Difference between revisions of "Bluetooth Pentesting Tools (HW/SW)"
| Line 42: | Line 42: | ||
=== bluetoothctl === | === bluetoothctl === | ||
Alternatively you can use bluetoothctl: | Alternatively you can use bluetoothctl which is also included in the bluez-utils package: | ||
[[File:Btctl.PNG]] | [[File:Btctl.PNG]] | ||
| Line 51: | Line 51: | ||
Bettercap is a powerful tool for Wifi, Bluetooth LE or ethernet hijacking and provides tools for MITM attacks. Bettercap can also be used to gather informations about bluetooth devices like shown below: | Bettercap is a powerful tool for Wifi, Bluetooth LE or ethernet hijacking and provides tools for MITM attacks. Bettercap can also be used to gather informations about bluetooth devices like shown below: | ||
Start bettercap with: | |||
bettercap | |||
Scanning for BLE devices: | |||
ble.recon on | |||
Show a formatted output of found BLE devices: | |||
ble.show | |||
| Line 66: | Line 78: | ||
=== Wireshark === | === Wireshark === | ||
Alternatively you can capture bluetooth traffic directly with Wireshark. Start Wireshark with | Alternatively you can capture bluetooth traffic directly with Wireshark. Start Wireshark with... | ||
wireshark -w ~/Documents/bttraffic.snoop | wireshark -w ~/Documents/bttraffic.snoop | ||
...and select your bluetooth interface e.g. bluetooth0 or bluetooth1. | |||
[[File:Wiresharkhciscan.PNG]] | [[File:Wiresharkhciscan.PNG]] | ||
Revision as of 18:01, 17 February 2020
Summary
This article describes various tools for bluetooth penetration testing and aims to provide an overview to choose the right tool for a use case.
Requirements
- Operating system: Kali Linux amd64 2019.2
- Packages: Individual shown for each tool
In order to use hardware pentesting devices a dedicated installation of kali linux is recommended but it is also possible to use hypervisors which are capable of passing USB devices from the host- to the guestsystem e.g. VMWare Workstation or the free hypervisor VirtualBox.
Information gathering
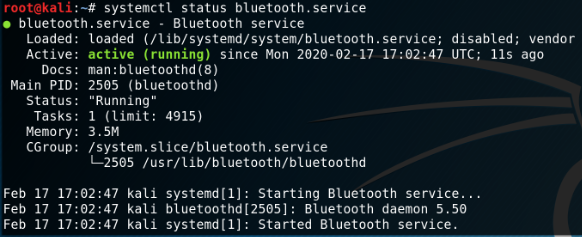
The offical linux bluetooth protocol stack BlueZ is already installed on kali linux but can be installed on other linux maschines with:
apt install -y bluez bluez-utils systemctl start bluetooth.service systemctl status bluetooth.service
hcitool
To start with penetration testing we need to gather information about our environment, for this purpose scan for available bluetooth devices with the included packages 'hcitool' or 'bluetoothctl'.
First check if your bluetooth device is available:
hciconfig
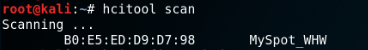
Scan for BR/EDR Bluetooth devices with hcitool:
hcitool scan
In order to scan for BLE devices use:
hcitool lescan
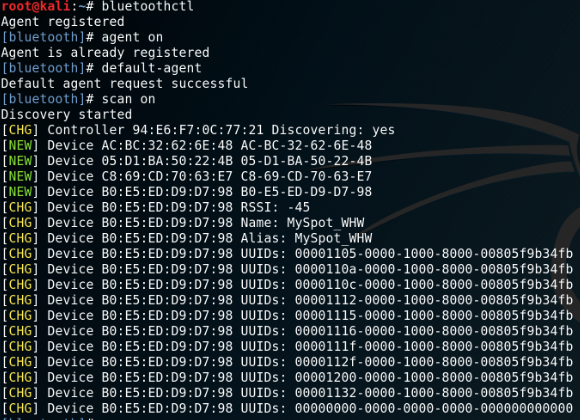
bluetoothctl
Alternatively you can use bluetoothctl which is also included in the bluez-utils package:
bettercap
In order to complete these steps, you must have followed Install_Bettercap_on_Kali_Linux before.
Bettercap is a powerful tool for Wifi, Bluetooth LE or ethernet hijacking and provides tools for MITM attacks. Bettercap can also be used to gather informations about bluetooth devices like shown below:
Start bettercap with:
bettercap
Scanning for BLE devices:
ble.recon on
Show a formatted output of found BLE devices:
ble.show
Capturing bluetooth traffic
btmon
With the preinstalled package 'btmon' it is possible to capture traffic between the HCI and the controller:
btmon --write ~/Documents/bttraffic.snoop
These files can be viewed and analysed with 'Wireshark' which is also preinstalled on kali linux.
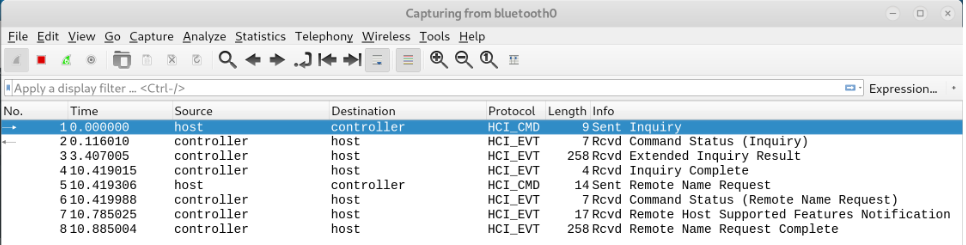
Wireshark
Alternatively you can capture bluetooth traffic directly with Wireshark. Start Wireshark with...
wireshark -w ~/Documents/bttraffic.snoop
...and select your bluetooth interface e.g. bluetooth0 or bluetooth1.
Bluetooth Pentesting Software
Bluetooth Pentesting Hardware
For hardware pentesting devices like the Ubertooth one please see following documentations:
Another BLE penetration testing example with the powerful GATT Tool can be found here: