Side Channel Attacks
Summary
Side Channel Attacks are attacks on the practical implementation. They are passive and non-invasive and examples of side channels are execution time, electromagnetic radiation and power consumption. You need additional but inexpensive instruments to measure the side channel signals. Different prior knowledge is required depending on the type of attack. Countermeasures are masking and hiding.
Introduction
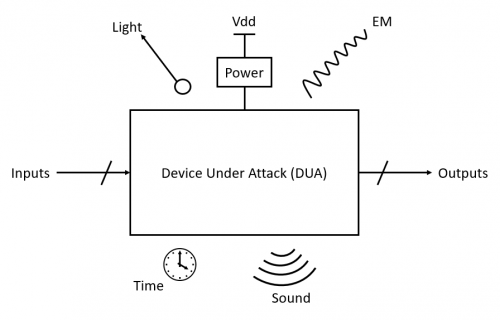
Classical cryptanalytic attacks analyse algorithms mathematically for weak points and vulnerabilities. There is a relatively new type of cryptanalytic attack called implementation attack (the Side Channel Attack is part of it). Instead of attacking the algorithm mathematically, the practical implementation is now the target. This type of attack bypasses the previously installed security mechanisms (e.g. RSA, AES) by also using information emitted by the physical implementation, such as electromagnetic radiation in calculations.
There are two types of implementation attack classifications. First the classification in active (device or environment is changed so that the device shows unnatural behavior) and passive (only signals are used that are sent out for observation under normal conditions). The other way is to distinguish whether the attacks are non-invasive (only information from directly accessible interfaces is used), semi-invasive (modification of the device, but only the outer layers) or invasive (manipulation of the device in every possible way).
Side Channel Attacks are classified as passive and non-invasive implementation attacks.
Side channels are for example execution time, electromagnetic radiation, and power consumption. The attacker tries to find out the secret key by analysing its influence on the side channel signals. Relatively inexpensive basic equipment is required to carry out a Side Channel Attack. A personal computer is sufficient to analyse the side channels. Instruments such as an oscilloscope, spectrum analyser, or electromagnetic antenna are required for the measurement. The attack itself can last from a few minutes to a few hours.[1]
Types of Side Channel Attacks
As there are different side channels, there are of course also different Side Channel Attacks. The best-known Side Channel Attacks are[3]:
- Timing Attacks
- Electromagnetic Attacks
- Power-Monitoring Attacks
- Fault-Injection Attacks
Timing Attacks
The Timing Attack is a Side Channel attack in which the execution time is analysed in order to obtain important information about a device. This is possible because each process is completed after a certain period of time, which depends on the type of process, the input, the characteristics of the environment and the technology used to build the device.
This type of attack is typically used in conjunction with other Side Channel Attacks because more information can be extracted using different analytical methods. The Power-Monitoring Attack, for example, works very well in combination with the Timing Attack. When using these two attacks in conjunction, one recognizes, for example, the order of operations. In this way, the attacker can guess the process currently running on the device and possibly also reconstruct it.[3]
Cache-Timing Analysis
An example of a Timing Attack is the Cache-Timing Analysis. This type of Timing Attack is applied to a process's cache memory. The aim is to measure the times for cache accesses and then use these time values to draw conclusions about which information is currently being processed. This is possible because the time for a cache access can vary in two ways:
- cache hit (the data requested by the processor is available in the cache) and
- cache miss (the data requested by the processor is not available in the cache and must therefore be requested from the main memory).
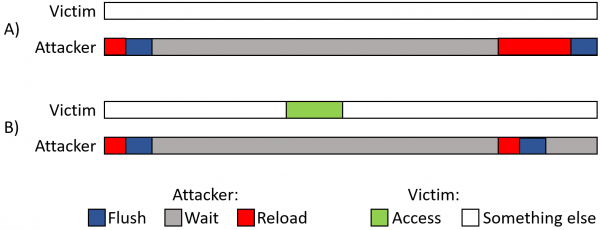
It takes longer to load the data from the main memory than to call up the data directly from the cache. The time difference is used in the Time Analysis to exploit the device. The attacker measures the time by deleting the monitored memory line (smallest administrative unit within the cache of processors) from the cache (FLUSH) and then waits for the victim to request the memory line. In this case it allows access to it (WAIT). The attacker then reloads the memory line and measures the time required for loading (RELOAD). If the victim accesses the memory line (cache) while the attacker is waiting for it, the RELOAD takes less time. If the request has to be answered from main memory, the RELOAD takes considerably longer.[3]
Electromagnetic Attacks
Electromagnetic (EM) signals can be intercepted with sensors such as an antenna. The EM signal is then converted into a current signal from which the noise is removed and the frequency band is limited. The two main types of EM analysis are[3]
- Simple Electromagnetic Analysis and
- Differential Electromagnetic Analysis.
Simple Electromagnetic Analysis
In order to be able to carry out a Simple Electromagnetic Analysis (SEMA), one must have prior knowledge of the architecture or the security policies of the device. The attacker tries to capture and analyse a single EM trace in order to obtain information about the device in this way. The analysis is done visually and the goal is to find a sequence of transitions in the function that contain information about the secret key.[3]
Differential Electromagnetic Analysis
Differential Electromagnetic Analysis (DEMA) is required when the information that needs to be used cannot be analysed visually (i.e. Simple Electromagnetic Analysis is not possible). The analysed signal is compared with an equivalent signal. When the equivalent signal comes from another area of the device, this is called spatial referencing. If the signal comes from a different time, this is called temporal referencing.
Differential Electromagnetic Analysis does not require a lot of knowledge about the compromised device, since most of the information can be learned afterwards during the analysis. This helps to get details about the device such as functionality and structure, which in turn helps to reconstruct the device or to deactivate the security policy.[3]
Power-monitoring Attacks
Power consumption analysis is used to obtain critical information (i.e. the secret key) by analysing the power consumption of a device. The attack is non-invasive, but requires the attacker to have physical access to the device in order to capture the current signals. It is the dominant form of Side Channel Attacks.
Performing such an attack requires a series of current measurements, which can be measured with an oscilloscope. Each current signal that is captured during the analysis is called a power trace. An attacker normally needs a large number of these power traces in order to successfully carry out a Power-Monitoring Attack. After the measurement, the relationship between the power consumption and the secret key is analysed in various ways.
When measuring the power consumption of a device, it is important to be aware that there are two types of power that affect power consumption: dynamic power and leakage power. The first is caused by switching activity of transistors within a device and the second is unwanted behaviour of a transistor. An attacker normally wants to capture dynamic power signals as they directly relate to the functional behaviour of the device. This means that he can use these signals to obtain information about certain operations that are currently being carried out inside of the device.[3]
Simple Power Analysis
Simple Power Analysis (SPA) does not require any advanced or statistical processing stages, but it does require relatively detailed knowledge about the implementation of a cryptographic algorithm to interpret information about the secret key by visually examining the power traces.
Simple Power Analysis is typically used for devices with limited accessibility, as only a few power traces are likely to be available to the attacker. However, for the attack to be successful, the power traces must contain critical information. If multiple power traces are available, the traces can be averaged to remove noise.
The power traces are usually checked visually. They show a sequence of patterns that can help identify key bits, instructions, or functions. This is possible because every command or function creates a specific pattern in the power trace. But to be able to see it, the captured power trace must have a clear pattern (without a lot of noise).[3]
Differential Power Analysis
Differential Power Analysis (DPA) is the most common type of Power-Monitoring Attack and generally the best-known Side Channel Attack. This is because the attacker does not need to have any prior knowledge of the device he is trying to attack. Another reason is that this attack is very effective at capturing high quality signals in environments with high levels of noise. What can be seen as a disadvantage is that it typically requires a larger number of power traces compared to Simple Power Analysis. But that fact also makes it more powerful.
Differential Power Analysis requires two phases: data collection and data analysis (just like SPA). In the data analysis phase, the current traces are analysed statistically (e.g. differences in the mean values).[3]
Correlation Power Analysis
The Correlation Power Analysis is an advanced form of the Power-Monitoring Attack. First, the real power consumption is measured. Hypothetical intermediate values are then calculated, each consisting of a part of an estimated subkey and known data (i.e. plain text). The theoretical power consumption that occurs in the device during the processing of the intermediate value is estimated for each hypothetical intermediate value, e.g. with the help of the Hamming distance. A statistical method is then used to find out which subkey was most likely used by correlating the hypothetical power traces and the actual power traces. The best subkey guesses are then pieced together to get the full secret key.[4]
Template Power Analysis
The Template Power Analysis is a more advanced form of the Simple Power Analysis (SPA). The attacker characterises and saves known and recognized patterns in the power traces as templates. He then compares these templates with the power traces collected from the target device. In this way, he recognizes matches and therefore knows what operations were being carried out when the power traces were measured.[3][5]
Fault-Injection Attacks
The Fault-Injection Attack is a attack where keys/secrets and sensitive information is "stolen" from cryptographic devices or systems by generating faults. Usually the attacker exploits a system that is more prone to being vulnerable due to its higher design complexity and incomplete verification. Voltage glitching, electromagnetic glitching or clock glitching are some of the ways a fault is generated. Fault-Injection Attacks are usually differential, because the output of a faulty operation is compared to a non-faulty operation.[6]
Others
There are also other Side Channel Attacks such as Acoustic and Optical Attacks, but these have not yet been extensively investigated and are therefore not mentioned in more detail here.[3]
Countermeasures
The aim of the countermeasures is to reduce the usable part of the side channel information to a level at which attacks are no longer possible, or at least to a level that would require too many measurements of the side channel. It would of course be much more attractive if you managed to prevent attacks from being possible, but in practice this is very difficult to achieve. A general countermeasure against all types of Side Channel Attacks is to use secret keys and similar sensitive data as rarely as possible (e.g. work with session keys) and to update them as often as possible.
From a technical point of view, the aim of these countermeasures is to remove the dependency between the data values and operations occurring in a cryptographic algorithm and the side channel signals of a cryptographic device. Two basic approaches can be taken to achieve this goal[1]:
- Masking
- Hiding
Masking
When masking is used, all susceptible intermediate values v of a cryptographic algorithm are hidden by a random value m called a mask: v(m) = v ∗ m. The random mask is generated internally by a device as it must not be known to an attacker. All operations performed in a cryptographic device only work with the masked values v(m). The most common masking operations are the XOR function (Boolean masking) and arithmetic operations such as modular addition or multiplication (arithmetic masking). Examples of masking countermeasures are masked look-up tables in software or masked function blocks in hardware.[1]
Hiding
Hiding is an attempt to change the side channel properties of cryptographic devices in such a way that the data processed on a device and the emitted side channel signals can no longer be associated with one another. However, this is usually not perfectly possible in practice. There are two main approaches to implement hiding:
- Randomization, i.e. randomizing side channel signals (e.g. inserting dummy operations randomly or mixing operations) and
- making side channel signals the same (for all operations and data values).
Randomization of side channel signals can be achieved by performing the operations of cryptographic algorithms at different times for each execution (temporal randomization) or by directly increasing the noise level in the side channel signals (randomization in the amplitude dimension).[1]
References
- ↑ 1.0 1.1 1.2 1.3 T. Popp. An introduction to implementation attacks and countermeasures. In 2009 7th IEEE/ACM International Conference on Formal Methods and Models for Co-Design, pages 108-115, 2009.
- ↑ Ken Mai. Side Channel Attacks and Countermeasures, pages 175-194. Springer New York, New York, NY, 2012.
- ↑ 3.00 3.01 3.02 3.03 3.04 3.05 3.06 3.07 3.08 3.09 3.10 3.11 Swarup Bhunia and Mark Tehranipoor. Chapter 8 - side-channel attacks. In Swarup Bhunia and Mark Tehranipoor, editors, Hardware Security, pages 193-218. Morgan Kaufmann, 2019.
- ↑ 4.0 4.1 https://cryptography.gmu.edu/documentation/fobos/cpa.html
- ↑ Suresh Chari, Josyula R. Rao, and Pankaj Rohatgi. Template attacks. In Burton S. Kaliski, cetin K. Koc, and Christof Paar, editors, Cryptographic Hardware and Embedded Systems - CHES 2002, pages 13-28, Berlin, Heidelberg, 2003. Springer Berlin Heidelberg.
- ↑ Y. Li, M. Chen and J. Wang, "Introduction to side-channel attacks and fault attacks," 2016 Asia-Pacific International Symposium on Electromagnetic Compatibility (APEMC), 2016, pp. 573-575, doi: 10.1109/APEMC.2016.7522801.