Difference between revisions of "WebGoat"
Jump to navigation
Jump to search
VHorvathova (talk | contribs) |
VHorvathova (talk | contribs) |
||
| Line 23: | Line 23: | ||
</ul></div> | </ul></div> | ||
To gain access to the lessons and challenges, you need to register. | |||
== References == | == References == | ||
<references /> | <references /> | ||
[[Category:Documentation]] | [[Category:Documentation]] | ||
Revision as of 21:07, 8 January 2022
Summary
This is a tutorial and info site on the OWASP's vulnerable web application WebGoat.
Requirements
- Operating system: Kali Linux
Description
WebGoat is a deliberately insecure web application maintained by OWASP designed to teach web application security lessons. It is a demonstration of common server-side application flaws. The exercises are intended to be used by people to learn about application security and penetration testing techniques.[1]
Installation Instructions
- Run via Docker
sudo apt install docker.io sudo docker run -it -p 127.0.0.1:80:8888 -p 127.0.0.1:8080:8080 -p 127.0.0.1:9090:9090 -e TZ=Europe/Amsterdam webgoat/goatandwolf:v8.2.2
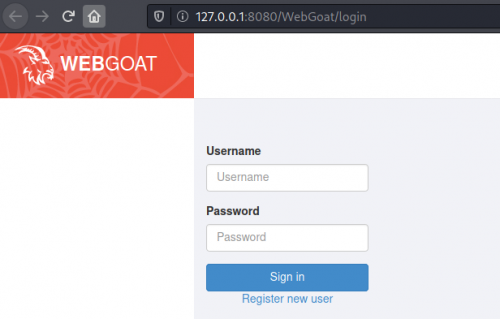
Access
- The landing page will be located at: http://localhost
- WebGoat will be located at: http://localhost:8080/WebGoat
- WebWolf will be located at: http://localhost:9090/WebWolf
To gain access to the lessons and challenges, you need to register.
References
- ↑ WebGoat Github, WebGoat, 2022, accessed on: 08.01.2022. [Online]. Available: https://github.com/WebGoat/WebGoat