OWASP Mutillidae (2021)
Summary
OWASP Mutillidae is a free open source tool created for Pentesting of Web Applications. It is a "Vulnerable Web Application" that offers a Platform where the provided Exploits and Security flaws can be executed within a local environment. With over 40 different vulnerabilities and related training challenges, it provides a platform that shows the most common flaws of the last 15 years of web development. The main goal is to to offer security training for a wide range of uses, from teaching in classrooms to security enthusiasts exploring to functioning as testing ground for vulnerability assessment targets. The vulnerabilities shown in the program are actual vulnerabilities within the application, so the application should only be run in a protected environment - such as a virtual machine. Most of the Vulnerabilities are structured around the OWASP Top Ten List[1]. The current Version Mutillidae II was created by Jeremy Druin [2] (pseudonym: webpwnized), who also created the Tutorials for the Challanges and Installation Guides.
How it Operates
Every Vulnerability contained in the application is build in within a Webpage. By selecting the Exploit from a List (e.g. Authentication Bypass) a site with the corresponding explotable Webpage is loaded and ready to get "hacked". Since everything run at your local machine you can not harm anyone. The data such as "User Data" are stored in a Database which you set up when you install the Application (see Installation for more Information).
A1 SQL Injection Example
SQL_Injection-> SQLi Extract Data
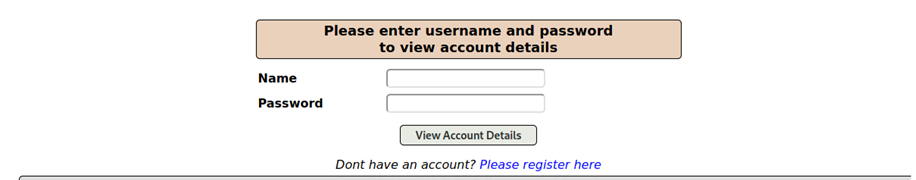
Now here is a short example how one vulnerability exploit could look like. In this case there is a query where user can request their userinformation by providing their credentials.
Normally the query should only retrun only on record when correct credentials are entered.
But this website is totally unsecure so we can easily rewrite the SQL query to give us a list of every user in the database. But how can we do this?
Step 1:
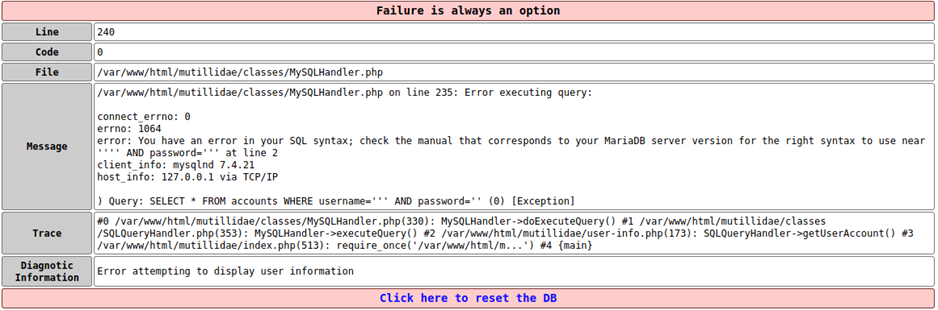
get an Exception by typing in invalid characters such as (', #, --)
Step 2:
Since we got an error message with the syntax how the sql statement is written we can alter the statement by simply put another statement in the form.
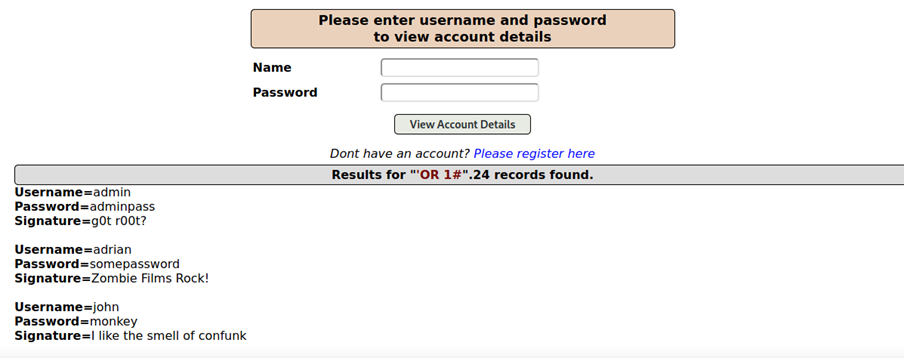
In this case i wrote ’OR 1# in the username fields to alter the query which should be now
SELECT * FROM acccounts where username= ’ ’OR 1# AND password = ’’
1 means true in SQL language and # is a comment so it ignores the password query. So our SQL String says now that it should gives as all datasets for which the condition is true which lead to following output:
A5 Cross-Site-Request Forgery Example
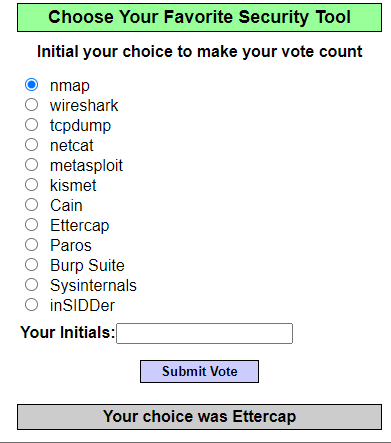
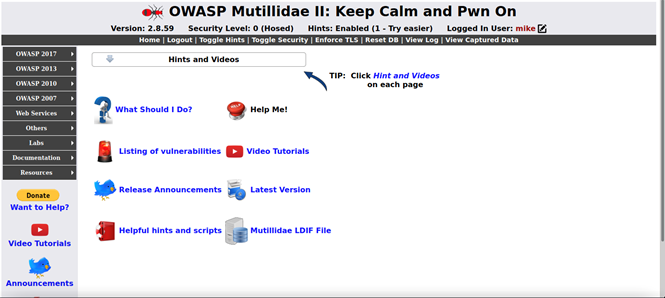
Cross-Site-Request_Forgery_(CSRF)-> Cross-Site-Request Forgery This example can be found in the A5 section from the Owasp Top 10 examples, which is called 'Add to your blog'. Here we simulating an attack to vote for a security tool but without actually voting for it. In the screenshot below you can see the site which we are attacking. So this site is basically the good site.
The evil site is in this case the 'Add to your blog' site. Users can save a blog to a blog table. An attacker can you use this mechanism to manipulate a blog to fire an action. Instead of a normal blog you can also add a script to the blog table. This script calls a method when you hover over the blog and it redirects to the voting site and votes for a security tool.
The script can be found on the official github website for Mutillidae https://github.com/webpwnized/mutillidae/blob/master/labs/lab-files/cross-site-request-forgery-lab-files/vote-for-nmap-onmouseover-csrf.txt This script creates a form object in the background and sets some specific fields. Those fields are being sent over the URL to the voting site. Because how the site is constructed, it reads the parameter from the url to decide which security tool should be voted. This means that the form object consists of some input fields and those input fields contain some values. One input field is responsible for redirecting to the voting site. The other one is setting the value for security tool. A form also should have a submit button which is also set with the input fields. This whole script is contained in a method. This method gets fired when you hover over the mouse. You basically save a html tag with the name of the blog but this html tag calls the method which is containing the malicious script.
Features
- over 40 vulnerabilities (OWASP Top Ten 2007, 2010, 2013 and 2017[3])
- Actually Vulnerable
- Simple Intallation and Maintaining
- User can switch between 3 security levels (no security, Client-side Security, Server-side Security)
- Used in web security courses
- Tutorials and Guides included in Application
- Updated frequently
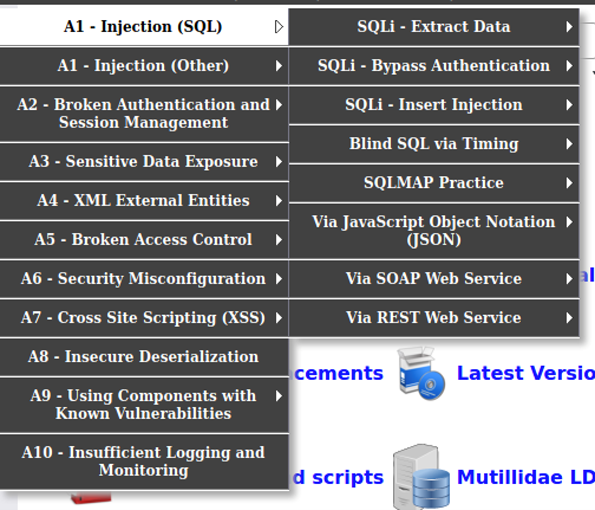
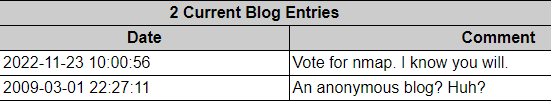
Interface
By clicking on any Item on the right dropdown menu, you can select any of the OWASP Top Ten Challanges from the last 15 years.
- Hints and Videos - leads you directly to a structured guide how the exercise could be completed.
- Toggle Security - you can choose between 3 Security levels for each exercise
- Reset DB - Clear all user Data
- Labs - Study Questions associated with the Exercises
Examples of Vulnerabilities
- SQL Injections (SQLi)[4]
- Cross-Site-Scripting [5]
- Sensitive Data Exposure
- other Injection (CSS, HTML, JavaScript)
- and many more...
Comparable Vulnerable Web Applications
Requirements
- Apache Webserver
- Database (MySQL/MariaDb)
- Packages: Sourcecode from git (https://github.com/webpwnized/mutillidae)
Installation
- Install Apache Webserver on your local Machine
- Install PHP on your local Machine
- Install a supported Database (e.g. MySQL, MariaDB)
- Install Metasploit, it includes everything you need to run mutillidae
If you have a XAMPP/LAMPP stack set up aleady, you might skip directly to installing Mutillidae. Alternativly you can also use a docker build to run Mutillidae. There are Videos from the creator which gives a Step-by-Step video tutorial
Installing Mutillidae
Head to the Folder where Websites are stored in Apache Webserver this could be the "htdocs" folder under XAMPP or if manually installed under a linux distribution this might be the folder "/var/www/html/"
Download the Repository from github (see #Requirements) and copy the contents of the Repository into the Webservers folder. After these steps go on your localhost webpage and make sure you can access Mutillidae Webinterface
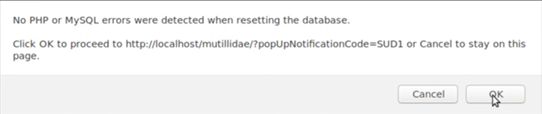
To see if the database is correctly installed press the "Reset DB" Button on the Webinterface. If you see the Message that no PHP or SQL errors were detected when resseting the database, the intallation of mutillidae succeded.
Installing Mutillidae with Metasploit
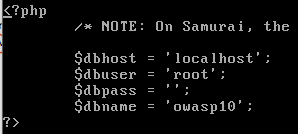
A different method for installing Mutillidae is to install Metasploit. Metasploit is a penetration testing software which inlcudes everything you need to set up and run Mutillidae. This means that you don't have to install all the other components you need for example a database, because Metasploit is doing this for. After installing you can use the credentials msfadmin for the username and password in order to login into Metasploit. When Metasploit is running Mutillidae is also accessible and for that you use the ip address of the machine where Metasploit is running on. To look up the ip address you can use the 'ip a' command in the CLI to find the ip address. Sometimes it happens that Mutillidae cannot access the database. This problem occurs when the database name in the config file is not set. To fix this problem you have to navigate to this config file which is found in this destination '/var/www/mutillidae/config.inc'. In this config file you change the value of the variable called '$dbname' to 'owasp10'. After this configuration Mutillidae can access the database.
References
- https://owasp.org/www-project-top-ten/
- https://github.com/webpwnized/mutillidae
- https://www.youtube.com/c/webpwnized/featured
- https://github.com/webpwnized/mutillidae/blob/master/README-INSTALLATION.md Step-by-Step video tutorial
Internal Links