hardening-definition-and-best-practices
- https://www.reuters.com/world/us/chinese-hackers-stole-60000-emails-us-state-department-microsoft-hack-senate-2023-09-27/