Difference between revisions of "USB Hacking"
| Line 1: | Line 1: | ||
== Introduction == | == Introduction == | ||
USB attacks have become a significant threat to cyber security. To address this, various tools have been developed to aid in penetration testing and security assessments. The USBNinja cable and OMG cable are two such tools that allow for the execution of payloads when connected to a target device by mimicking a Human Interface Device (HID) such as a keyboard or mouse. These tools can be programmed using the Arduino Integrated Development Environment (IDE) which is user-friendly and straightforward. To prevent USB attacks, a combination of preventive measures such as the Malicious Cable Detector, HID protection approaches through software or hardware, and awareness training is recommended. | |||
== O.MG Cable == | == O.MG Cable == | ||
Revision as of 12:36, 31 January 2023
Introduction
USB attacks have become a significant threat to cyber security. To address this, various tools have been developed to aid in penetration testing and security assessments. The USBNinja cable and OMG cable are two such tools that allow for the execution of payloads when connected to a target device by mimicking a Human Interface Device (HID) such as a keyboard or mouse. These tools can be programmed using the Arduino Integrated Development Environment (IDE) which is user-friendly and straightforward. To prevent USB attacks, a combination of preventive measures such as the Malicious Cable Detector, HID protection approaches through software or hardware, and awareness training is recommended.
O.MG Cable
- Operating system: Ubuntu 18.04 bionic amd64
- Packages: git emacs
In order to complete these steps, you must have followed Some Other Documentation before.
O.MG Cable Setup
Step 1
Enter these commands in the shell
echo foo echo bar
Step 2
USBNinja Cable
The USBNinja cable is a information security and penetration testing tool that allows the execution of payloads when the USB cable is connected by pretending to be a HID device such as a keyboard or mouse. Programming the cable is done through the Arduino IDE, making it a simple and user-friendly method for using USB Ninja.
USBNinja Cable Setup
Step 1
To start with the USB NINJA cable, it is necessary to first access the official website at https://usbninja.com/help/
Step 2
Then, it is essential to strictly follow the steps described on the USBNinja website
Step 3
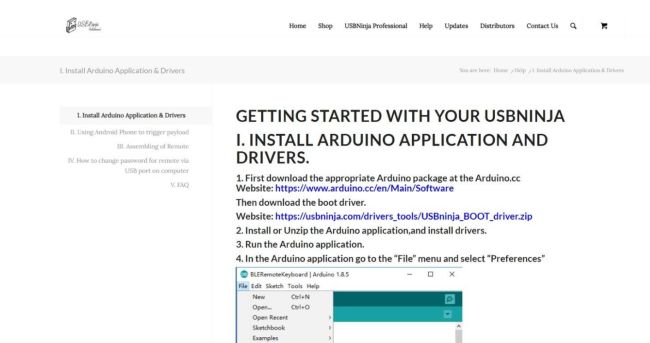
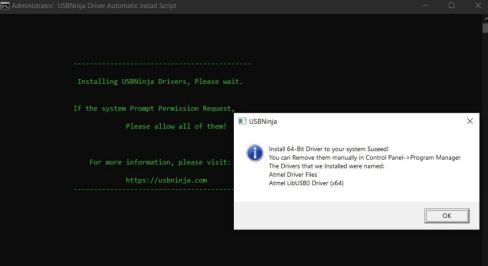
After downloading the required boot driver and the Arduino IDE, it is imperative to run both as administrator to avoid future conflicts and then proceed with the installation
Step 4
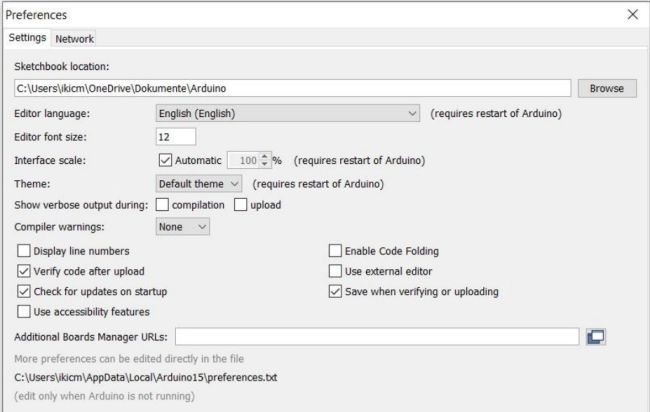
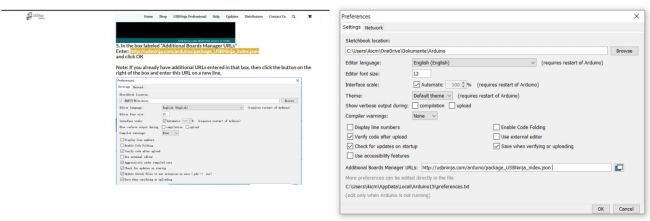
Next, in the Arduino IDE, go to "Preferences" and add the required link
Step 5
The URL for downloading the required JSON file can be easily found on the USB Ninja website. The link simply specifies the location for the download.
Step 6
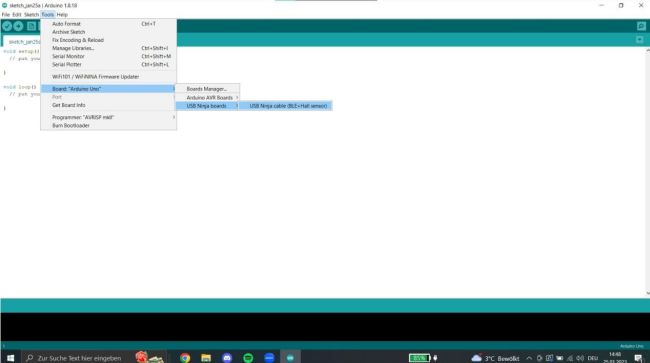
Next, we will open the Board Manager within the Arduino IDE and download the required board for the NINJA cable
Step 7
Finally, we simply select the previously downloaded board for the NINJA cable
Demonstration
Dein OMG Cable Angriff mit der Mail
Scenario
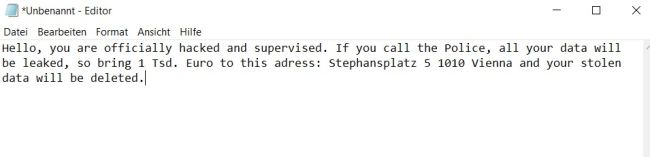
Imagine a hypothetical scenario: Our USB NINJA cable could pose potential dangers. Suppose someone is at an airport and wants to charge their laptop or smartphone. They find a public charging station with USB ports as well as accessible USB cables that can be connected to their laptop. Without thinking, the person connects the charging cable. As soon as the NINJA cable is connected, a threatening message appears on the screen, manipulating the user and causing them to follow the attacker's instructions. This is a typical attack through social engineering.
Preventive measures
Preventive measures against malicious USB cables include the use of a Malicious Cable Detector. This device prevents data transfer through the USB cable while still allowing for charging. The LED on the detector lights up red when data transfer is blocked. There are also two approaches for protecting against HID (Human Interface Device) attacks, a software approach and a hardware approach. The software approach records keyboard activity through software and the hardware approach uses a separate device to record keyboard activity. Awareness training is also an important aspect of protecting against malicious USB cables and HID attacks.